Malware analysis Malicious activity
Por um escritor misterioso
Last updated 27 março 2025

Malware analysis metasploit.bat Malicious activity

Malware Analysis: Steps & Examples - CrowdStrike
GitHub - mesquidar/ForensicsTools: A list of free and open forensics analysis tools and other resources

The latest malicious activity and how to deal with it

PROUD-MAL: static analysis-based progressive framework for deep unsupervised malware classification of windows portable executable

An Elastic approach to large-scale dynamic malware analysis — Elastic Security Labs

Interactive Online Malware Sandbox

Routers Roasting on an Open Firewall: the KV-botnet Investigation - Lumen

Unveiling activities of Tropic Trooper 2023 deep analysis of Xiangoop Loader and EntryShell payload

Web injections are back on the rise: 40+ banks affected by new malware campaign

Robust Malware Detection Models: Learning From Adversarial Attacks and Defenses - Forensic Focus
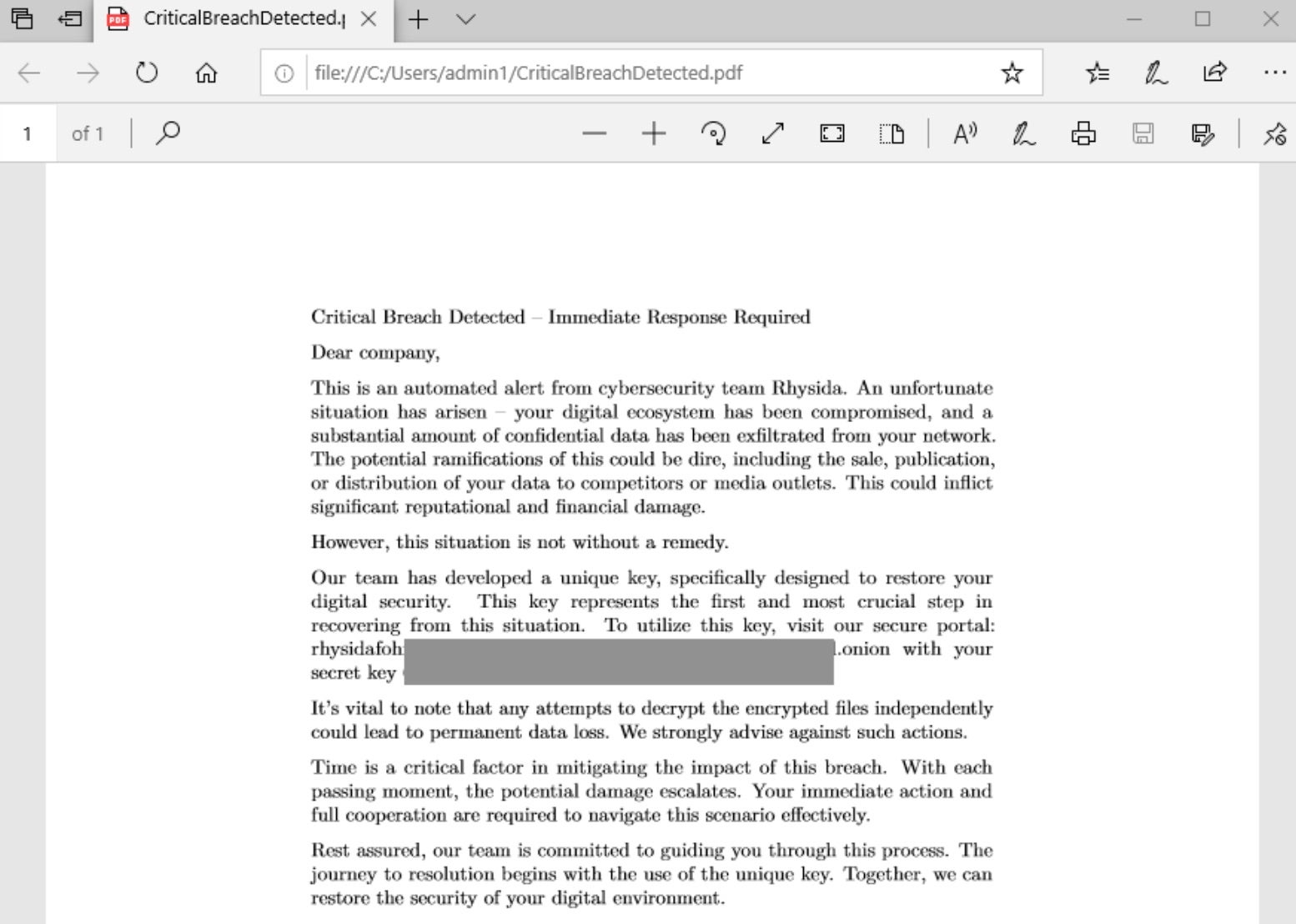
Rhysida - SentinelOne
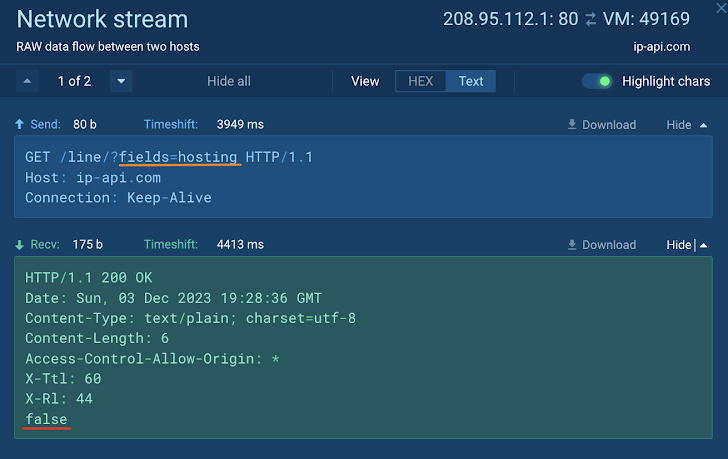
How to Analyze Malware's Network Traffic in A Sandbox

How to build a malware analysis sandbox with Elastic Security
Recomendado para você
-
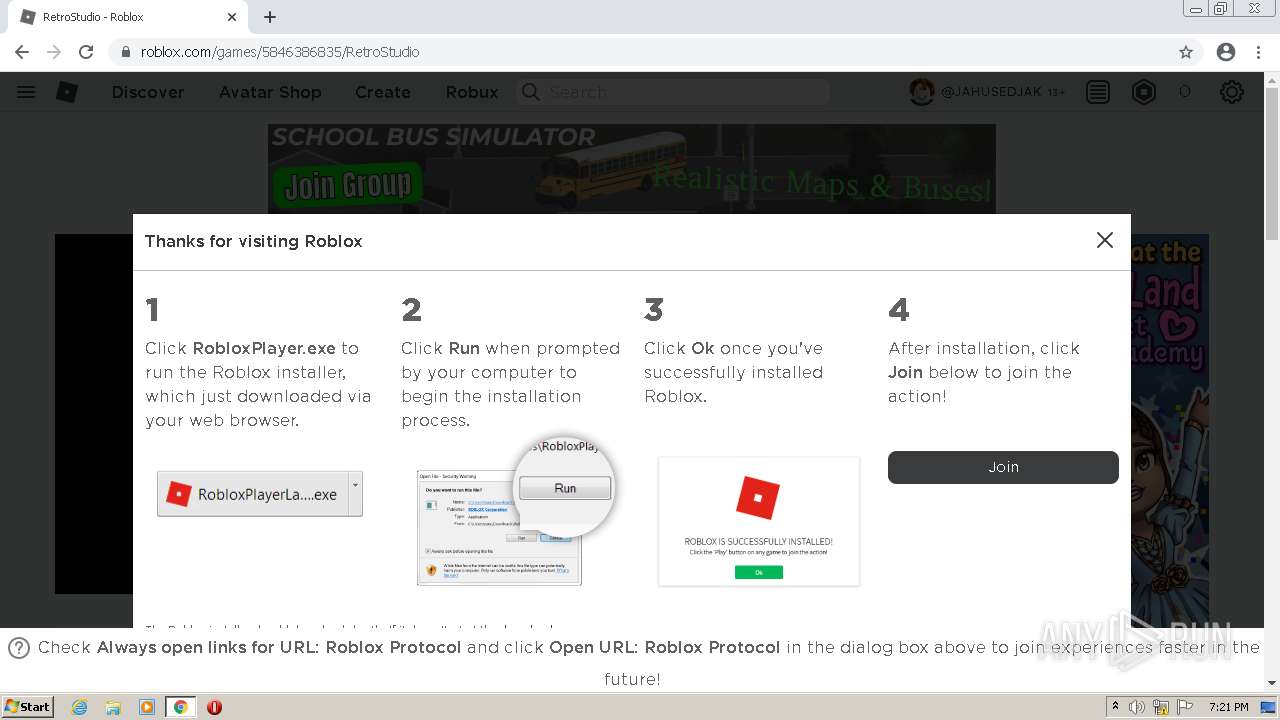
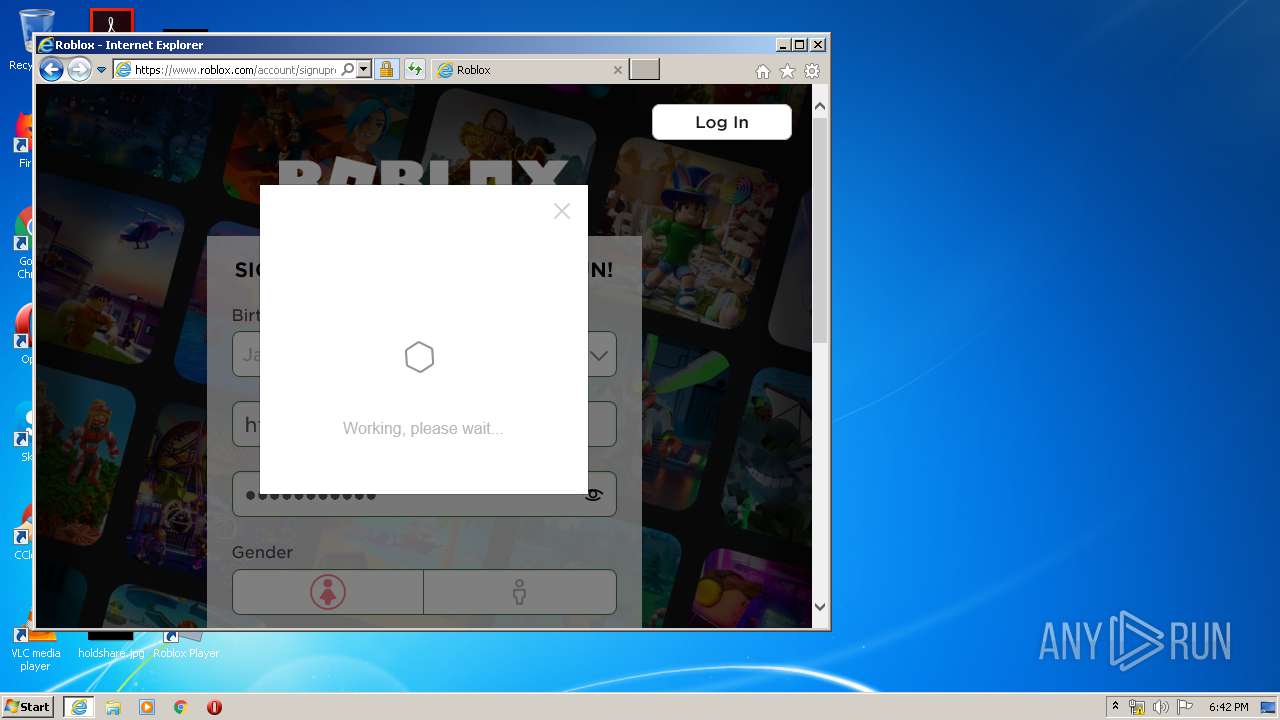
 How To Download Robloxplayer.exe & Play Roblox Games27 março 2025
How To Download Robloxplayer.exe & Play Roblox Games27 março 2025 -
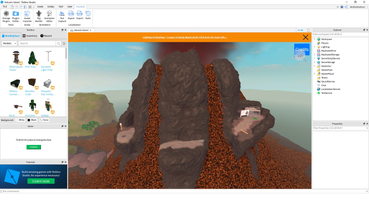 Roblox Studio for PC Windows 1.6.1.9670 Download27 março 2025
Roblox Studio for PC Windows 1.6.1.9670 Download27 março 2025 -
 Malware analysis RobloxPlayerLauncher.exe Malicious activity27 março 2025
Malware analysis RobloxPlayerLauncher.exe Malicious activity27 março 2025 -
 RobloxPlayer.exe - Download & Play Roblox Games (2023)27 março 2025
RobloxPlayer.exe - Download & Play Roblox Games (2023)27 março 2025 -
 RobloxPlayerBeta.exe not working with a game capture in OBS - Platform Usage Support - Developer Forum27 março 2025
RobloxPlayerBeta.exe not working with a game capture in OBS - Platform Usage Support - Developer Forum27 março 2025 -
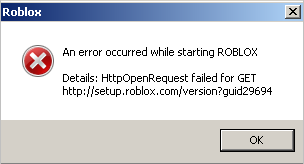 robloxplayer.exe error. : r/PhantomForces27 março 2025
robloxplayer.exe error. : r/PhantomForces27 março 2025 -
 Malware analysis Malicious activity27 março 2025
Malware analysis Malicious activity27 março 2025 -
 How to use the Roblox App Beta (Mac & Windows) - Community27 março 2025
How to use the Roblox App Beta (Mac & Windows) - Community27 março 2025 -
 GitHub - Malte0621/Roblox-Player-Mod-Manager: An open-source custom bootstrapper for Roblox Player that allows you to override files in Roblox Player's directory, opt into development branches of Roblox, and experiment with Fast Flags. Based27 março 2025
GitHub - Malte0621/Roblox-Player-Mod-Manager: An open-source custom bootstrapper for Roblox Player that allows you to override files in Roblox Player's directory, opt into development branches of Roblox, and experiment with Fast Flags. Based27 março 2025 -
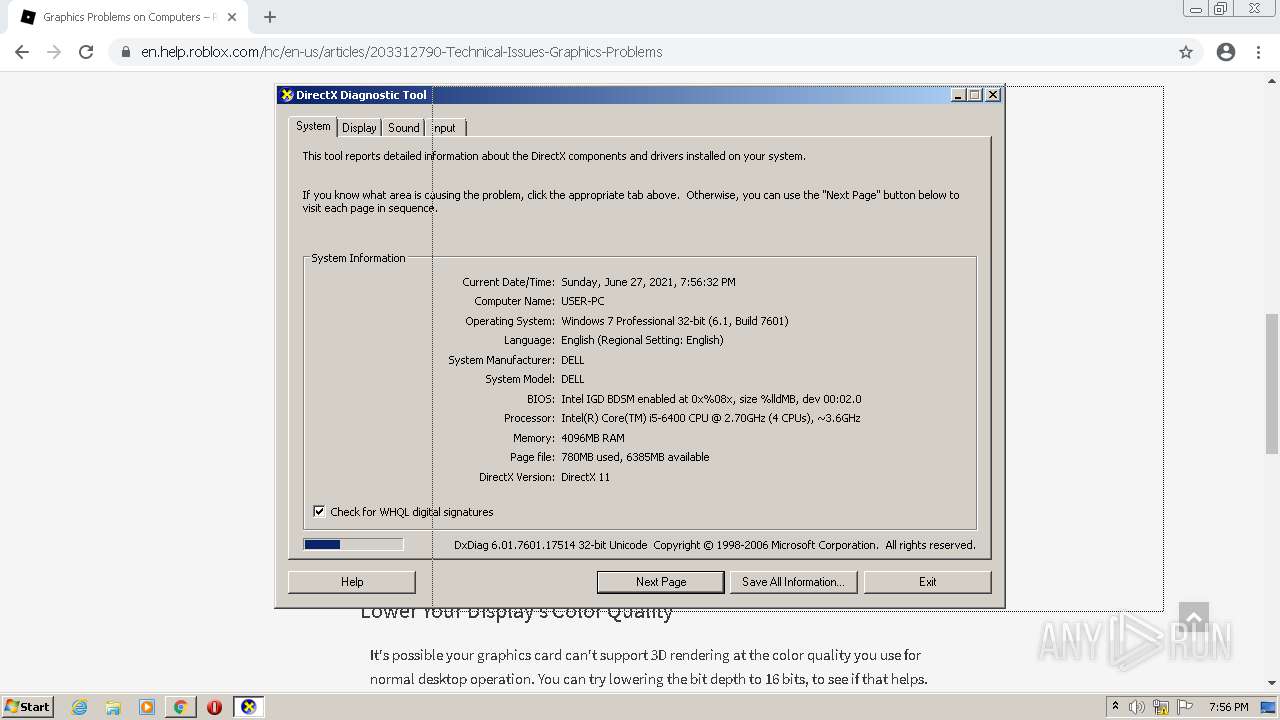
 Unable to launch roblox from browser - Platform Usage Support - Developer Forum27 março 2025
Unable to launch roblox from browser - Platform Usage Support - Developer Forum27 março 2025
você pode gostar
-
Camiseta Ferrocarril Midland ⚪🔵⚪ en Doble Vidrio27 março 2025
-
 Игровые коды One Piece — AOPG AFK Gears (декабрь 2022 г.) - Game27 março 2025
Игровые коды One Piece — AOPG AFK Gears (декабрь 2022 г.) - Game27 março 2025 -
 Notação Matemática, guia do estudante (MAT) - guidg.com27 março 2025
Notação Matemática, guia do estudante (MAT) - guidg.com27 março 2025 -
 Another exciting raffle draw is just around the corner! - Winzir27 março 2025
Another exciting raffle draw is just around the corner! - Winzir27 março 2025 -
 Movies on TV this week: Sunday, Feb. 14, 2021 - Los Angeles Times27 março 2025
Movies on TV this week: Sunday, Feb. 14, 2021 - Los Angeles Times27 março 2025 -
 Cut the Rope 2 - Intro Video - IGN27 março 2025
Cut the Rope 2 - Intro Video - IGN27 março 2025 -
 65 Desenhos para colorir kawaii e imprimir Páginas para colorir para adultos, Páginas para colorir gratuitas, Páginas de colorir com animais27 março 2025
65 Desenhos para colorir kawaii e imprimir Páginas para colorir para adultos, Páginas para colorir gratuitas, Páginas de colorir com animais27 março 2025 -
 Load Ps5 Games (Playstation 5 Games) OFFLINE ONLINE in Dansoman27 março 2025
Load Ps5 Games (Playstation 5 Games) OFFLINE ONLINE in Dansoman27 março 2025 -
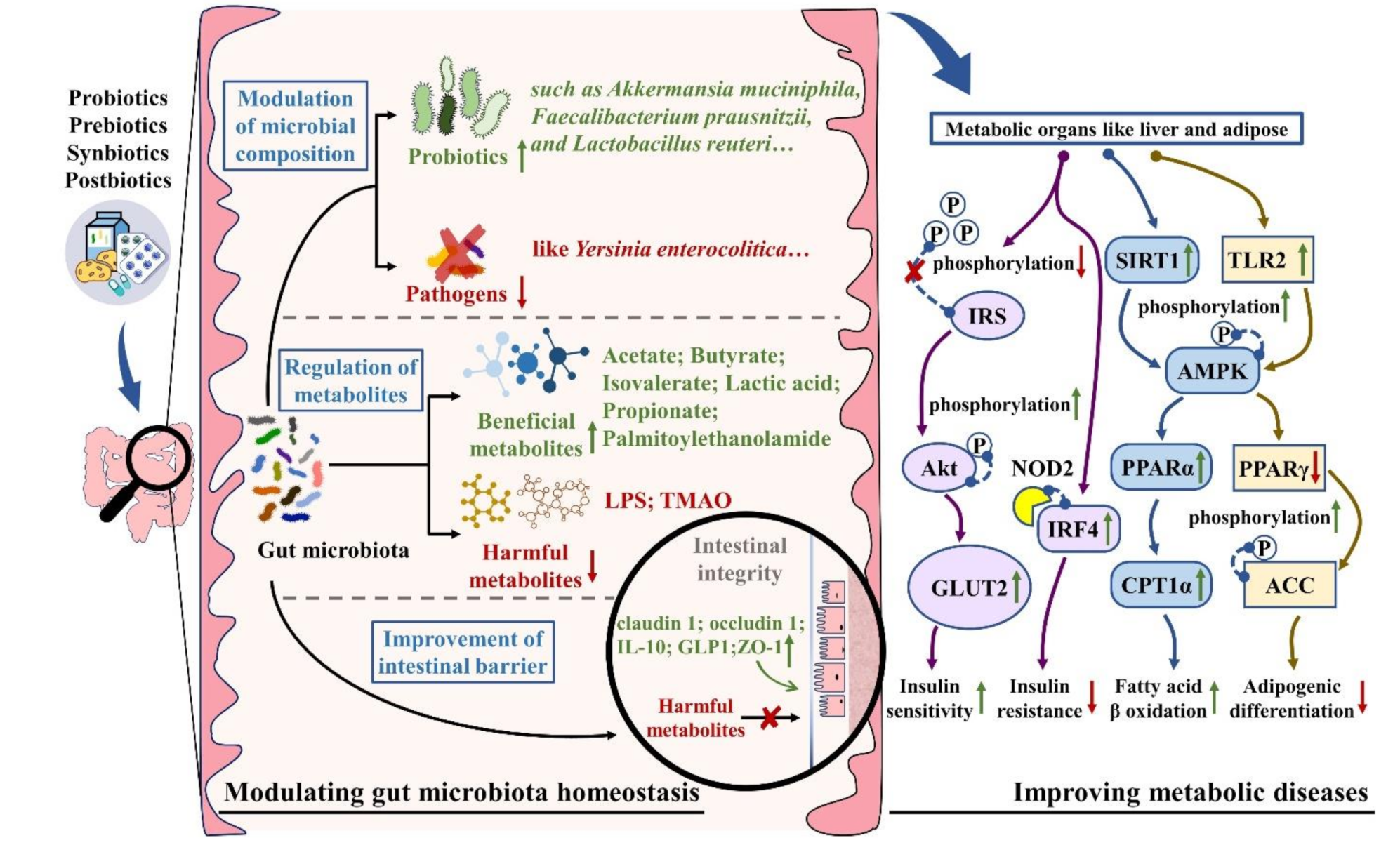 Nutrients, Free Full-Text27 março 2025
Nutrients, Free Full-Text27 março 2025 -
Torcida Tubarão Azul27 março 2025

