Malware analysis Malicious activity
Por um escritor misterioso
Last updated 25 abril 2025

Malware Analysis: Steps & Examples - CrowdStrike

Security Orchestration Use Case: Automating Malware Analysis - Palo Alto Networks Blog

What Is Malware Analysis? Definition, Types, Stages, and Best Practices - Spiceworks

PROUD-MAL: static analysis-based progressive framework for deep unsupervised malware classification of windows portable executable

Detail procedure of malware analysis

Feature Extraction and Detection of Malwares Using Machine Learning
TryHackMe Hacktivities
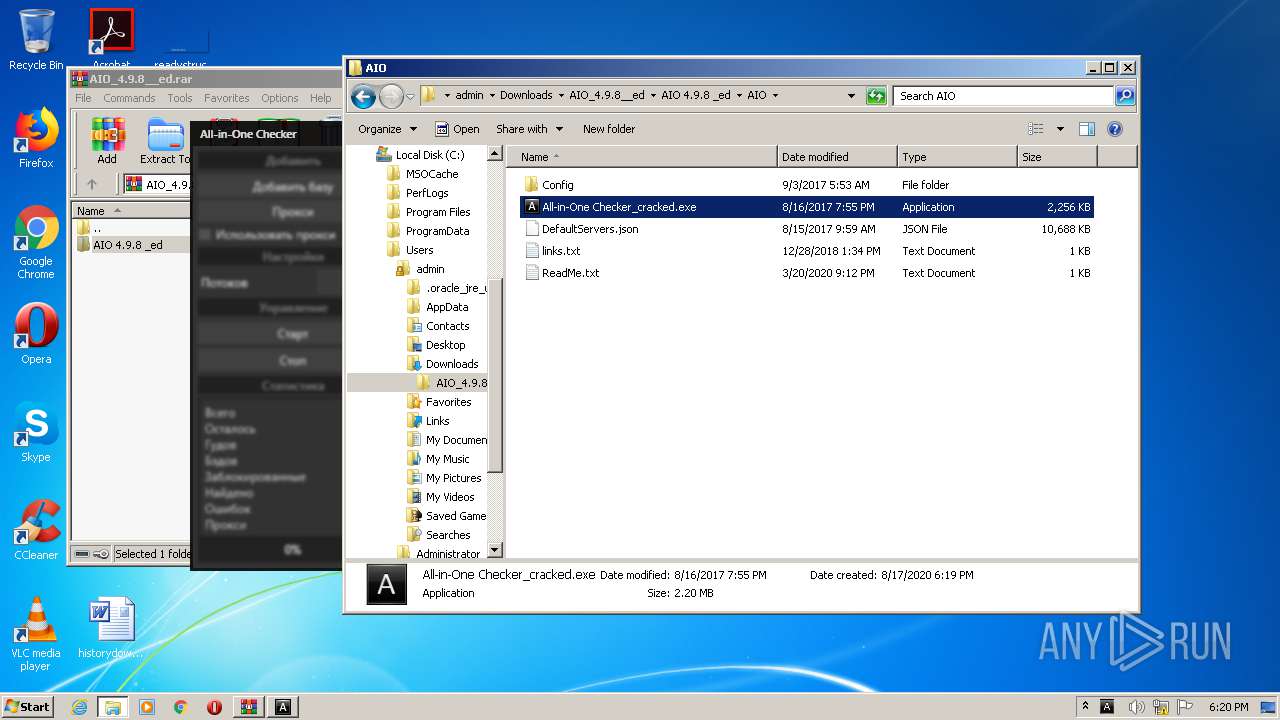
Malware analysis AIO_4.9.8__ed.rar Malicious activity
Interactive Online Malware Sandbox

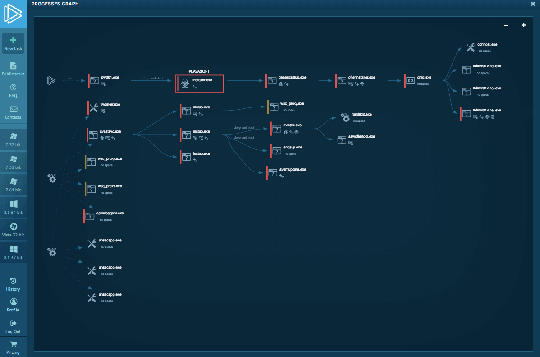
Malware analysis tt.7z Malicious activity

Remediation and Malware Detection Overview

UK and allies support Ukraine calling out Russia's GRU for
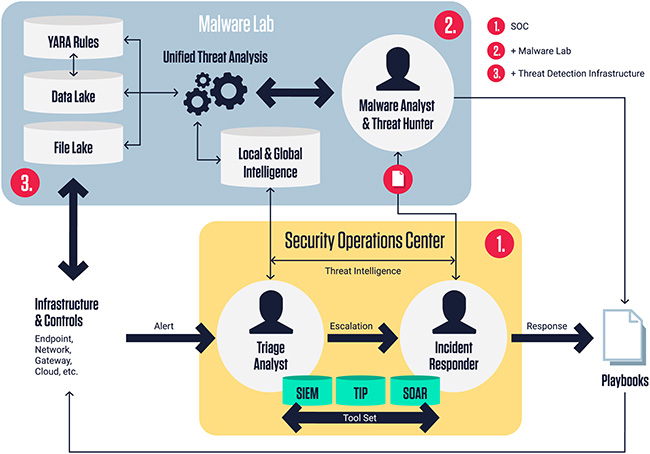
ReversingLabs Malware Lab: Detect, classify, analyze, and respond to malicious files - Help Net Security
Recomendado para você
-
.png%3Falt%3Dmedia%26token%3D98718cff-fa3e-4fb4-b2ff-dbdfc3386898) Executing Scripts - MainDab Documentation25 abril 2025
Executing Scripts - MainDab Documentation25 abril 2025 -
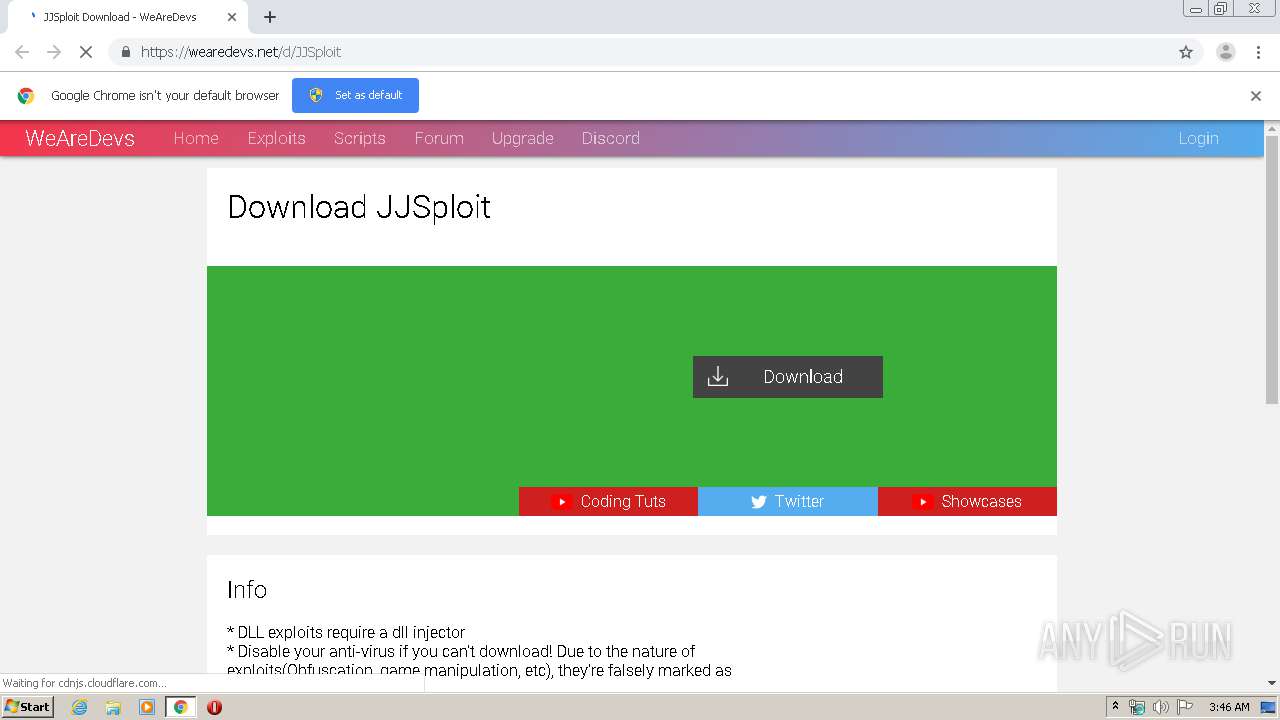
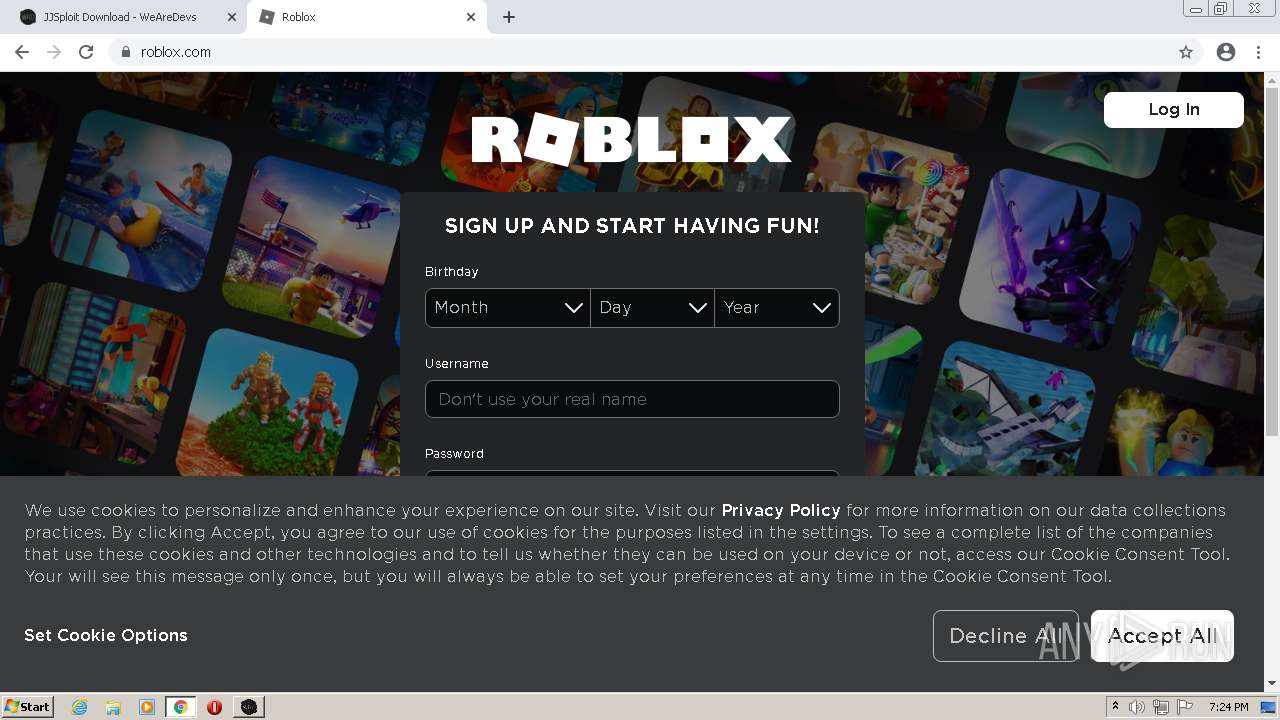
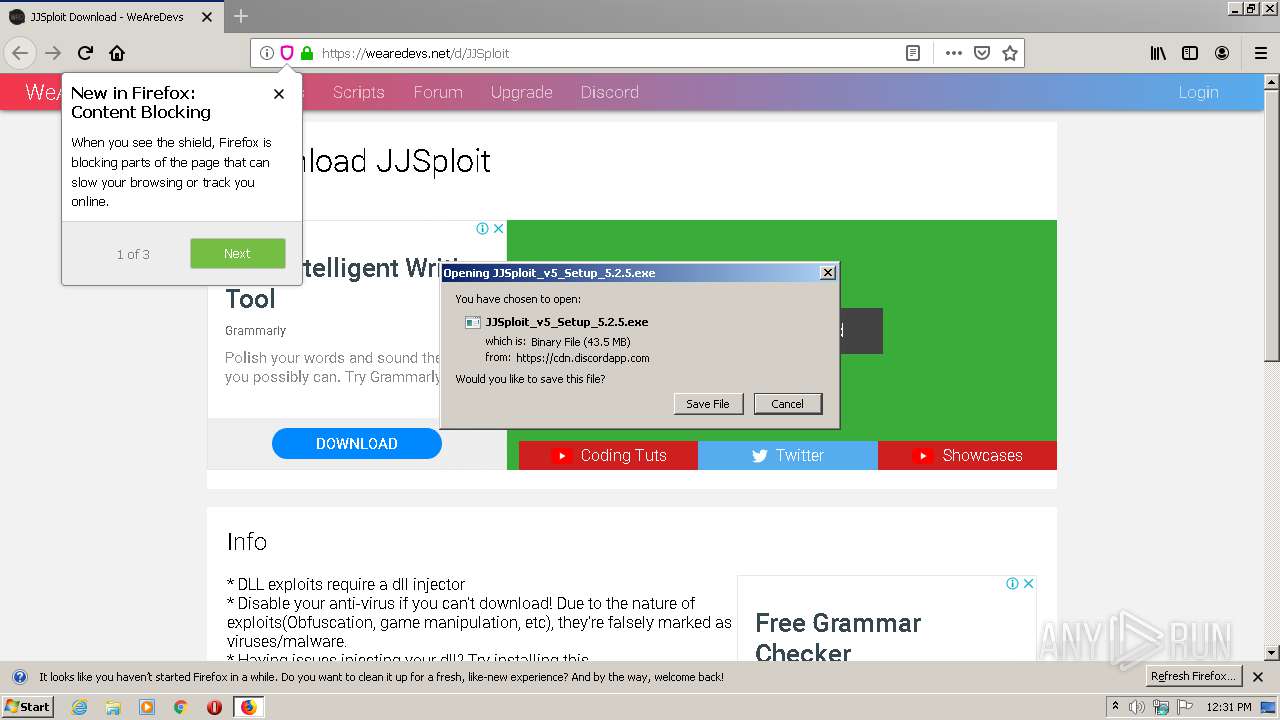
 Roblox Aimbot Script with JJSploit Lua Executor25 abril 2025
Roblox Aimbot Script with JJSploit Lua Executor25 abril 2025 -
roblox-scripts · GitHub Topics · GitHub25 abril 2025
-
 Random require script appearing each time I login to studio - Scripting Support - Developer Forum25 abril 2025
Random require script appearing each time I login to studio - Scripting Support - Developer Forum25 abril 2025 -
 JJsPLOIT Tutorial #Exploit #tutorial #WeAreDevs #scripting25 abril 2025
JJsPLOIT Tutorial #Exploit #tutorial #WeAreDevs #scripting25 abril 2025 -
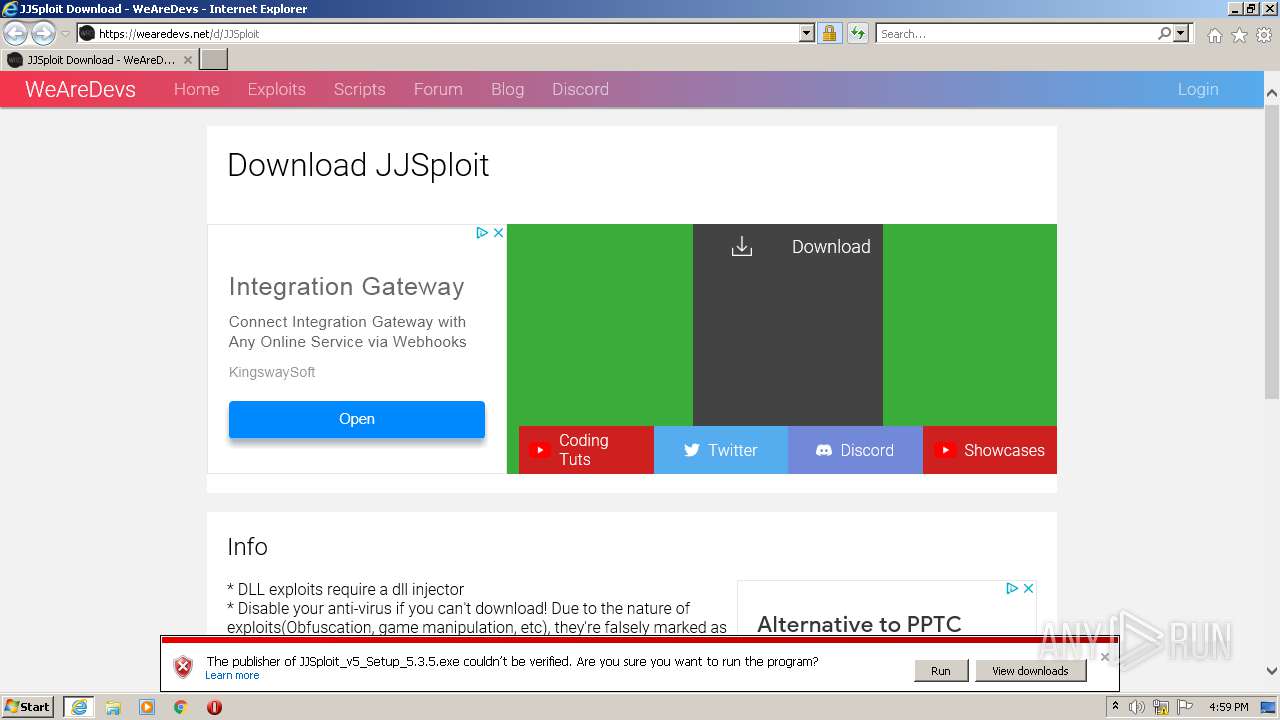 Malware analysis Malicious25 abril 2025
Malware analysis Malicious25 abril 2025 -
 Malware analysis Malicious25 abril 2025
Malware analysis Malicious25 abril 2025 -
roblox #fyo #hack #script #jjsploit #wearedevs Like and Comment25 abril 2025
-
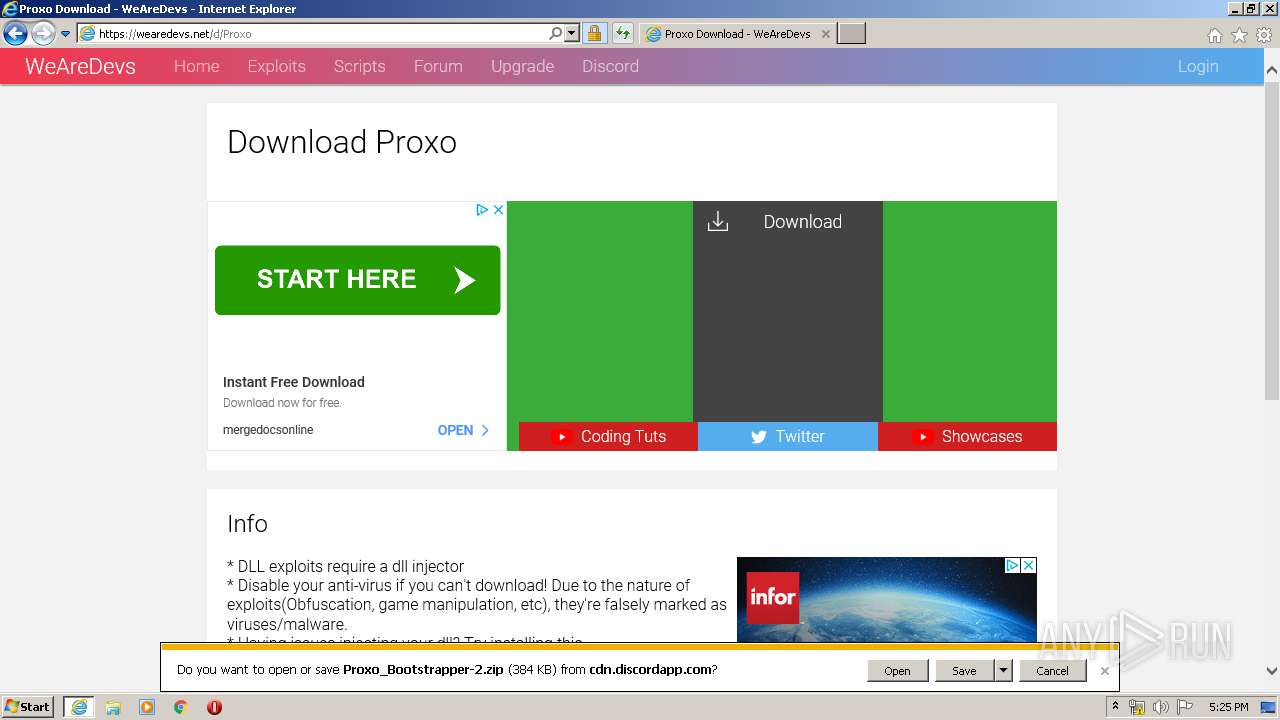 Malware analysis Malicious25 abril 2025
Malware analysis Malicious25 abril 2025 -
 Malware analysis Malicious25 abril 2025
Malware analysis Malicious25 abril 2025
você pode gostar
-
 Crazy Taxi: Fare Wars Review - IGN25 abril 2025
Crazy Taxi: Fare Wars Review - IGN25 abril 2025 -
 Masters of the Universe: Revelation Masterverse Action Figure Sorceress 18 cm25 abril 2025
Masters of the Universe: Revelation Masterverse Action Figure Sorceress 18 cm25 abril 2025 -
 Filme - Pterodactyl - A Ameaça Jurássica (Pterodactyl) - 200525 abril 2025
Filme - Pterodactyl - A Ameaça Jurássica (Pterodactyl) - 200525 abril 2025 -
/i.s3.glbimg.com/v1/AUTH_bc8228b6673f488aa253bbcb03c80ec5/internal_photos/bs/2021/Z/Q/xZRQniS0mmPXgBJkQ4bw/gettyimages-1231802440.jpg) Liga dos Campeões começa com sete jogos da primeira fase25 abril 2025
Liga dos Campeões começa com sete jogos da primeira fase25 abril 2025 -
 Amidst the CHAOS, a FURIOUS TITAN appears to help HUMANITY - RECAP (PART 3)25 abril 2025
Amidst the CHAOS, a FURIOUS TITAN appears to help HUMANITY - RECAP (PART 3)25 abril 2025 -
 One Piece Vs. The Anime25 abril 2025
One Piece Vs. The Anime25 abril 2025 -
Ricardo Caruana - Go-To-Market Lead, AI/ML - Google25 abril 2025
-
skin roblox tryhard blox fruit|Recherche TikTok25 abril 2025
-
 Kats to play Texas State at NRG Stadium in 2024 - Sam Houston25 abril 2025
Kats to play Texas State at NRG Stadium in 2024 - Sam Houston25 abril 2025 -
 Chuteira Infantil Menino Para Campo Jogo Futebol Com Pinos25 abril 2025
Chuteira Infantil Menino Para Campo Jogo Futebol Com Pinos25 abril 2025


