Windows Command-Line Obfuscation
Por um escritor misterioso
Last updated 14 abril 2025
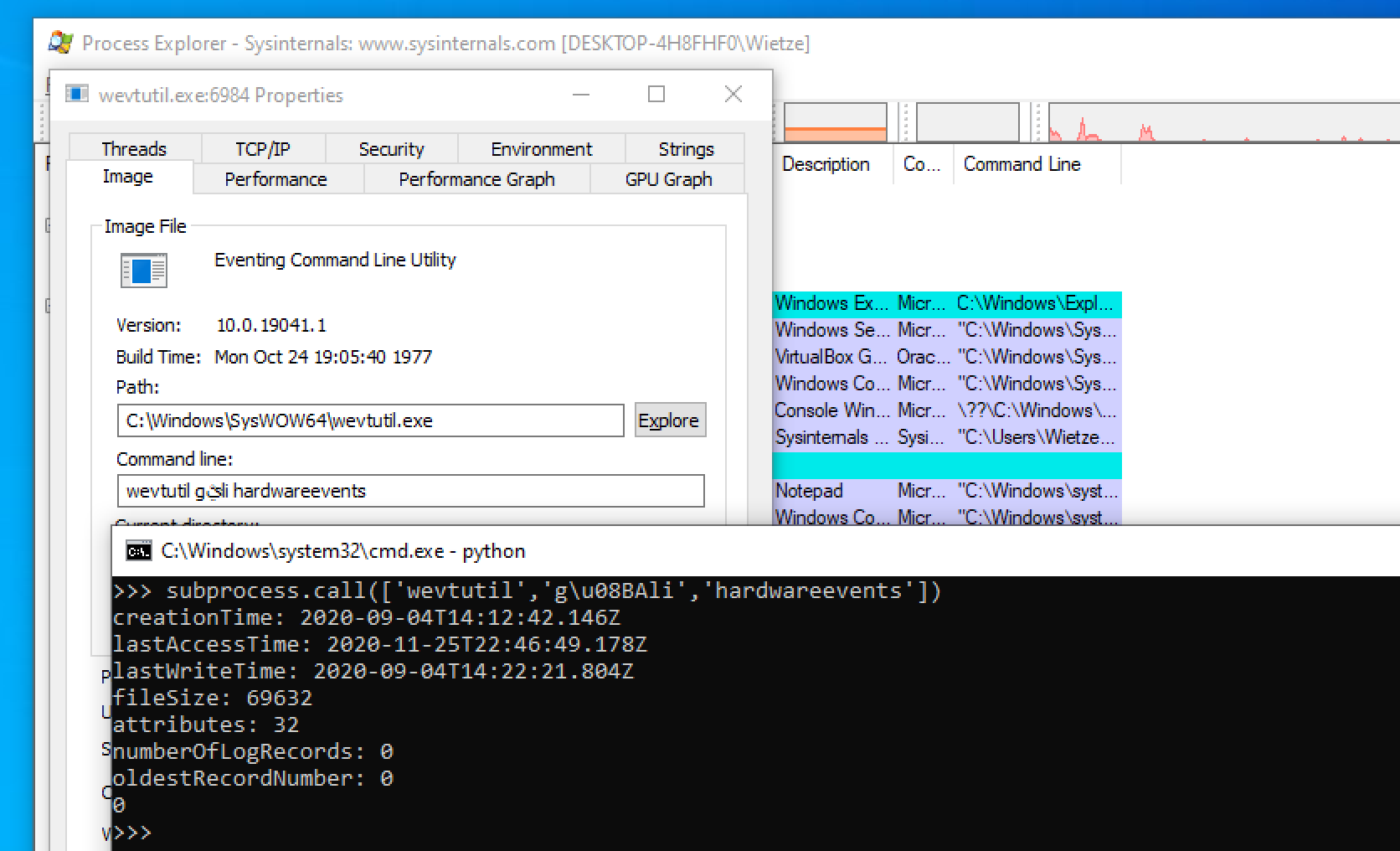
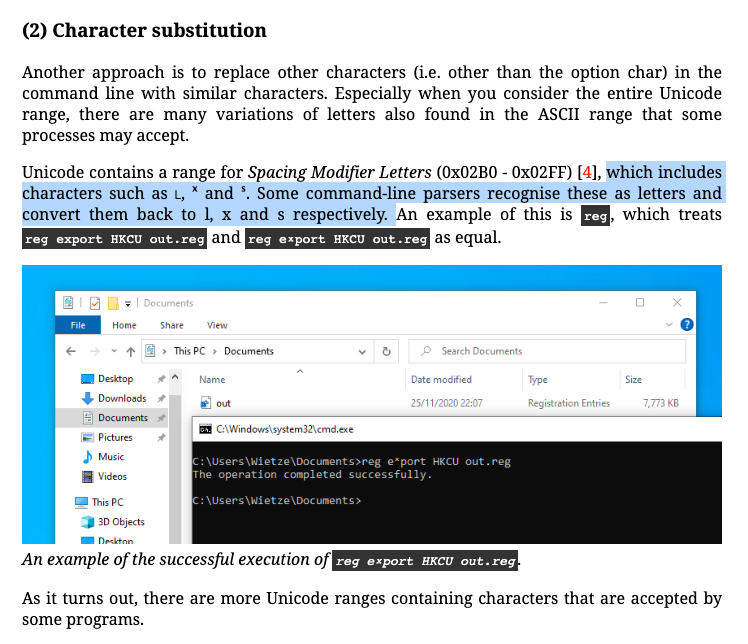
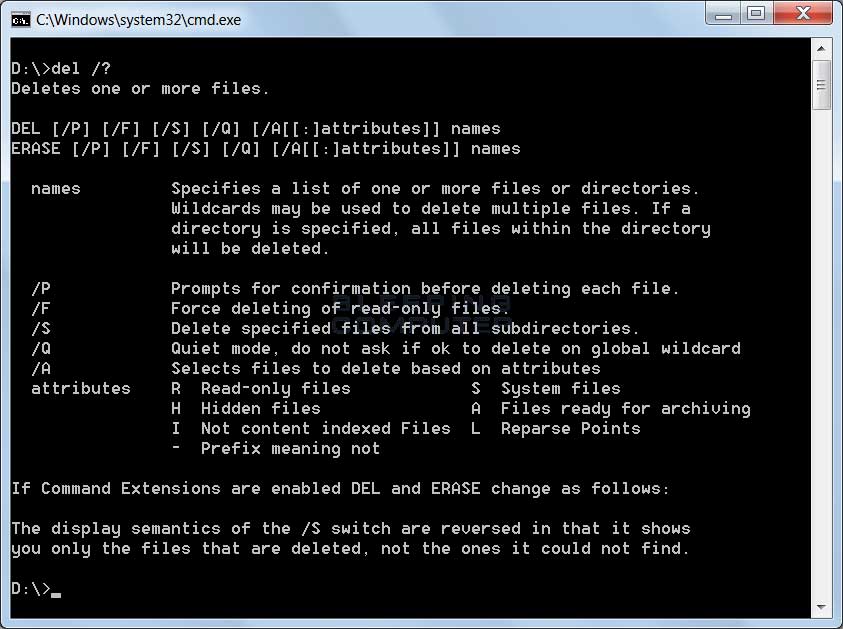
Many Windows applications have multiple ways in which the same command line can be expressed, usually for compatibility or ease-of-use reasons. As a result, command-line arguments are implemented inconsistently making detecting specific commands harder due to the number of variations. This post shows how more than 40 often-used, built-in Windows applications are vulnerable to forms of command-line obfuscation, and presents a tool for analysing other executables.
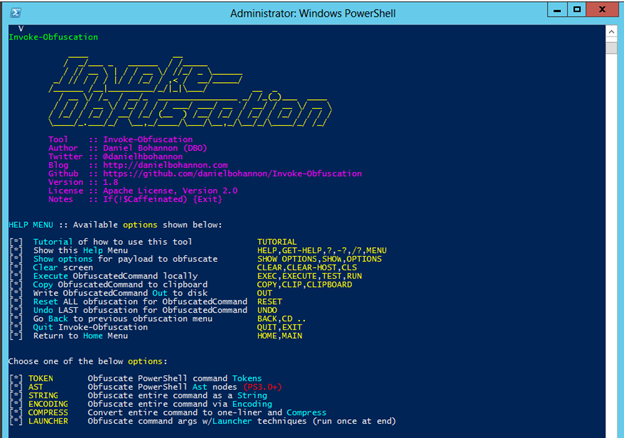
Invoke-Obfuscation — Hiding Payloads To Avoid Detection
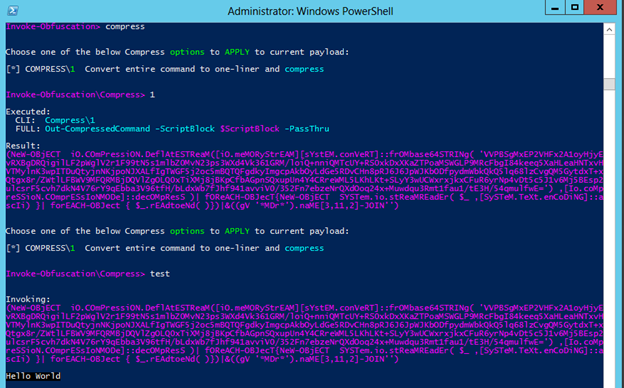
Invoke-Obfuscation — Hiding Payloads To Avoid Detection

Invoke-Obfuscation – Liam Cleary [MVP Alumni and MCT]
Florian Roth on X: Sigma rule to detect suspicious Unicode
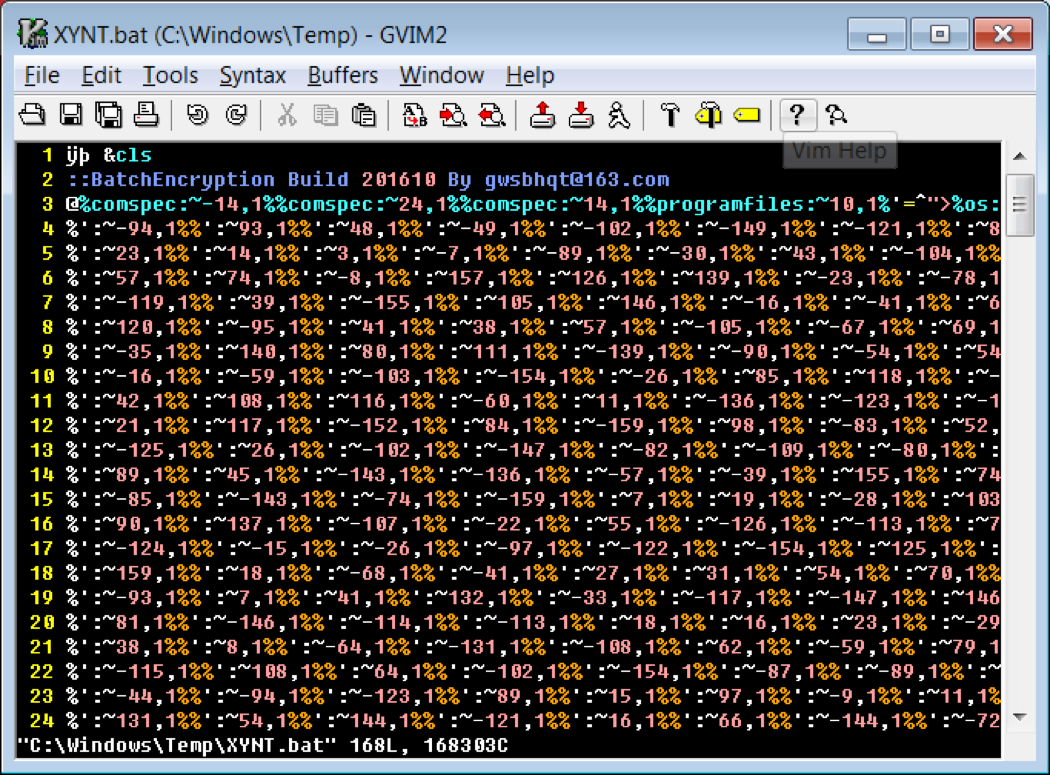
Cmd and Conquer: De-DOSfuscation with flare-qdb
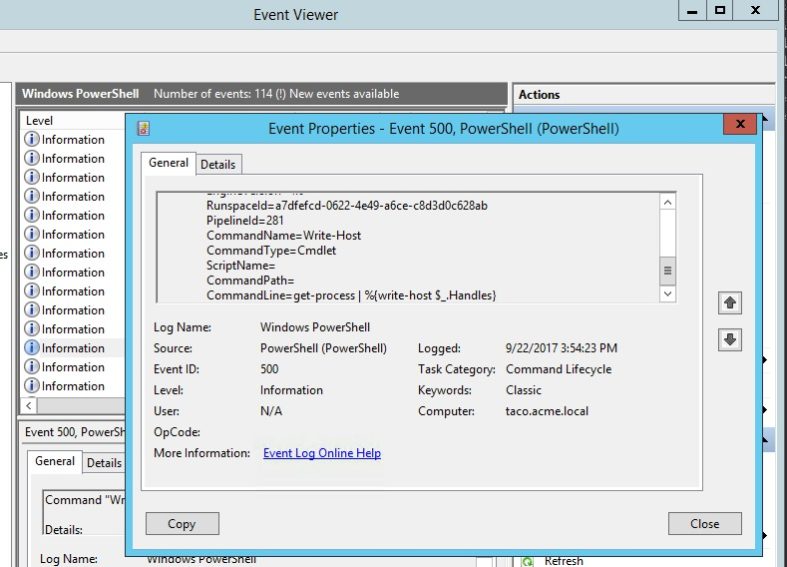
PowerShell Obfuscation: Stealth Through Confusion, Part I
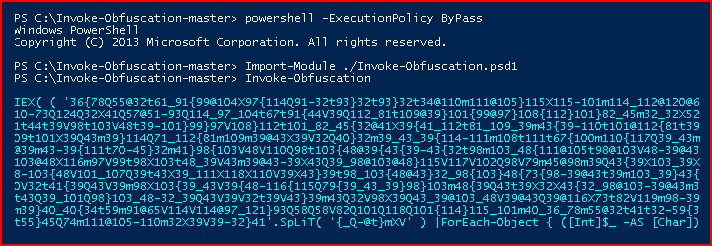
Invoke Obfuscation

Exploring Windows Command-Line Obfuscation
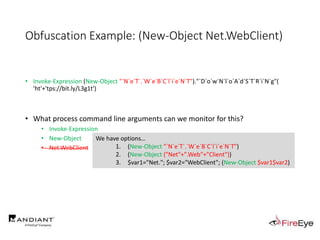
CB16] Invoke-Obfuscation: PowerShell obFUsk8tion Techniques & How

Command Line Interface — Dotfuscator Community User Guide 6.3
Recomendado para você
-
 Understanding Command Line Arguments and How to Use Them14 abril 2025
Understanding Command Line Arguments and How to Use Them14 abril 2025 -
:max_bytes(150000):strip_icc()/psexec-ipconfig-command-5c6ef8dc46e0fb0001b68174.png) PsExec: What It Is and How to Use It14 abril 2025
PsExec: What It Is and How to Use It14 abril 2025 -
 How can I run an application with arguments from Windows Explorer? - Super User14 abril 2025
How can I run an application with arguments from Windows Explorer? - Super User14 abril 2025 -
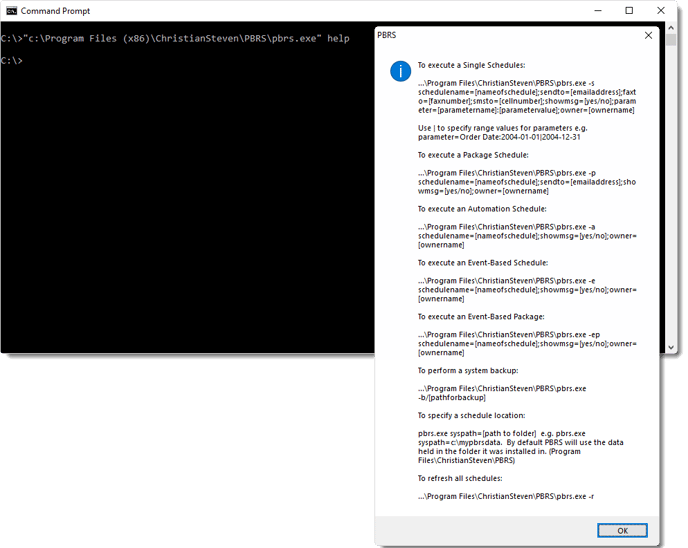 How do I use Command Line Options in PBRS?14 abril 2025
How do I use Command Line Options in PBRS?14 abril 2025 -
 Scheduling a PowerShell script… with arguments14 abril 2025
Scheduling a PowerShell script… with arguments14 abril 2025 -
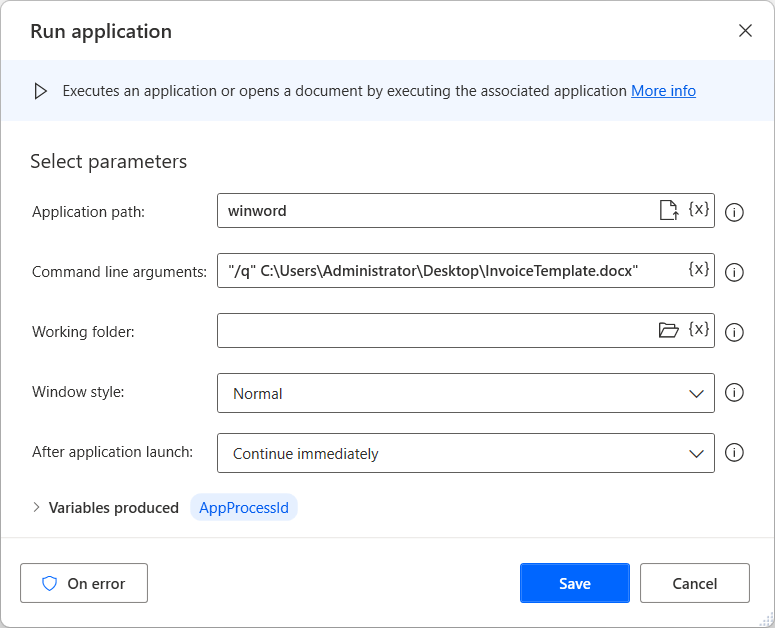 System actions reference - Power Automate14 abril 2025
System actions reference - Power Automate14 abril 2025 -
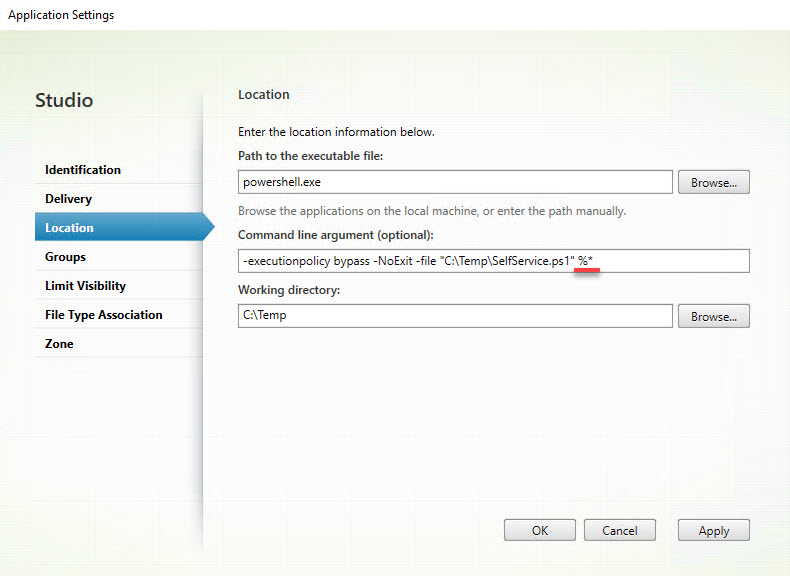 Parsing multiple parameters using the Citrix SelfService.exe14 abril 2025
Parsing multiple parameters using the Citrix SelfService.exe14 abril 2025 -
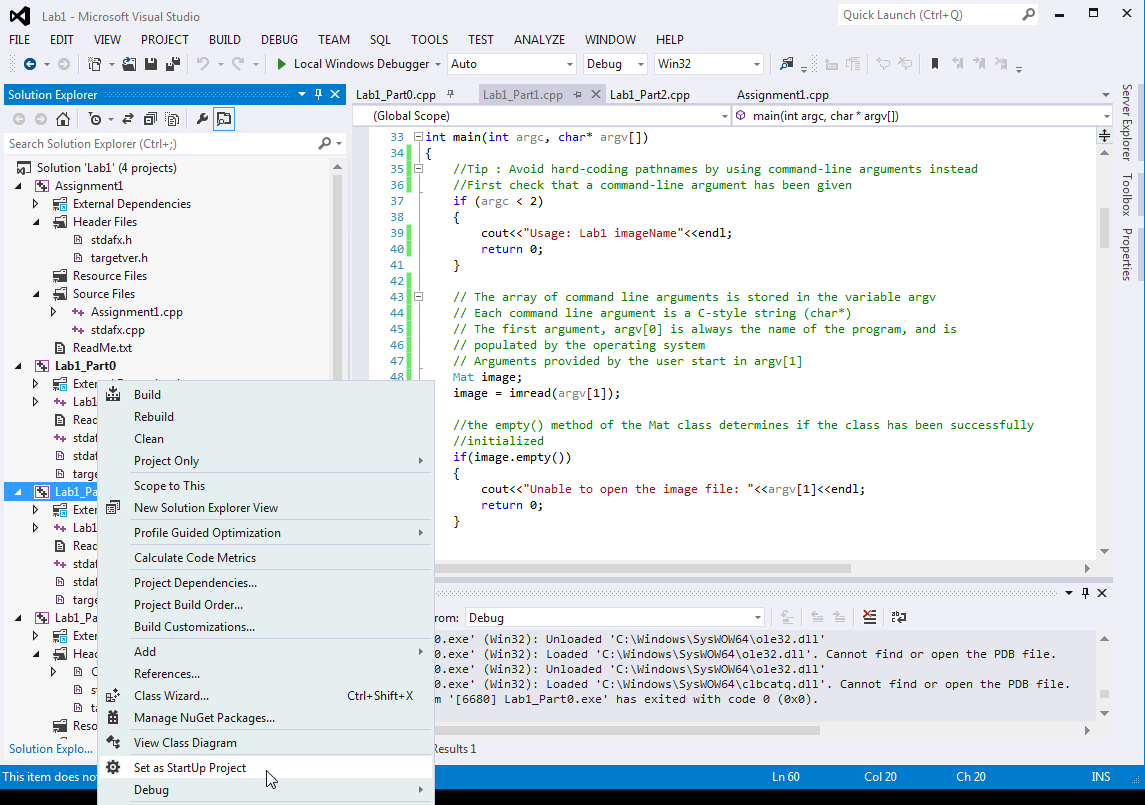 CS585 : Getting Started with Visual Studio Tutorial: Diane H14 abril 2025
CS585 : Getting Started with Visual Studio Tutorial: Diane H14 abril 2025 -
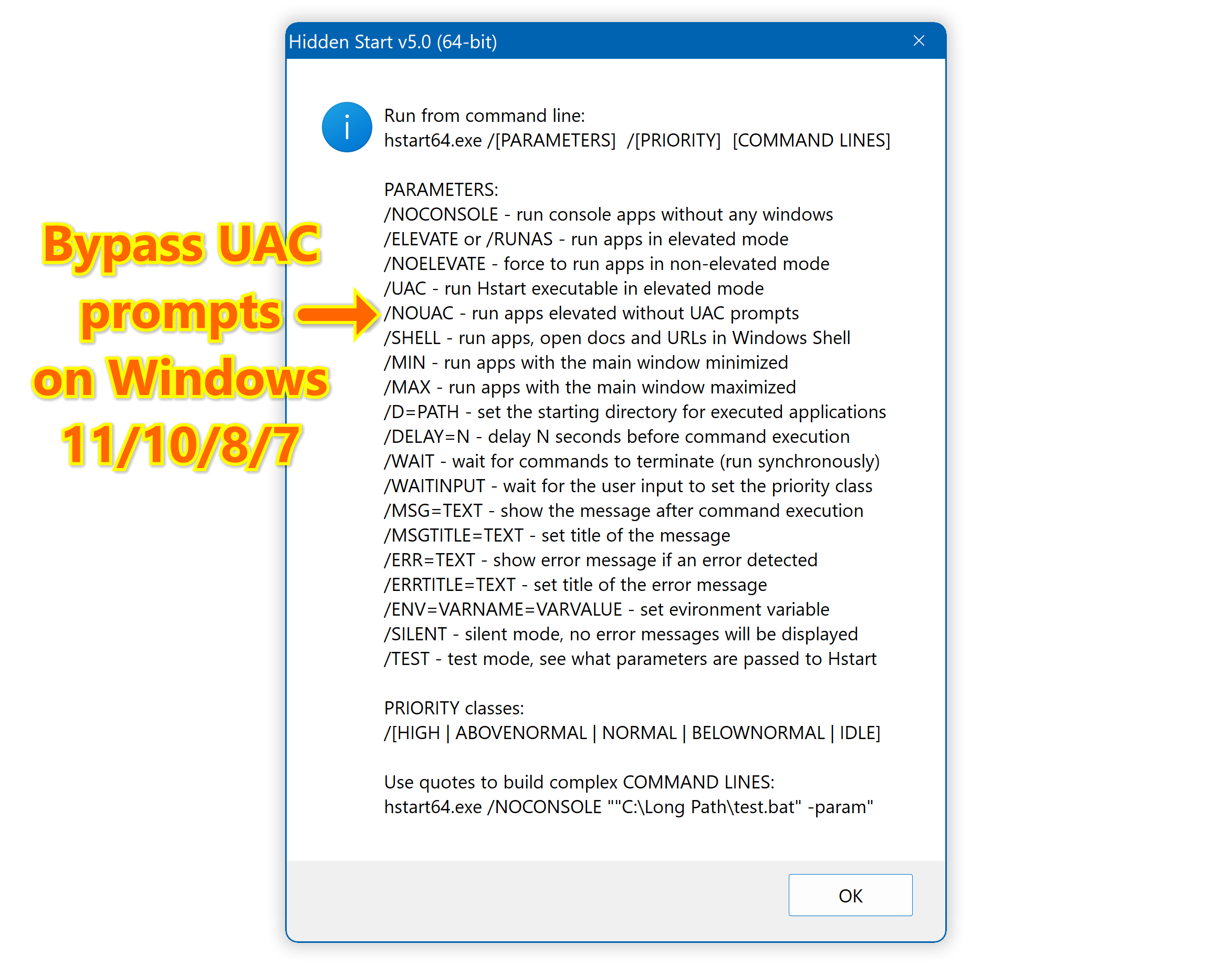 Hidden Start - Bypass UAC, Hide Console Windows, Run Apps in the14 abril 2025
Hidden Start - Bypass UAC, Hide Console Windows, Run Apps in the14 abril 2025 -
 Installing SQL Server from Command line(CMD) – MSSQLTREK14 abril 2025
Installing SQL Server from Command line(CMD) – MSSQLTREK14 abril 2025
você pode gostar
-
 Quadro de xadrez e diferentes peças de xadrez14 abril 2025
Quadro de xadrez e diferentes peças de xadrez14 abril 2025 -
 Free Vector Vintage coffee types concept14 abril 2025
Free Vector Vintage coffee types concept14 abril 2025 -
 Attack on Titan: Parte 3 da temporada final estreia dublado % %14 abril 2025
Attack on Titan: Parte 3 da temporada final estreia dublado % %14 abril 2025 -
 5 jogos para Android baseados em memes14 abril 2025
5 jogos para Android baseados em memes14 abril 2025 -
 Undertale / Nightmare Fuel - TV Tropes14 abril 2025
Undertale / Nightmare Fuel - TV Tropes14 abril 2025 -
 9 Things We'll PROBABLY See in Forza Horizon 6!14 abril 2025
9 Things We'll PROBABLY See in Forza Horizon 6!14 abril 2025 -
 Rebecca → EDENS ZERO Anime eden, Black lagoon anime, Anime14 abril 2025
Rebecca → EDENS ZERO Anime eden, Black lagoon anime, Anime14 abril 2025 -
 Using the crucifix on rush by Brotherlandball on DeviantArt14 abril 2025
Using the crucifix on rush by Brotherlandball on DeviantArt14 abril 2025 -
 Vestido roxo princesa Black Friday Casas Bahia14 abril 2025
Vestido roxo princesa Black Friday Casas Bahia14 abril 2025 -
 General/Other - Kotal Kahn - Kotal Khan : Shao Khan or Relatives?14 abril 2025
General/Other - Kotal Kahn - Kotal Khan : Shao Khan or Relatives?14 abril 2025