Malware analysis Malicious activity
Por um escritor misterioso
Last updated 04 abril 2025

Malware Analysis: Steps & Examples - CrowdStrike

Routers Roasting on an Open Firewall: the KV-botnet Investigation

A detailed analysis of the Menorah malware used by APT34
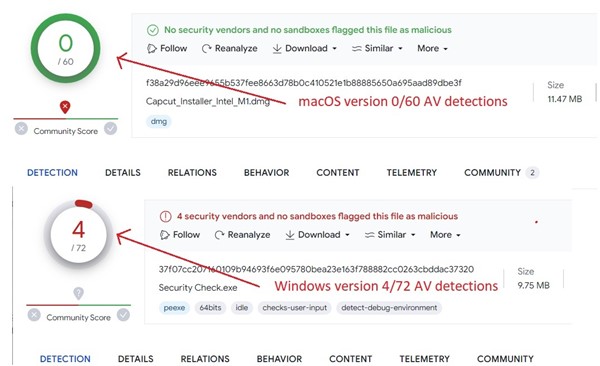
Behind the Scenes: JaskaGO's Coordinated Strike on macOS and Windows
GitHub - mesquidar/ForensicsTools: A list of free and open

How to build a malware analysis sandbox with Elastic Security

Malware analysis mykey_.rar Malicious activity
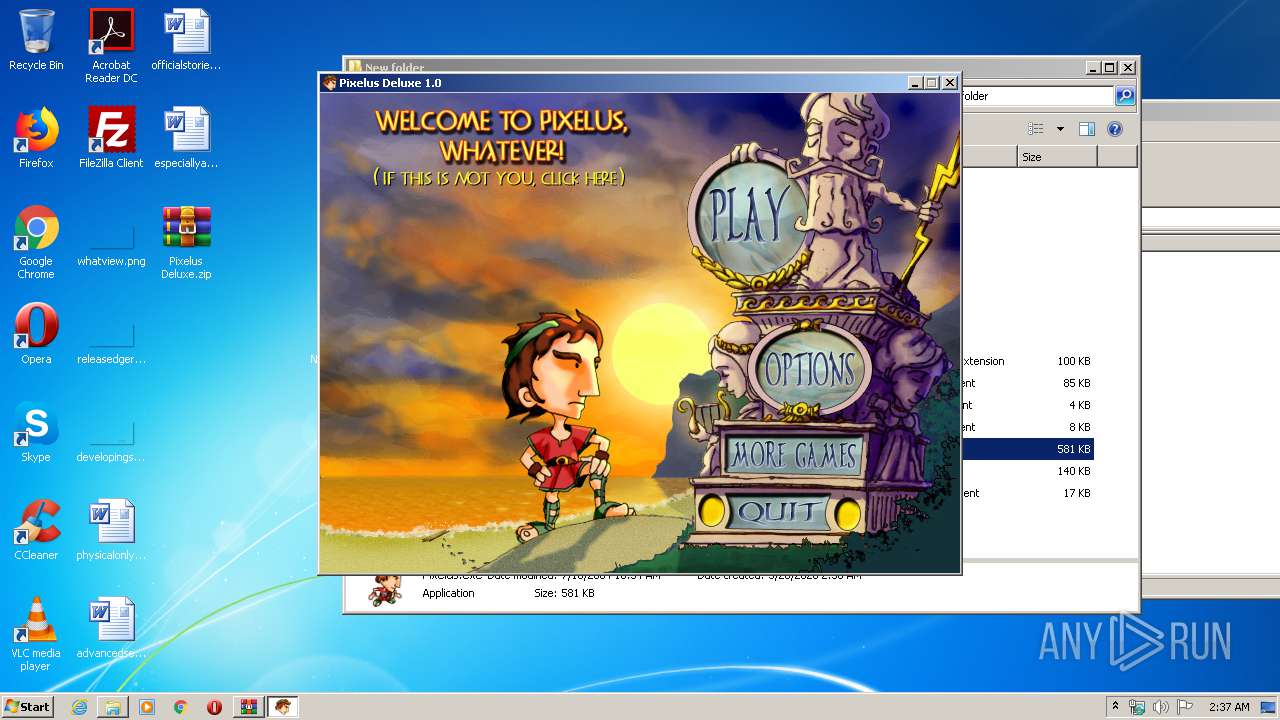
Malware analysis Pixelus Deluxe.zip Malicious activity
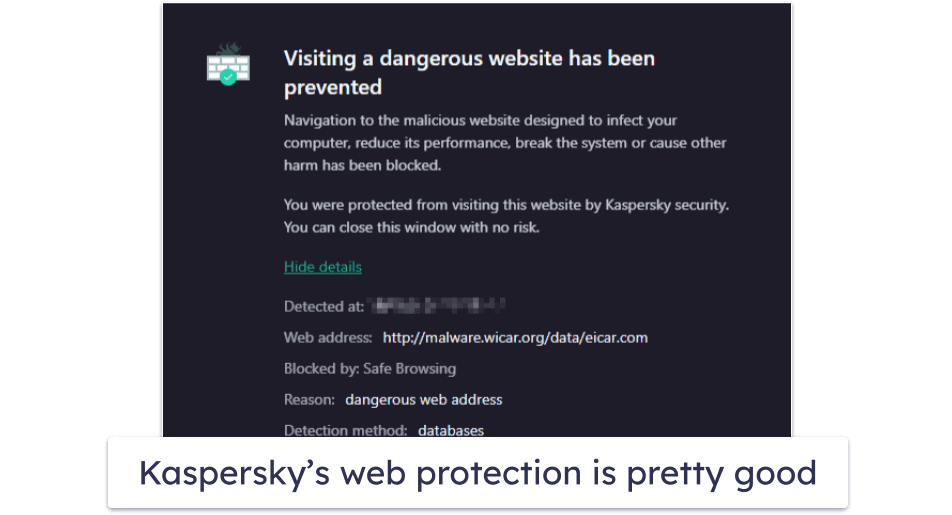
10 Best Antivirus Software in 2023: Windows, Android, iOS, Mac

UK and allies support Ukraine calling out Russia's GRU for
Malware analysis index.html Malicious activity

Routers Roasting on an Open Firewall: the KV-botnet Investigation
Recomendado para você
-
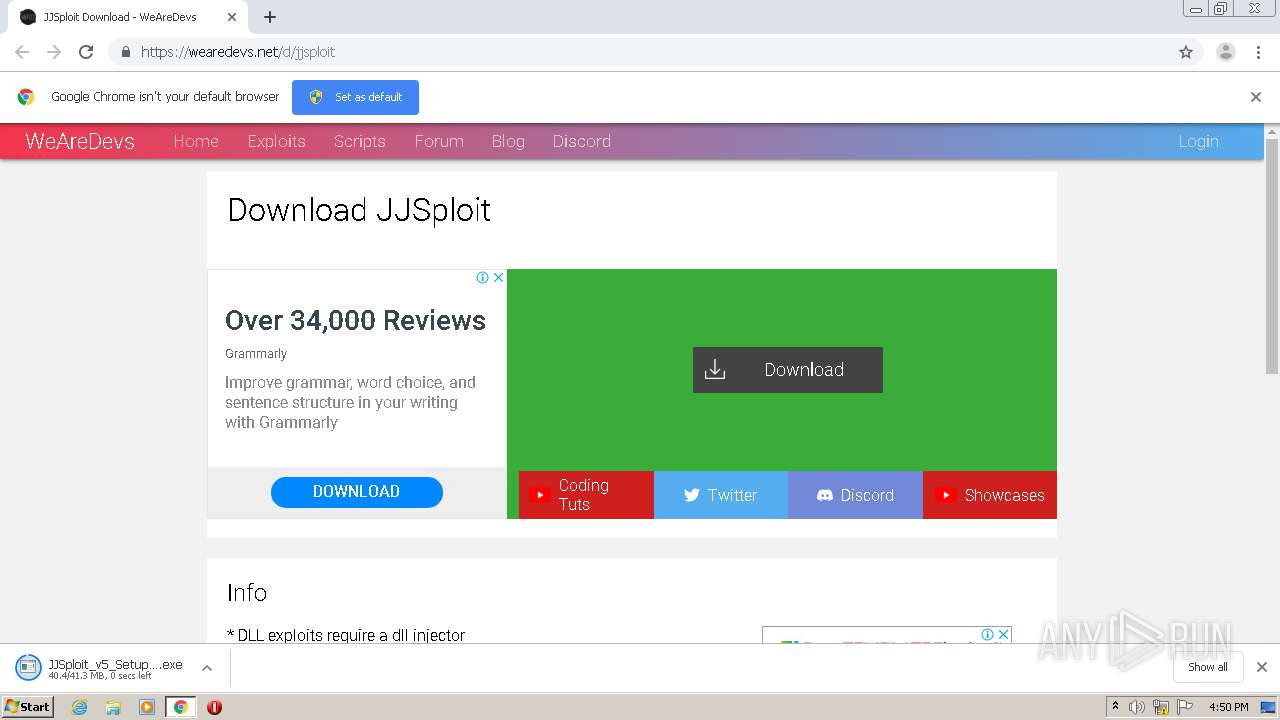
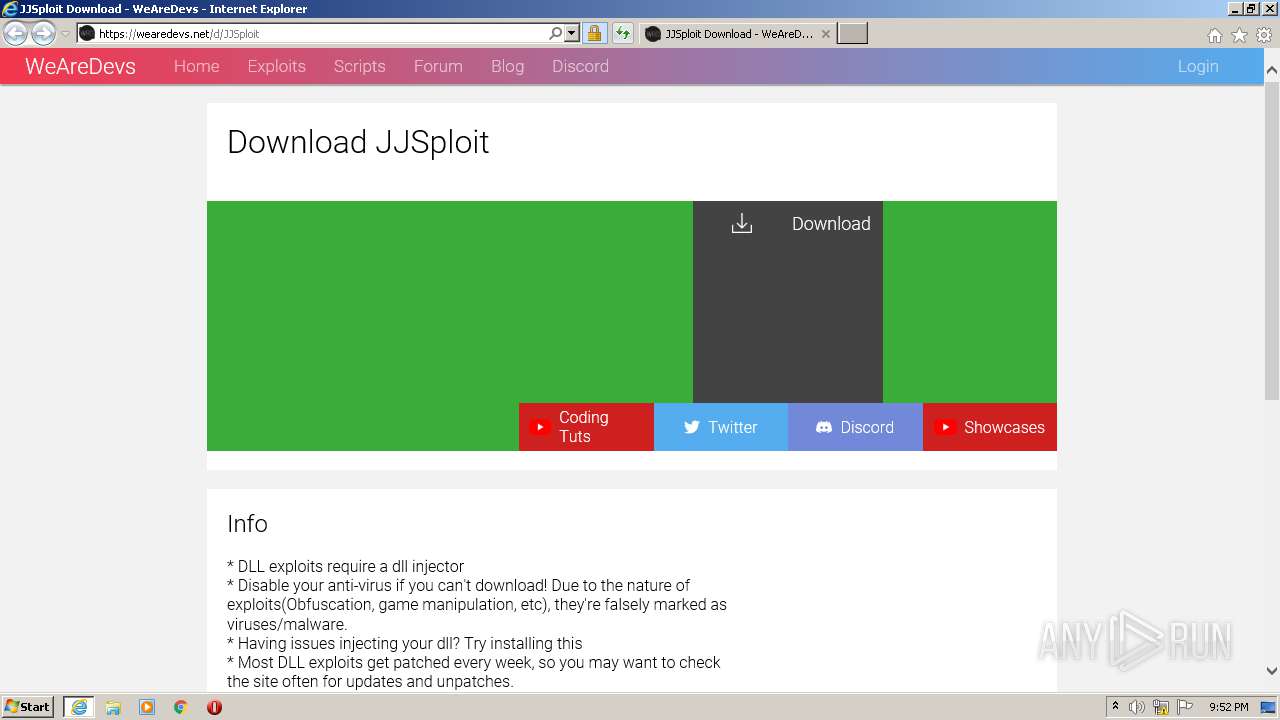
 WeAreDevs (@WeAreDevs_) / X04 abril 2025
WeAreDevs (@WeAreDevs_) / X04 abril 2025 -
 JJSploit for Roblox 7.2.1 Download For Windows PC - Softlay04 abril 2025
JJSploit for Roblox 7.2.1 Download For Windows PC - Softlay04 abril 2025 -
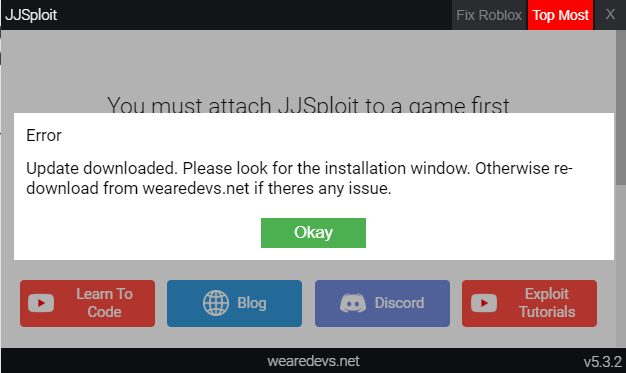 JJSploit Information WeAreDevs, 49% OFF04 abril 2025
JJSploit Information WeAreDevs, 49% OFF04 abril 2025 -
 Malware analysis Malicious activity04 abril 2025
Malware analysis Malicious activity04 abril 2025 -
 How to use lua scripts with JJ sploit (By wearedevs)04 abril 2025
How to use lua scripts with JJ sploit (By wearedevs)04 abril 2025 -
 WeAreDevs.net review pt.1 I exploits on wearedevs04 abril 2025
WeAreDevs.net review pt.1 I exploits on wearedevs04 abril 2025 -
 How to dowload and use Krnl and scripts!04 abril 2025
How to dowload and use Krnl and scripts!04 abril 2025 -
 how to execute scripts on jjsploit|TikTok Search04 abril 2025
how to execute scripts on jjsploit|TikTok Search04 abril 2025 -
how to download jj exploit roblox|TikTok Search04 abril 2025
-
roblox #fyo #hack #script #jjsploit #wearedevs Like and Comment04 abril 2025
você pode gostar
-
/i.s3.glbimg.com/v1/AUTH_bc8228b6673f488aa253bbcb03c80ec5/internal_photos/bs/2022/V/v/Jf6mAjRBKuoBNFxdWmDA/whatsapp-image-2022-12-14-at-09.08.39-1-.jpeg) Basquete Unifacisa recebe o Bauru em mais um jogo do NBB 2023/202404 abril 2025
Basquete Unifacisa recebe o Bauru em mais um jogo do NBB 2023/202404 abril 2025 -
Vibes FM 97.3 - Happy birthday @Nosaigunma1 Best wishes04 abril 2025
-
 Carros na Web Chevrolet Grand Blazer 4.2 Turbodiesel 200004 abril 2025
Carros na Web Chevrolet Grand Blazer 4.2 Turbodiesel 200004 abril 2025 -
 Boneca Bebê Reborn Olho Aberto Baby Brink Roupa Rosa Rosa - Tio Gêra04 abril 2025
Boneca Bebê Reborn Olho Aberto Baby Brink Roupa Rosa Rosa - Tio Gêra04 abril 2025 -
 A Dama de Vermelho (Portuguese Edition) eBook : Farias Borges, Elizandra : Tienda Kindle04 abril 2025
A Dama de Vermelho (Portuguese Edition) eBook : Farias Borges, Elizandra : Tienda Kindle04 abril 2025 -
 Mushoku Tensei: Jobless Reincarnation Anime Complete Settings Book04 abril 2025
Mushoku Tensei: Jobless Reincarnation Anime Complete Settings Book04 abril 2025 -
 Jogos 6º Ano - Ludo Educativo04 abril 2025
Jogos 6º Ano - Ludo Educativo04 abril 2025 -
 Ingressos à venda para Londrina Esporte Clube x Ponte Preta04 abril 2025
Ingressos à venda para Londrina Esporte Clube x Ponte Preta04 abril 2025 -
 ◓ Mangá: Pokémon Adventures (Pokémon Special)04 abril 2025
◓ Mangá: Pokémon Adventures (Pokémon Special)04 abril 2025 -
 PRE-ORDER Hell's Paradise: Jigokuraku Vibration Stars Yamada04 abril 2025
PRE-ORDER Hell's Paradise: Jigokuraku Vibration Stars Yamada04 abril 2025


