Malware analysis Malicious activity
Por um escritor misterioso
Last updated 05 abril 2025

Routers Roasting on an Open Firewall: the KV-botnet Investigation - Lumen

Playbook for Malware outbreak

A detailed analysis of the Menorah malware used by APT34

Remediation and Malware Detection Overview

PROUD-MAL: static analysis-based progressive framework for deep unsupervised malware classification of windows portable executable

Malware analysis file Malicious activity

Routers Roasting on an Open Firewall: the KV-botnet Investigation - Lumen
Most Common Malware Attacks

Malware analysis mykey_.rar Malicious activity
Malware analysis apksharp.com Malicious activity

An Elastic approach to large-scale dynamic malware analysis — Elastic Security Labs

Security Orchestration Use Case: Automating Malware Analysis - Palo Alto Networks Blog
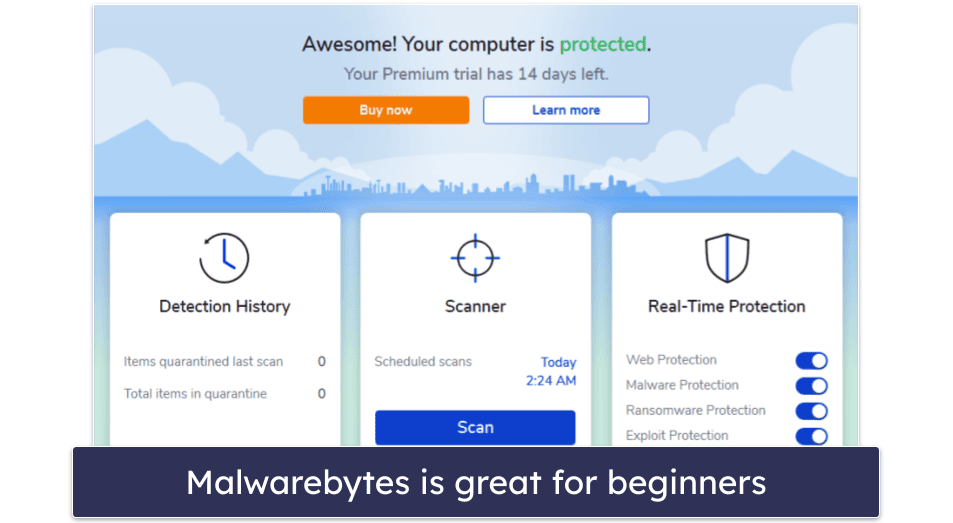
10 Best Antivirus Software in 2023: Windows, Android, iOS, Mac
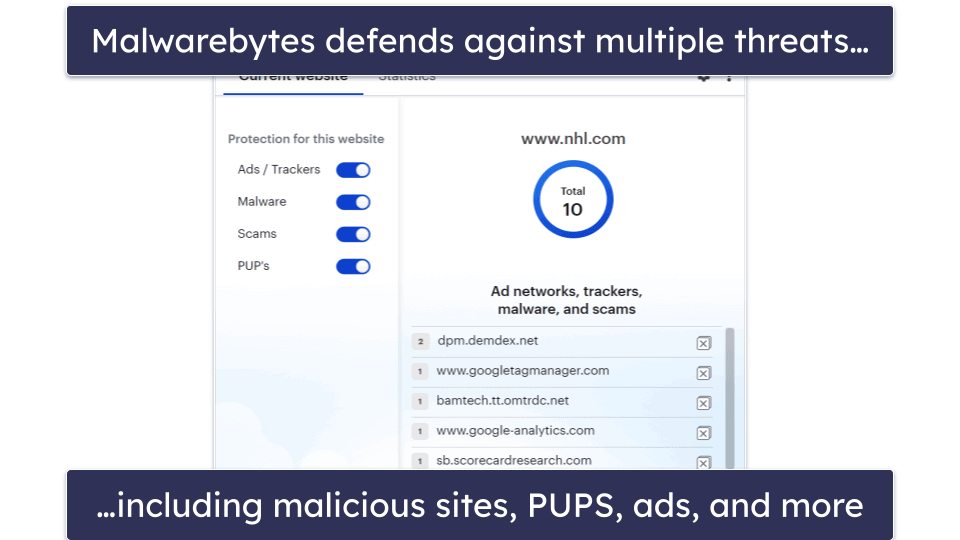
10 Best (REALLY FREE) Antivirus Software for Windows in 2023
Recomendado para você
-
 That's very clever. : r/CookieClicker05 abril 2025
That's very clever. : r/CookieClicker05 abril 2025 -
 Favourite grandma name : r/CookieClicker05 abril 2025
Favourite grandma name : r/CookieClicker05 abril 2025 -
Solved: How do I add an iframe to a confluence page?05 abril 2025
-
 cohost! - a sneak peek of media embeds05 abril 2025
cohost! - a sneak peek of media embeds05 abril 2025 -
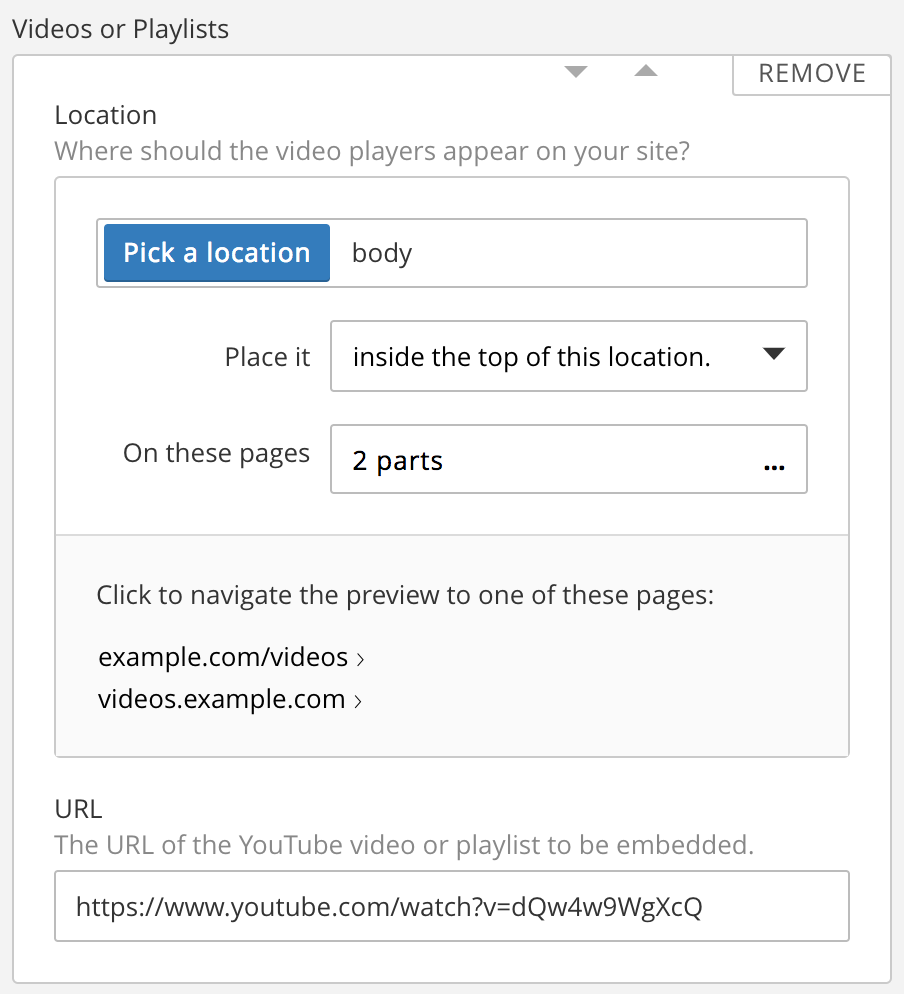 Cloudflare Apps Platform Update: September Edition05 abril 2025
Cloudflare Apps Platform Update: September Edition05 abril 2025 -
Rogelio M. Armino - Systems Engineer - Medical - Texas Instruments05 abril 2025
-
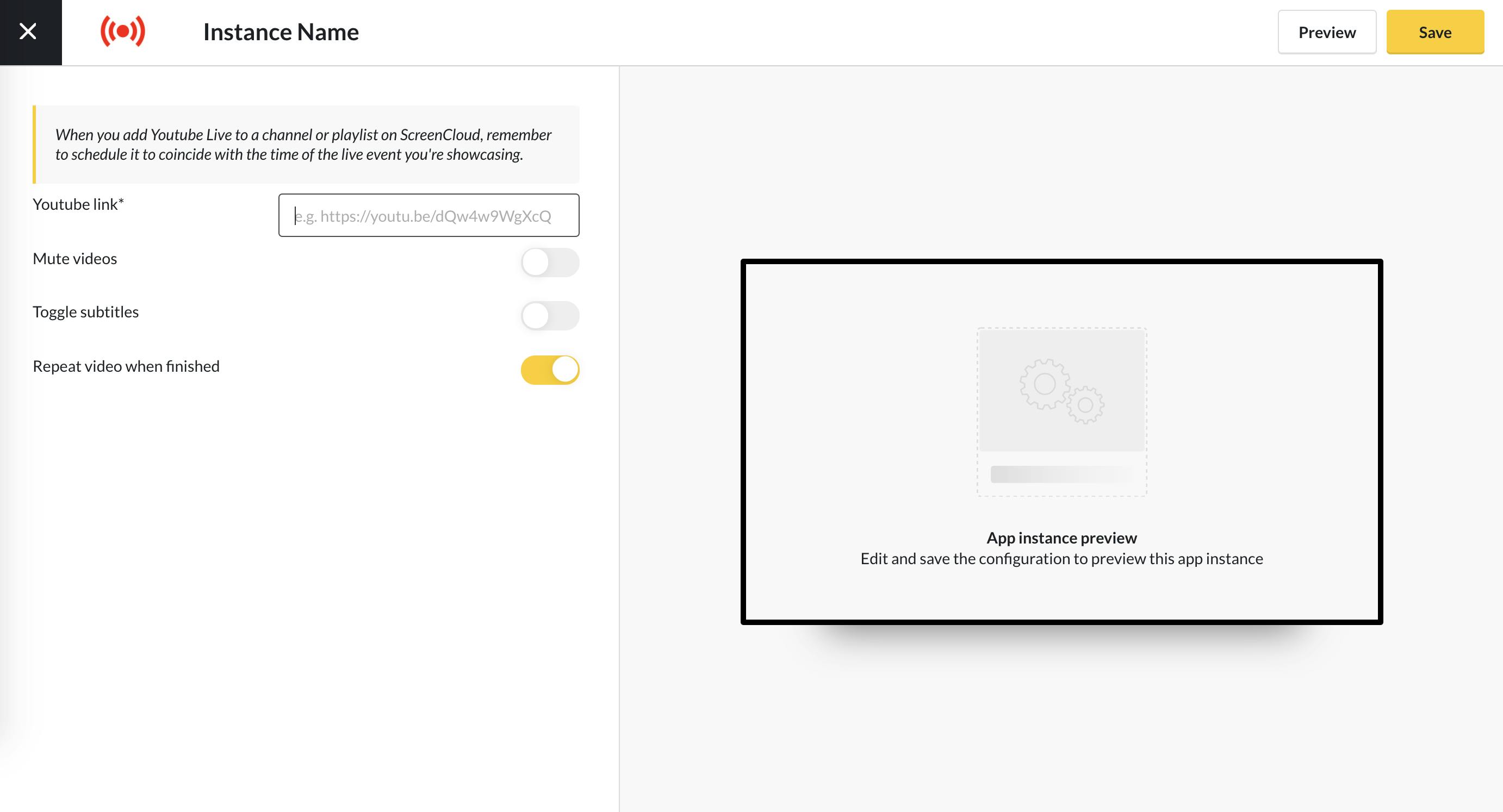 Live App Guide for ScreenCloud - ScreenCloud05 abril 2025
Live App Guide for ScreenCloud - ScreenCloud05 abril 2025 -
The Desktop - Skymods05 abril 2025
-
![What is 'Click-to-Play' and how to enable it in Chrome, Firefox, Opera, and Internet Explorer [dotTech Explains]](https://dt.azadicdn.com/wp-content/uploads/2013/03/2013-03-10_203836.png?7653) What is 'Click-to-Play' and how to enable it in Chrome, Firefox, Opera, and Internet Explorer [dotTech Explains]05 abril 2025
What is 'Click-to-Play' and how to enable it in Chrome, Firefox, Opera, and Internet Explorer [dotTech Explains]05 abril 2025 -
 XSS: Cross-Site Scripting (Part 1), by Marco Angelo05 abril 2025
XSS: Cross-Site Scripting (Part 1), by Marco Angelo05 abril 2025
você pode gostar
-
 The Guardians of the Galaxy Holiday Special - Wikipedia05 abril 2025
The Guardians of the Galaxy Holiday Special - Wikipedia05 abril 2025 -
 Marvel Spider-Man: Across The Spider-Verse Spider-Man Toy, 6-Inch-Scale Action Figure with Web Accessory, Toys for Kids Ages 4 and Up05 abril 2025
Marvel Spider-Man: Across The Spider-Verse Spider-Man Toy, 6-Inch-Scale Action Figure with Web Accessory, Toys for Kids Ages 4 and Up05 abril 2025 -
 Download The Legend of Zelda A Link To The Past SNES ROM05 abril 2025
Download The Legend of Zelda A Link To The Past SNES ROM05 abril 2025 -
 Top 2 jogos da semana para se utilizar na educação - Game Comenius05 abril 2025
Top 2 jogos da semana para se utilizar na educação - Game Comenius05 abril 2025 -
 Malware analysis Malicious activity05 abril 2025
Malware analysis Malicious activity05 abril 2025 -
 Casemiro marca e garante empate do Manchester United contra o05 abril 2025
Casemiro marca e garante empate do Manchester United contra o05 abril 2025 -
 Create an offline game for Opera GX to never get bored when your05 abril 2025
Create an offline game for Opera GX to never get bored when your05 abril 2025 -
 Download Candy Crush Saga for Android - Free - 1.267.0.205 abril 2025
Download Candy Crush Saga for Android - Free - 1.267.0.205 abril 2025 -
 Budapest Honved Contra O Jogo De Futebol De Anzhi Makhachkala Foto de Stock Editorial - Imagem de tiroteio, campeonato: 2590623805 abril 2025
Budapest Honved Contra O Jogo De Futebol De Anzhi Makhachkala Foto de Stock Editorial - Imagem de tiroteio, campeonato: 2590623805 abril 2025 -
 Walmart inaugura seção de produtos brasileiros em loja no sul da05 abril 2025
Walmart inaugura seção de produtos brasileiros em loja no sul da05 abril 2025