Malware analysis Malicious activity
Por um escritor misterioso
Last updated 13 abril 2025

Security Orchestration Use Case: Automating Malware Analysis - Palo Alto Networks Blog

What is Malware? Definition, Types, Prevention - TechTarget

Routers Roasting on an Open Firewall: the KV-botnet Investigation - Lumen

FBI, CISA, MS-ISAC release cybersecurity advisory on emerging Rhysida ransomware targeting critical sectors - Industrial Cyber

Cybersecurity Search Engine
Interactive Online Malware Sandbox

TryHackMe Hacktivities

Malware analysis metasploit.bat Malicious activity
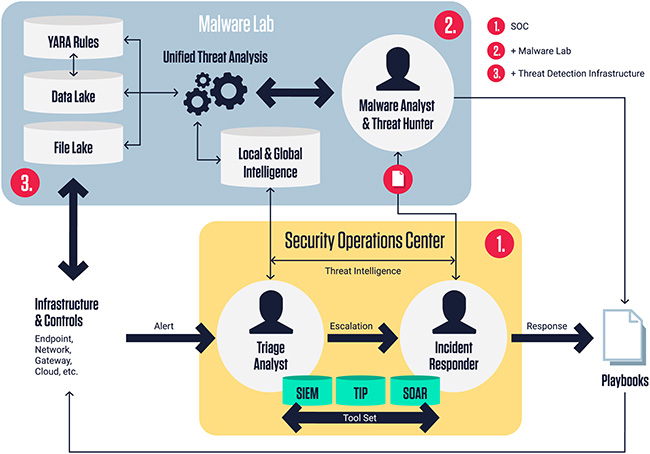
ReversingLabs Malware Lab: Detect, classify, analyze, and respond to malicious files - Help Net Security

An Elastic approach to large-scale dynamic malware analysis — Elastic Security Labs

Info stealers and how to protect against them
Recomendado para você
-
 Songbook13 abril 2025
Songbook13 abril 2025 -
 SongBook13 abril 2025
SongBook13 abril 2025 -
Pdfcoffee.com Songbook Choro Chediak Vol 3 PDF Free13 abril 2025
-
 Songbook for Keyboard13 abril 2025
Songbook for Keyboard13 abril 2025 -
 Malware analysis Malicious activity13 abril 2025
Malware analysis Malicious activity13 abril 2025 -
 The Great American Songbook.pdf13 abril 2025
The Great American Songbook.pdf13 abril 2025 -
 Richard Galliano SongBook.pdf13 abril 2025
Richard Galliano SongBook.pdf13 abril 2025 -
 King's Singers Sheet Music and Songbook Arrangements13 abril 2025
King's Singers Sheet Music and Songbook Arrangements13 abril 2025 -
 Kiss - The Best of Guitar Songbook13 abril 2025
Kiss - The Best of Guitar Songbook13 abril 2025 -
 My First Jazz Standards Song Book - A Treasury of Favorite Songs to Play (Sheet Music) My First Piano Song Books (159635) by Hal Leonard13 abril 2025
My First Jazz Standards Song Book - A Treasury of Favorite Songs to Play (Sheet Music) My First Piano Song Books (159635) by Hal Leonard13 abril 2025
você pode gostar
-
 asdasdas:d on Make a GIF13 abril 2025
asdasdas:d on Make a GIF13 abril 2025 -
 Lanvin Spring 2022 Ready-to-Wear Fashion Show13 abril 2025
Lanvin Spring 2022 Ready-to-Wear Fashion Show13 abril 2025 -
 Hackers hit Reddit; deface 70+ Subreddits with Pro-Trump messages13 abril 2025
Hackers hit Reddit; deface 70+ Subreddits with Pro-Trump messages13 abril 2025 -
 Kuusen Madoushi Kouhosei No Kyoukan Season 2 Release Date13 abril 2025
Kuusen Madoushi Kouhosei No Kyoukan Season 2 Release Date13 abril 2025 -
 Warren Zevon – Werewolves of London Lyrics13 abril 2025
Warren Zevon – Werewolves of London Lyrics13 abril 2025 -
 Gay Paris: Where's Hot in 2023? New gay bars, saunas, parties, hotels, map +13 abril 2025
Gay Paris: Where's Hot in 2023? New gay bars, saunas, parties, hotels, map +13 abril 2025 -
 GTA Gaming Archive13 abril 2025
GTA Gaming Archive13 abril 2025 -
KIT C/ 2 Arminha Lança Dardos e Bolinhas Água Gel Pistola de Brinquedo Arma Tipo Nerf Barato Criança13 abril 2025
-
 How to Breathe in a Cold Plunge Through the Wim Hof Method – Renu13 abril 2025
How to Breathe in a Cold Plunge Through the Wim Hof Method – Renu13 abril 2025 -
/cdn.vox-cdn.com/uploads/chorus_image/image/59983051/968733062.jpg.0.jpg) NBA Finals 2018 MVP is Kevin Durant after a close call with teammate Stephen Curry13 abril 2025
NBA Finals 2018 MVP is Kevin Durant after a close call with teammate Stephen Curry13 abril 2025

