How hackers use idle scans in port scan attacks
Por um escritor misterioso
Last updated 27 março 2025
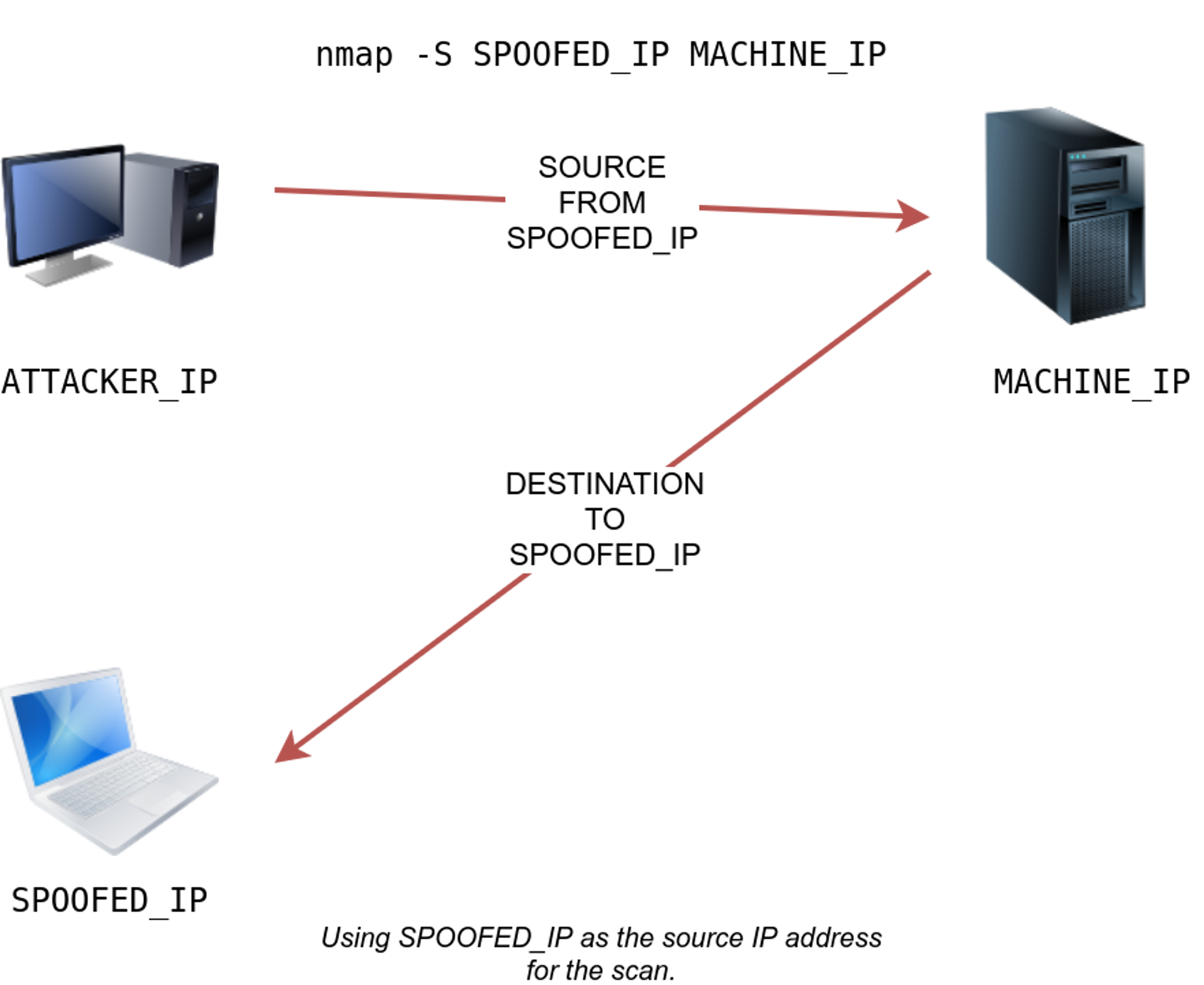
Hackers employ a variety of port scan attacks to gain entry into an enterprise network. Idle scans are a popular method to mask the hacker
Hackers exploit port scan attacks to mask their identities before launching an attack. One of their favorites: the idle scan.
Hackers exploit port scan attacks to mask their identities before launching an attack. One of their favorites: the idle scan.
Hacking Reconnaissance: Finding Vulnerabilities in Your Target Using Nmap « Null Byte :: WonderHowTo
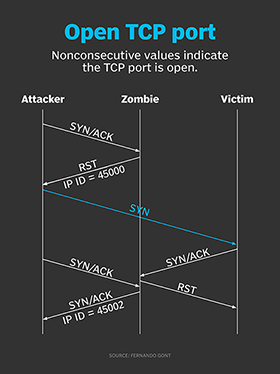
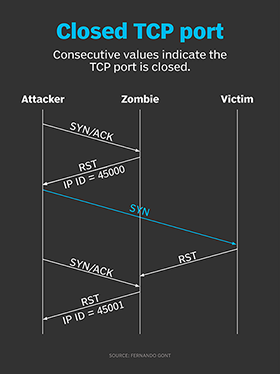
How hackers use idle scans in port scan attacks
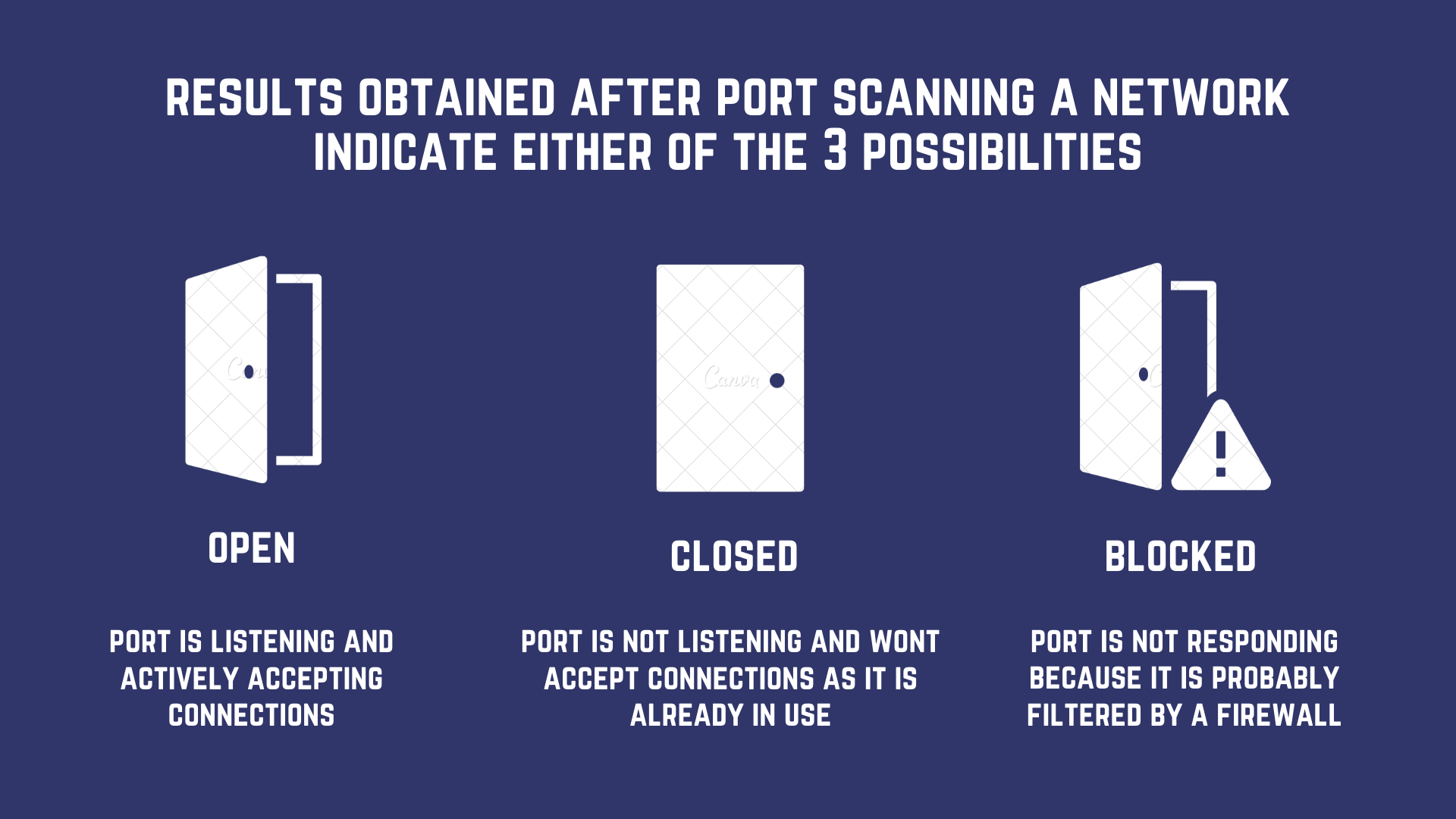
Port Scanning based Attacks

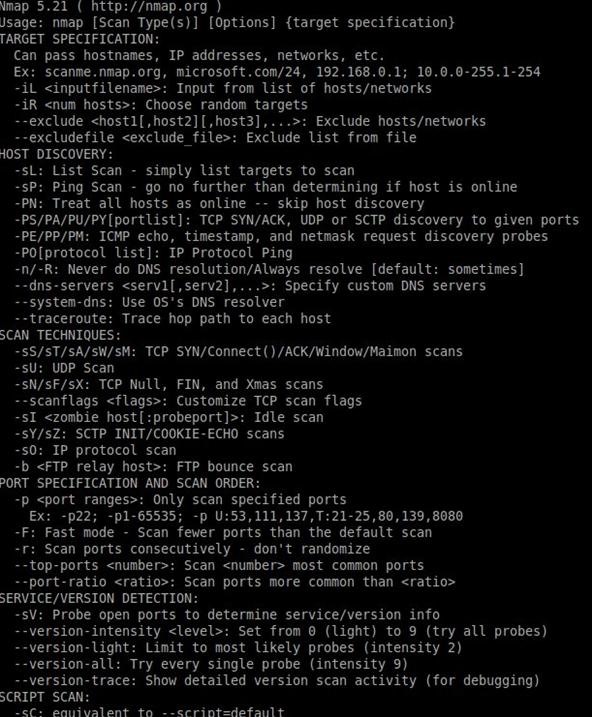
A Complete Guide to Nmap, Nmap Tutorial
PPT - Port Scanning PowerPoint Presentation, free download - ID:1577632

What is Idle Scan? ICterra Information and Communication Technologies
Performing an Idle Zombie Scan Nmap
The Ultimate Guide to Port Scanning using Nmap

Port scanners
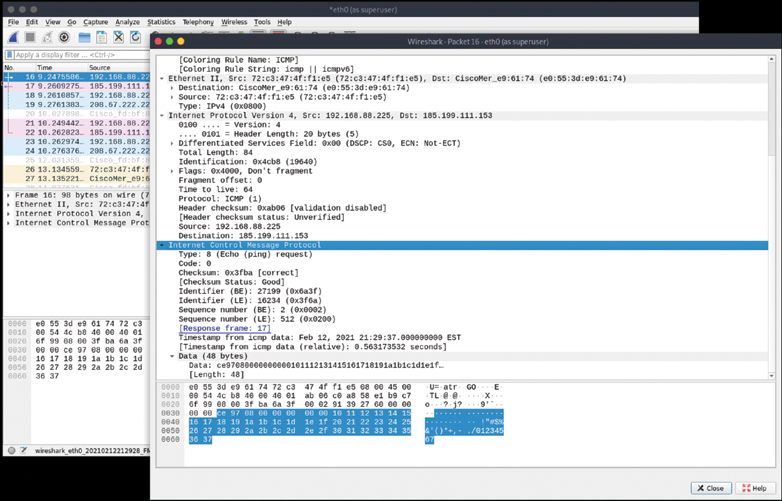
Scanning, Footprinting, Reconnaissance, and Scanning

What Is an Idle Scan? (with pictures)
Recomendado para você
-
 How to extract your outside IP address - What's My IP - IP Chicken - IP Monkey27 março 2025
How to extract your outside IP address - What's My IP - IP Chicken - IP Monkey27 março 2025 -
SOLVED] Port Forwarding for IP Camera not working27 março 2025
-
 8 Sites That Show Your IP Address –27 março 2025
8 Sites That Show Your IP Address –27 março 2025 -
 Proxying Burp Traffic through VPS using SOCKS Proxy, by Nishith K27 março 2025
Proxying Burp Traffic through VPS using SOCKS Proxy, by Nishith K27 março 2025 -
 What is port scanning and how does it work?27 março 2025
What is port scanning and how does it work?27 março 2025 -
 Brisson teaches internet safety - Munising Beacon27 março 2025
Brisson teaches internet safety - Munising Beacon27 março 2025 -
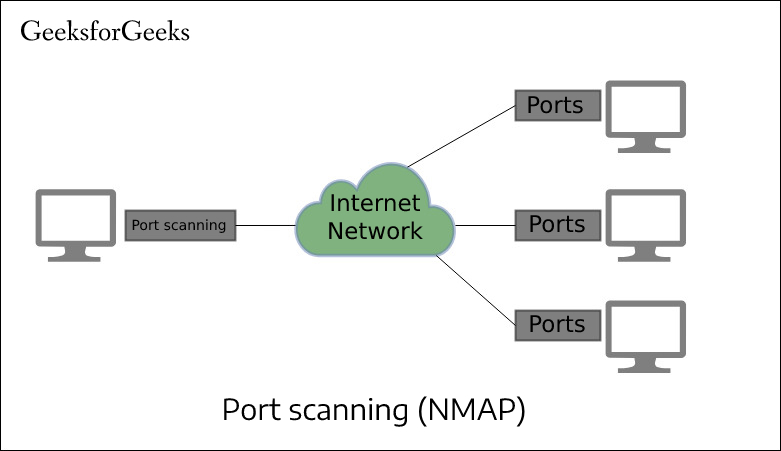 Port Scan in Ethical Hacking - GeeksforGeeks27 março 2025
Port Scan in Ethical Hacking - GeeksforGeeks27 março 2025 -
 Test Your Router27 março 2025
Test Your Router27 março 2025 -
 10 Best Port Scanner Tools for Network Security - Geekflare27 março 2025
10 Best Port Scanner Tools for Network Security - Geekflare27 março 2025 -
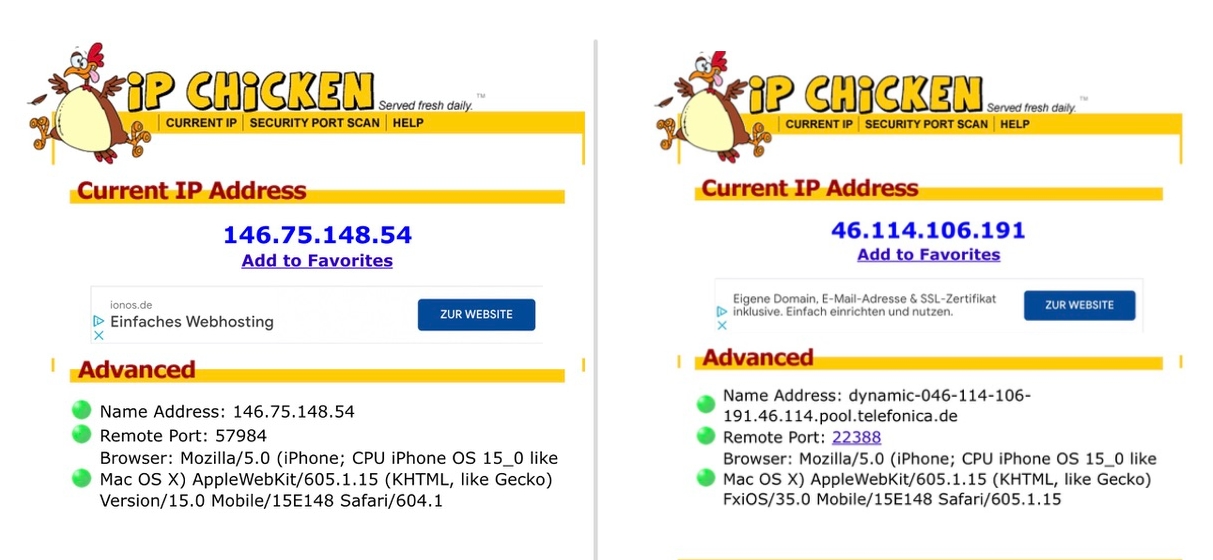 iOS 15: Hide IP address in Safari27 março 2025
iOS 15: Hide IP address in Safari27 março 2025
você pode gostar
-
 B L M 🖤. on X: all drawings that were found within Justin Bieber's music video for the song “where are you now “, Keep in mind this song was made 427 março 2025
B L M 🖤. on X: all drawings that were found within Justin Bieber's music video for the song “where are you now “, Keep in mind this song was made 427 março 2025 -
stitch with @karmabl0ck #scptiktok #scp #scpfoundation #drsherman #si, scp-66627 março 2025
-
Media - Max Holloway got promoted to brown belt in BJJ, Sherdog Forums27 março 2025
-
 26 ideias de Natasha panda garotas gamer, panda, panda desenho27 março 2025
26 ideias de Natasha panda garotas gamer, panda, panda desenho27 março 2025 -
 MEDO - Aprenda a Enfrentar - Use a mente27 março 2025
MEDO - Aprenda a Enfrentar - Use a mente27 março 2025 -
 Como fazer boca realista·(Tutorial)·Gacha Clube·27 março 2025
Como fazer boca realista·(Tutorial)·Gacha Clube·27 março 2025 -
 CEO 2023 - Qanba Drone27 março 2025
CEO 2023 - Qanba Drone27 março 2025 -
 Conta no roblox27 março 2025
Conta no roblox27 março 2025 -
Copo Térmico para Cerveja com Tampa em Inox 473ml Stanley Preto - Spicy27 março 2025
-
 EVOLUÇÃO DO MARIO NOS GAMES (ORDEM CRONOLÓGICA)27 março 2025
EVOLUÇÃO DO MARIO NOS GAMES (ORDEM CRONOLÓGICA)27 março 2025

