Malware analysis Malicious activity
Por um escritor misterioso
Last updated 13 abril 2025

How to Do Malware Analysis?

Malware analysis index.html Malicious activity
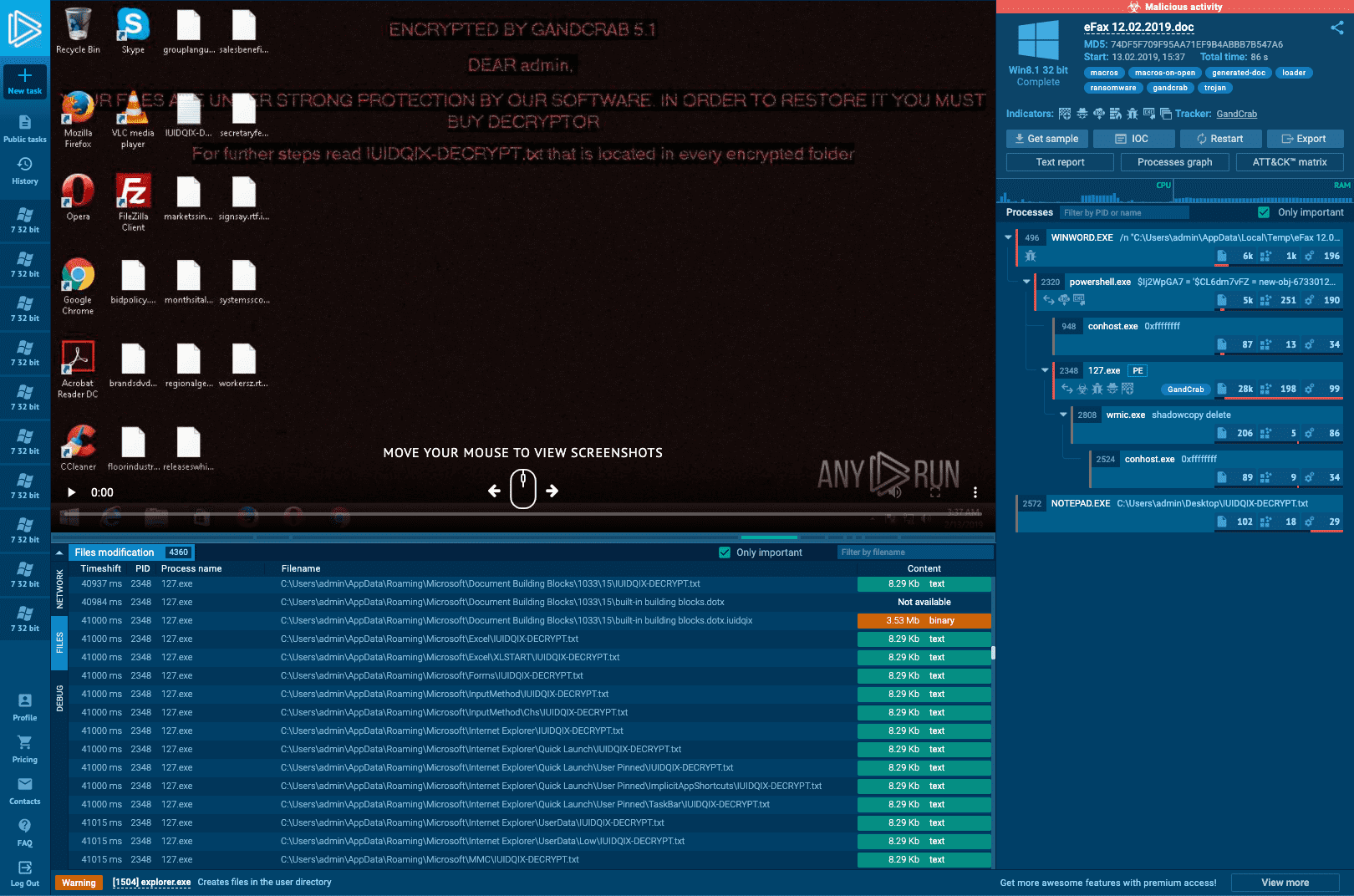
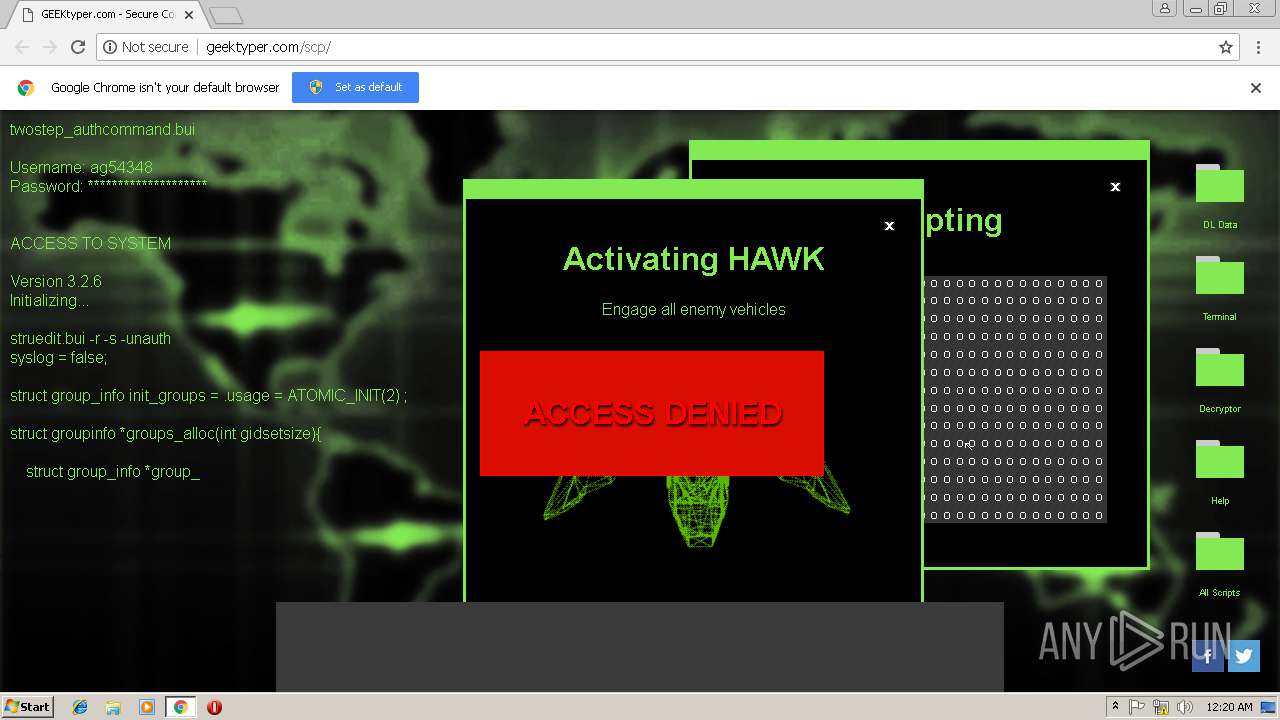
Interactive Online Malware Sandbox

MetaDefender Cloud Advanced threat prevention and detection

The Guide to Ransomware Solutions in 2023 - Security Boulevard

Info stealers and how to protect against them

Malware Analysis: Steps & Examples - CrowdStrike

Comprehensive Protection Strategies Against Cyber Threats

Mastering Malware Analysis

Malware Analysis: Steps & Examples - CrowdStrike

Malware Analysis: Steps & Examples - CrowdStrike

Patch Now: Exploit Activity Mounts for Dangerous Apache Struts 2 Bug
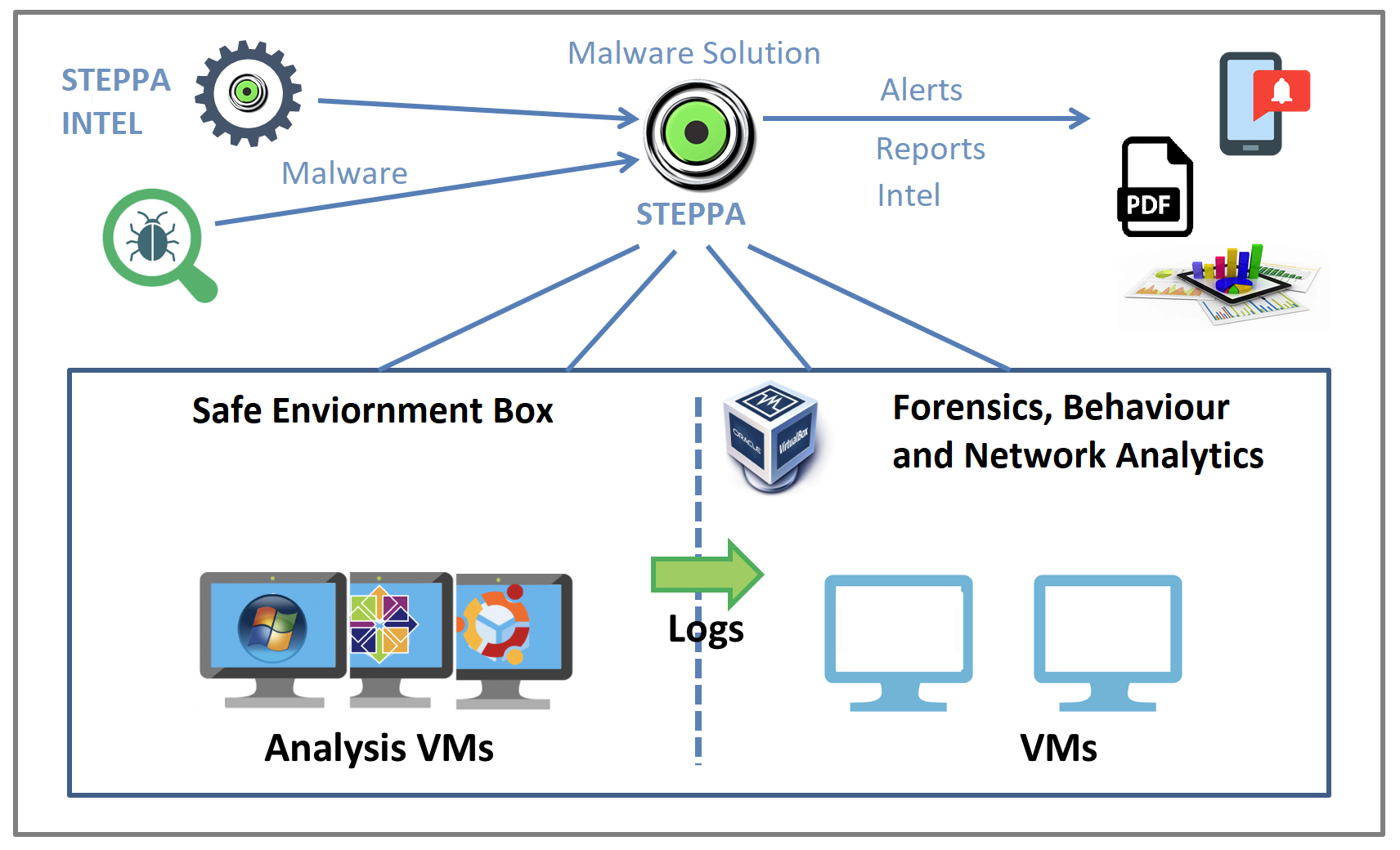
Malware Analysis Solution: Analyze, Detect, and Protect
Recomendado para você
-
 Online Hacker Simulator and Typer13 abril 2025
Online Hacker Simulator and Typer13 abril 2025 -
 Hacker Typer Pro - Prank App by Omer Karakullukcu13 abril 2025
Hacker Typer Pro - Prank App by Omer Karakullukcu13 abril 2025 -
 A hacker using the code simulator Ge, Stock Video13 abril 2025
A hacker using the code simulator Ge, Stock Video13 abril 2025 -
 Hacker Typer - Geek Prank Hacker Simulator Online13 abril 2025
Hacker Typer - Geek Prank Hacker Simulator Online13 abril 2025 -
:strip_icc()/i.s3.glbimg.com/v1/AUTH_08fbf48bc0524877943fe86e43087e7a/internal_photos/bs/2021/m/C/yAj1AQQDG2VA89LsIptw/pexels-sora-shimazaki-5935794.jpg) Hacker Typer: o que é e como usar o simulador para fingir ser hacker13 abril 2025
Hacker Typer: o que é e como usar o simulador para fingir ser hacker13 abril 2025 -
 Hacker Typer Game Simulated Fake Hacking Unblocked13 abril 2025
Hacker Typer Game Simulated Fake Hacking Unblocked13 abril 2025 -
 Sites permitem que usuários finjam que são hackers - Canaltech13 abril 2025
Sites permitem que usuários finjam que são hackers - Canaltech13 abril 2025 -
 GeekTyper Official APK for Android - Download13 abril 2025
GeekTyper Official APK for Android - Download13 abril 2025 -
 That One Hacker Kid Starter Pack : r/starterpacks13 abril 2025
That One Hacker Kid Starter Pack : r/starterpacks13 abril 2025 -
 Link Download Hacker Typer APK for Android Terbaru 202313 abril 2025
Link Download Hacker Typer APK for Android Terbaru 202313 abril 2025
você pode gostar
-
 Exército envia blindados para a fronteira do Brasil com Venezuela13 abril 2025
Exército envia blindados para a fronteira do Brasil com Venezuela13 abril 2025 -
 Jogos Gratuitos PS Plus de Março 202313 abril 2025
Jogos Gratuitos PS Plus de Março 202313 abril 2025 -
 How to Pronounce MAN vs. MEN - American English13 abril 2025
How to Pronounce MAN vs. MEN - American English13 abril 2025 -
 Overwatch 2 review - a brilliant teamplay experience in the grip13 abril 2025
Overwatch 2 review - a brilliant teamplay experience in the grip13 abril 2025 -
 Sonic the Hedgehog (8-bit), Sonic Wiki Zone13 abril 2025
Sonic the Hedgehog (8-bit), Sonic Wiki Zone13 abril 2025 -
 Renewal (Digibook) by Kreator13 abril 2025
Renewal (Digibook) by Kreator13 abril 2025 -
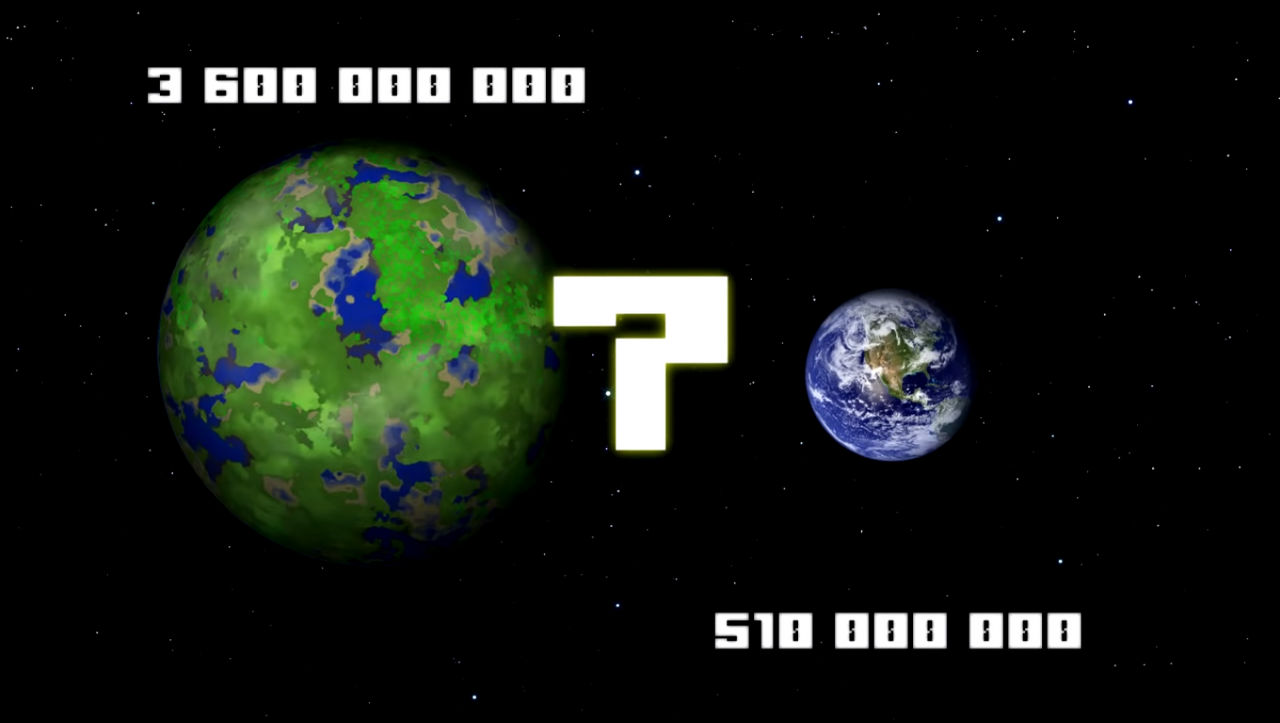 Minecraft planet versus earth. by WorldOfPeter12 on DeviantArt13 abril 2025
Minecraft planet versus earth. by WorldOfPeter12 on DeviantArt13 abril 2025 -
 27 ideias de Oni OC KNY personagens de anime, anime, demônio em desenho13 abril 2025
27 ideias de Oni OC KNY personagens de anime, anime, demônio em desenho13 abril 2025 -
 Lego Harry Potter Collection Review - Review - Nintendo World Report13 abril 2025
Lego Harry Potter Collection Review - Review - Nintendo World Report13 abril 2025 -
 Purple😍😍 #rainbowfriends #rainbowfriendsplushie #rainbowfriendsroblo13 abril 2025
Purple😍😍 #rainbowfriends #rainbowfriendsplushie #rainbowfriendsroblo13 abril 2025