Malware analysis Malicious activity
Por um escritor misterioso
Last updated 13 abril 2025

Malware leveraging public infrastructure like GitHub on the rise

Security Orchestration Use Case: Automating Malware Analysis

How to Do Malware Analysis?

Malware analysis

Patch Now: Exploit Activity Mounts for Dangerous Apache Struts 2 Bug

Routers Roasting on an Open Firewall: the KV-botnet Investigation

MetaDefender Cloud Advanced threat prevention and detection

Advanced Automated Malware Analysis – Kaspersky Research Sandbox

Comprehensive Protection Strategies Against Cyber Threats

Malware Analysis: Protecting Your Network from Cyber Attacks

Playbook of the Week: Malware Investigation and Response - Palo

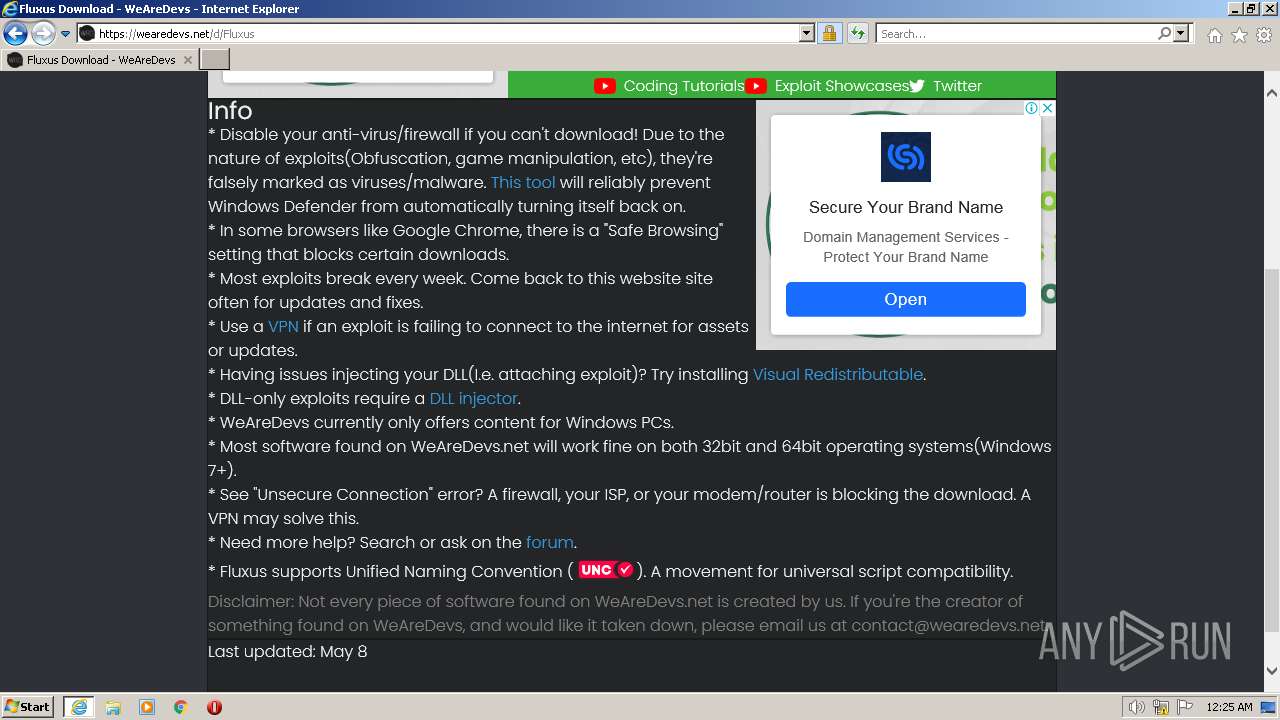
Malware analysis file Malicious activity

Routers Roasting on an Open Firewall: the KV-botnet Investigation
Recomendado para você
-
 JJSploit for Roblox 7.2.1 Download For Windows PC - Softlay13 abril 2025
JJSploit for Roblox 7.2.1 Download For Windows PC - Softlay13 abril 2025 -
wearedevs.net Competitors - Top Sites Like wearedevs.net13 abril 2025
-
Is Wearedevs Safe13 abril 2025
-
Hoopz Script Pastebin Op Gui13 abril 2025
-
 تحميل سكربت طيران روبلوكس arceus x fly v2 script loadstring13 abril 2025
تحميل سكربت طيران روبلوكس arceus x fly v2 script loadstring13 abril 2025 -
 Injenction failed fluxus|TikTok Search13 abril 2025
Injenction failed fluxus|TikTok Search13 abril 2025 -
 Download Fluxus v9 APK 9.0 for Android13 abril 2025
Download Fluxus v9 APK 9.0 for Android13 abril 2025 -
Infinite Yield Roblox13 abril 2025
-
ain't no way Fluxus *Killer* 💀 Keyless and v8! 💀 #evon #fypstotted #13 abril 2025
-
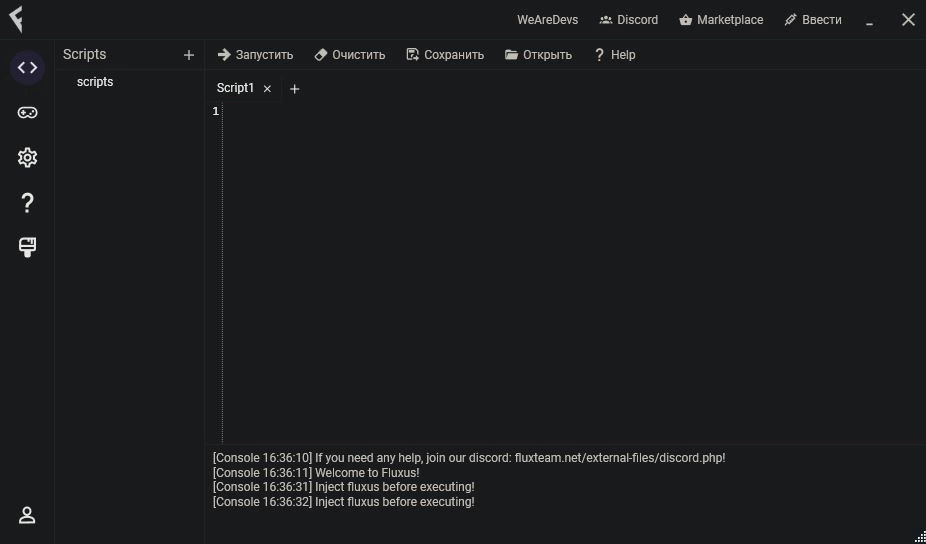 Fluxus - (Free Roblox Exploit) - Roblox-Scripter13 abril 2025
Fluxus - (Free Roblox Exploit) - Roblox-Scripter13 abril 2025
você pode gostar
-
 KonoSuba Movie Original Soundtrack13 abril 2025
KonoSuba Movie Original Soundtrack13 abril 2025 -
 Pin by 𝕵𝖊𝖘𝖘𝖎𝖊. on ❃ anime13 abril 2025
Pin by 𝕵𝖊𝖘𝖘𝖎𝖊. on ❃ anime13 abril 2025 -
 Top 14 Best Indoor Games That You Can Play With Your Kids13 abril 2025
Top 14 Best Indoor Games That You Can Play With Your Kids13 abril 2025 -
Shazam: Fury of the Gods (2023) - The Ultimate Superheroines Forum13 abril 2025
-
 Kimetsu no Yaiba (Demon Slayer) Lucky Bag Review • Core Reviews13 abril 2025
Kimetsu no Yaiba (Demon Slayer) Lucky Bag Review • Core Reviews13 abril 2025 -
About: YES or NO wheel - spin to decide (Google Play version13 abril 2025
-
 Darlison4D / Mascot 3D & Motion - SONIC MY FAN ART13 abril 2025
Darlison4D / Mascot 3D & Motion - SONIC MY FAN ART13 abril 2025 -
 Senran Kagura Burst Preview - Japanese Ninja Schoolgirls Are Coming To North America - Game Informer13 abril 2025
Senran Kagura Burst Preview - Japanese Ninja Schoolgirls Are Coming To North America - Game Informer13 abril 2025 -
 Bandana Durag Preta Veludo Alta Qualidade - Yucca - Bandana13 abril 2025
Bandana Durag Preta Veludo Alta Qualidade - Yucca - Bandana13 abril 2025 -
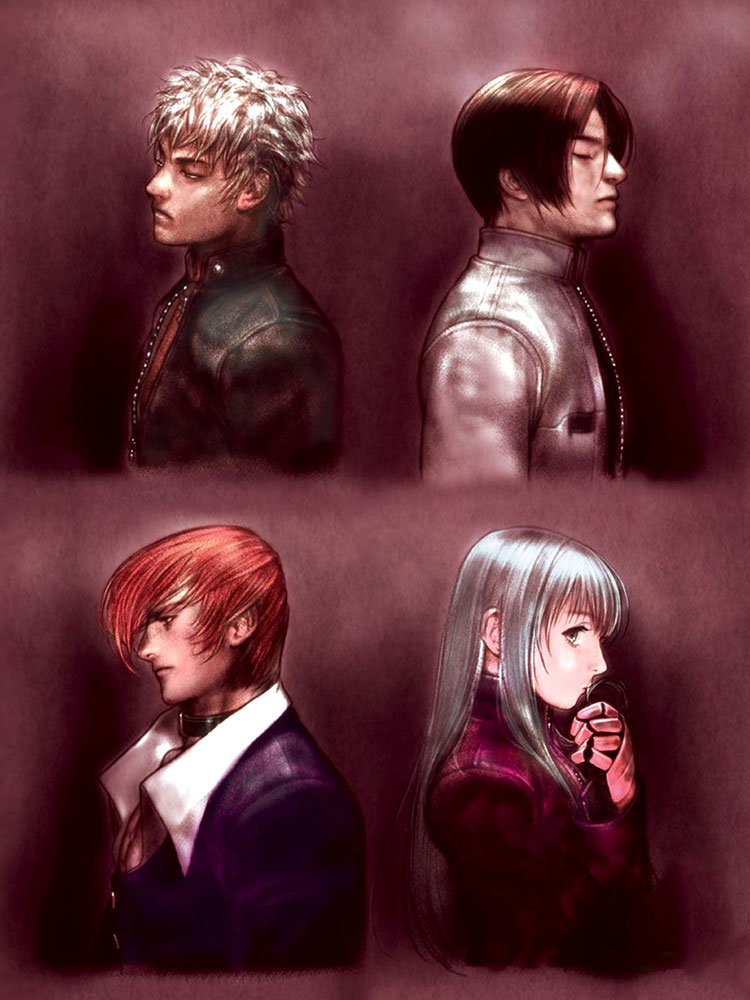 King Of Fighters 2002 Official Artworks13 abril 2025
King Of Fighters 2002 Official Artworks13 abril 2025

