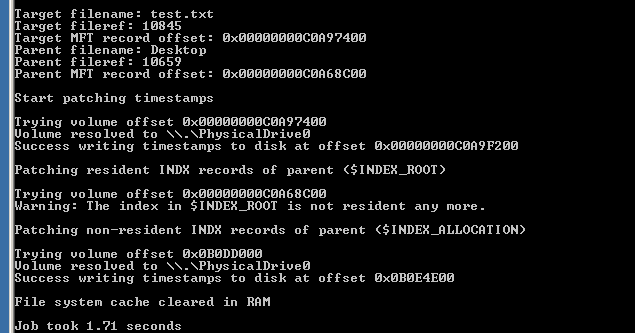
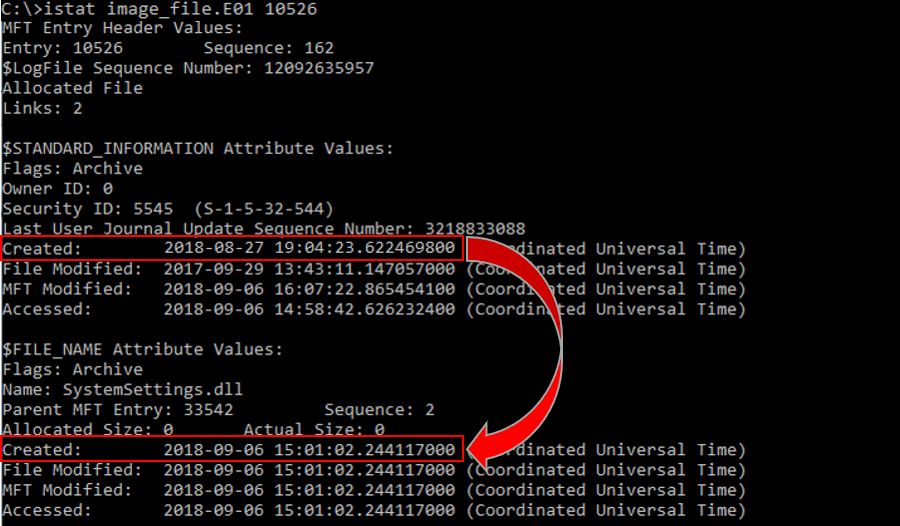
Detecting Linux Anti-Forensics: Timestomping
Por um escritor misterioso
Last updated 27 março 2025
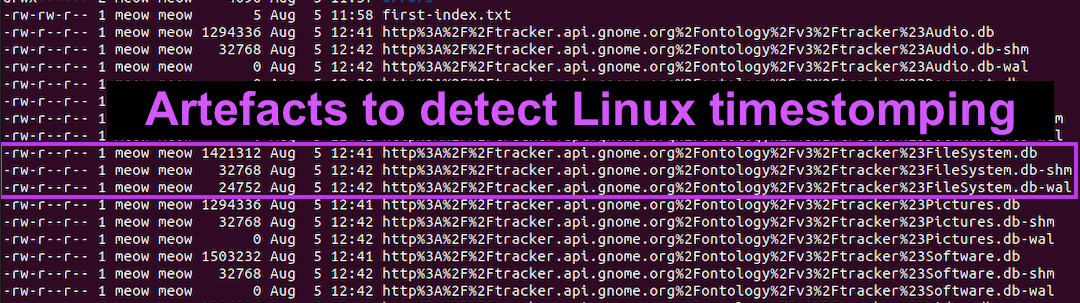
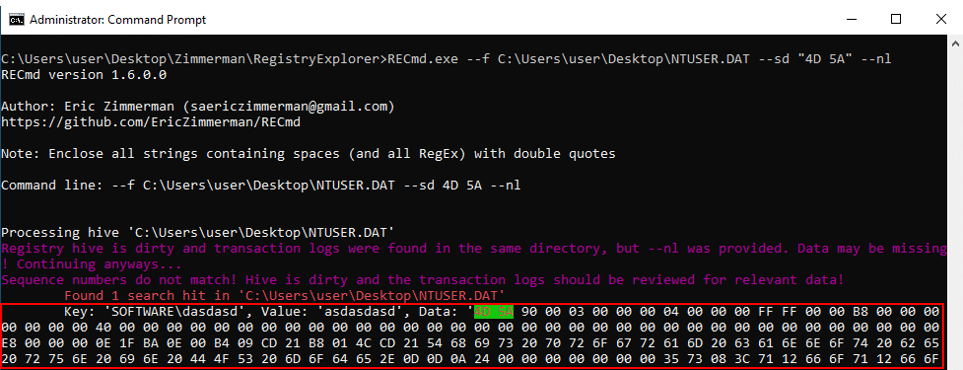
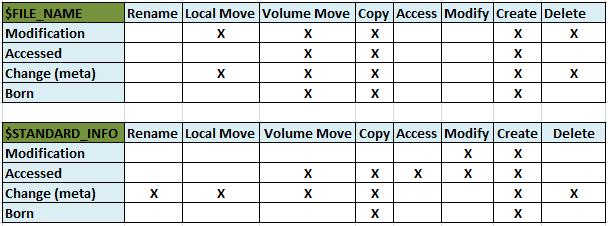
#160; Threat actors can modify the timestamps on malicious files to evade detection. This technique has been used time and time again across va
inversecosᵘʷᵘ's Threads – Thread Reader App

Detecting Linux Anti-Forensics: Timestomping
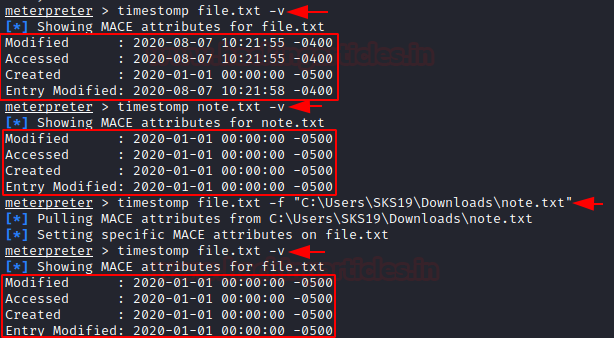
Anti-Forensic: Swipe Footprint with Timestomp - Hacking Articles

Anti-forensics Securing Network Infrastructure
Anti-Forensics Techniques - Cynet
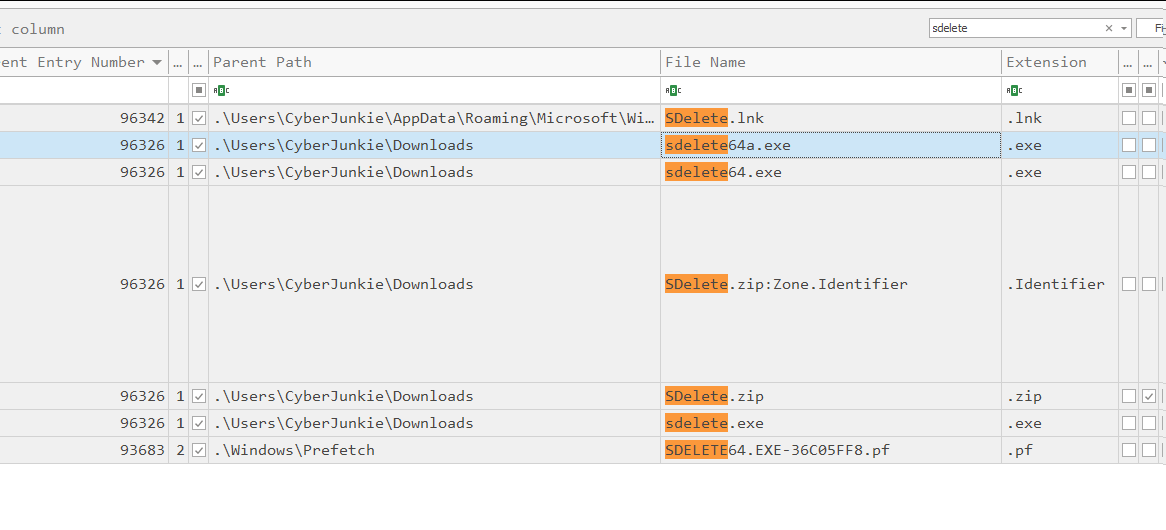
5 anti-forensics techniques to trick investigators (+ examples
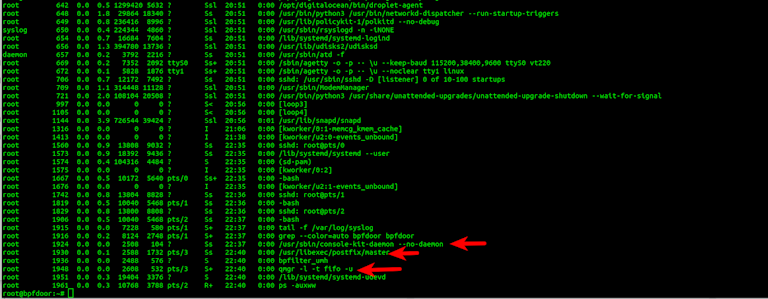
BPFDoor - An Evasive Linux Backdoor Technical Analysis
Anti-Forensics Techniques - Cynet

Anti-forensics: Furthering digital forensic science through a new

Lina L. en LinkedIn: Detecting Linux Anti-Forensics: Timestomping

PDF) Detection and Mitigation of Anti-Forensics
SANS Digital Forensics and Incident Response Blog
Recomendado para você
-
![OP Evade Script GUI [FREE]](https://vapouryt.co.uk/wp-content/uploads/2022/09/evade-script.jpg) OP Evade Script GUI [FREE]27 março 2025
OP Evade Script GUI [FREE]27 março 2025 -
 NEW BEST Evade SCRIPTS Mobile And Pc, ALL FEATURES27 março 2025
NEW BEST Evade SCRIPTS Mobile And Pc, ALL FEATURES27 março 2025 -
 Roblox Evade Script Pastebin Hacks - December 202327 março 2025
Roblox Evade Script Pastebin Hacks - December 202327 março 2025 -
 Hackers Using New Obfuscation Mechanisms to Evade Detection27 março 2025
Hackers Using New Obfuscation Mechanisms to Evade Detection27 março 2025 -
 Netflix Clone - Video Streaming App - Launch OTT Platform - Develop The Most Sophisticated Netflix Clone With AiOC- Netflix Clone Script - SideProjectors27 março 2025
Netflix Clone - Video Streaming App - Launch OTT Platform - Develop The Most Sophisticated Netflix Clone With AiOC- Netflix Clone Script - SideProjectors27 março 2025 -
Joel Lambert27 março 2025
-
 Seriously? Helping trouble-makers to evade moderation? : r/discordapp27 março 2025
Seriously? Helping trouble-makers to evade moderation? : r/discordapp27 março 2025 -
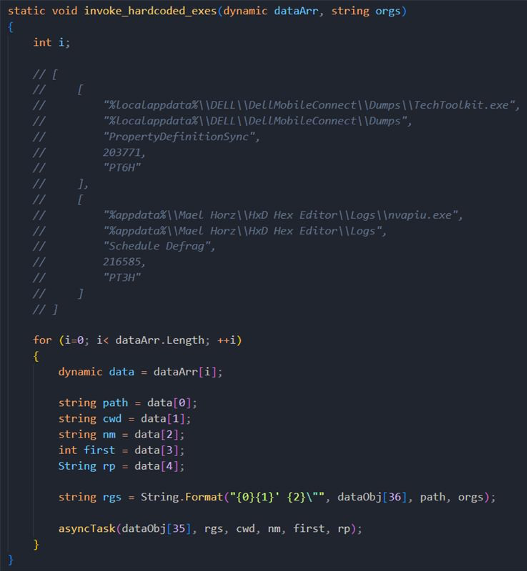
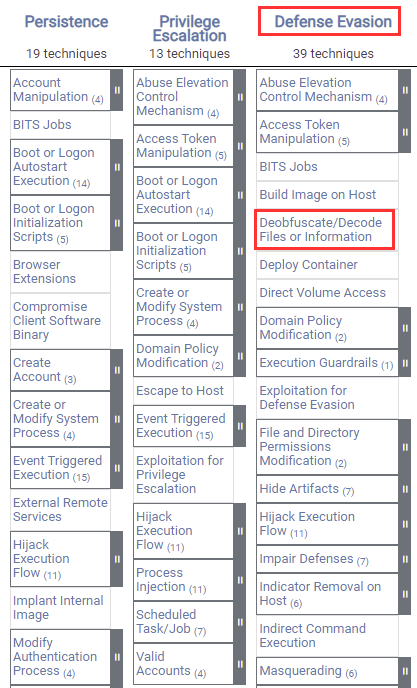 Windows Red Team Defense Evasion Techniques27 março 2025
Windows Red Team Defense Evasion Techniques27 março 2025 -
 Buy, Sell, Steal, EvilNum Targets Cryptocurrency, Forex, Commodities27 março 2025
Buy, Sell, Steal, EvilNum Targets Cryptocurrency, Forex, Commodities27 março 2025 -
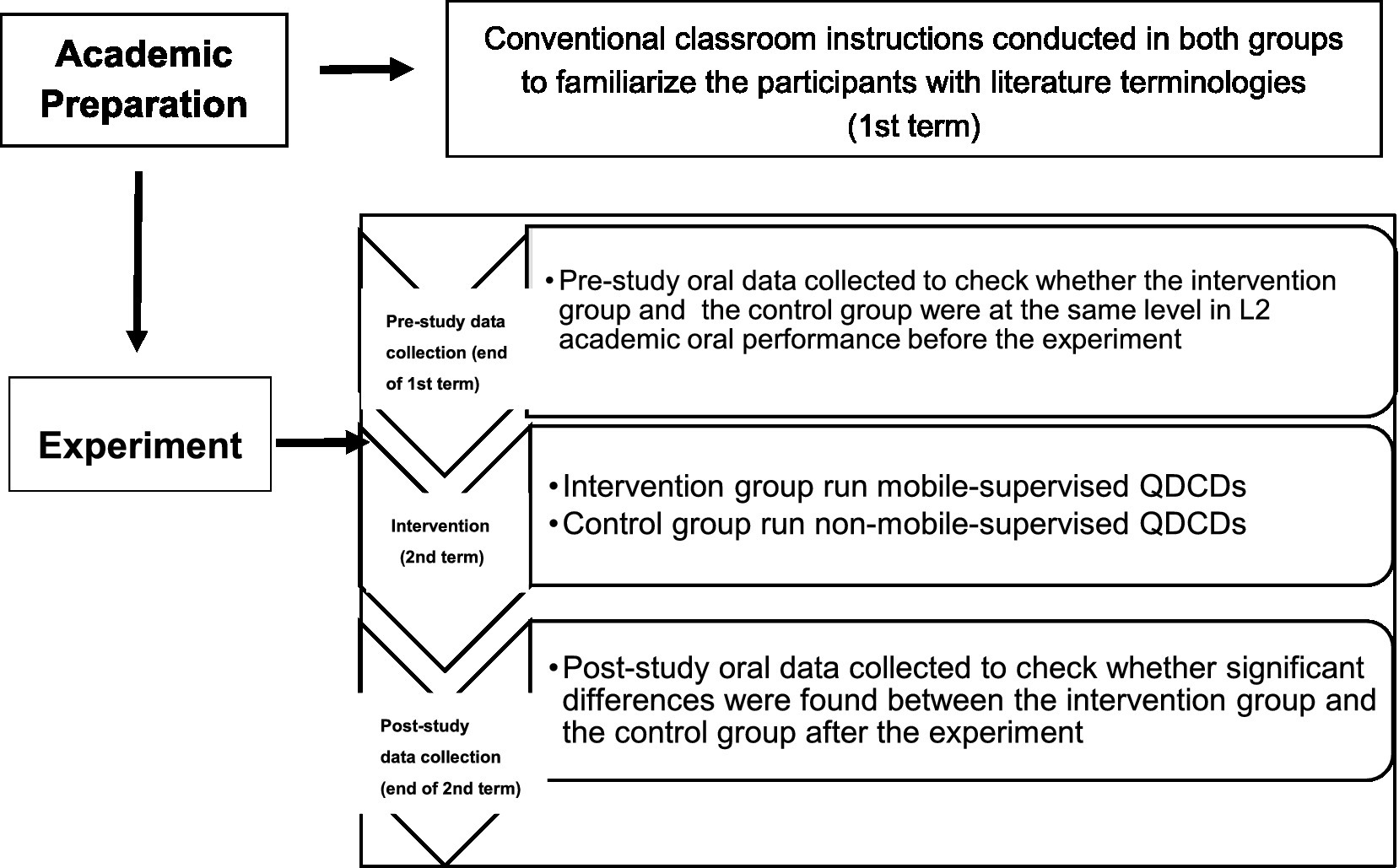 Frontiers Effects of mobile-supervised question-driven collaborative dialogues on EFL learners' communication strategy use and academic oral English performance27 março 2025
Frontiers Effects of mobile-supervised question-driven collaborative dialogues on EFL learners' communication strategy use and academic oral English performance27 março 2025
você pode gostar
-
 Novo monstrinho faz sua estreia no jogo Pokémon Go; confira qual é27 março 2025
Novo monstrinho faz sua estreia no jogo Pokémon Go; confira qual é27 março 2025 -
 outro novo animatronic criado por mim fnar - Desenho de bonnie_fofinho_ - Gartic27 março 2025
outro novo animatronic criado por mim fnar - Desenho de bonnie_fofinho_ - Gartic27 março 2025 -
 Camiseta Camisa Nanatsu No Taizai Meliodas Anime Nerd Filme27 março 2025
Camiseta Camisa Nanatsu No Taizai Meliodas Anime Nerd Filme27 março 2025 -
 Mafia Town Gangster Transport Criminal Mind Ganglands Hard Time27 março 2025
Mafia Town Gangster Transport Criminal Mind Ganglands Hard Time27 março 2025 -
 Just Dance 2020 - Nintendo Switch - Compra jogos online na27 março 2025
Just Dance 2020 - Nintendo Switch - Compra jogos online na27 março 2025 -
 Rodojr Transportes - São João da Boa Vista em São João da Boa Vista, SP, Transportadoras27 março 2025
Rodojr Transportes - São João da Boa Vista em São João da Boa Vista, SP, Transportadoras27 março 2025 -
 Dough Combo, Easy One-Shot Combo27 março 2025
Dough Combo, Easy One-Shot Combo27 março 2025 -
 Obi Wan Kenobi - Qui Gon Jinn Art Wallpaper Download27 março 2025
Obi Wan Kenobi - Qui Gon Jinn Art Wallpaper Download27 março 2025 -
 Intruder in the Dust (1950) - Turner Classic Movies27 março 2025
Intruder in the Dust (1950) - Turner Classic Movies27 março 2025 -
![Salto de Paraquedas! GTA V [PT-BR]](https://i.ytimg.com/vi/r4Uw50uiwIE/maxresdefault.jpg) Salto de Paraquedas! GTA V [PT-BR]27 março 2025
Salto de Paraquedas! GTA V [PT-BR]27 março 2025
