Operation Exchange Marauder: Active Exploitation of Multiple Zero-Day Microsoft Exchange Vulnerabilities
Por um escritor misterioso
Last updated 11 abril 2025
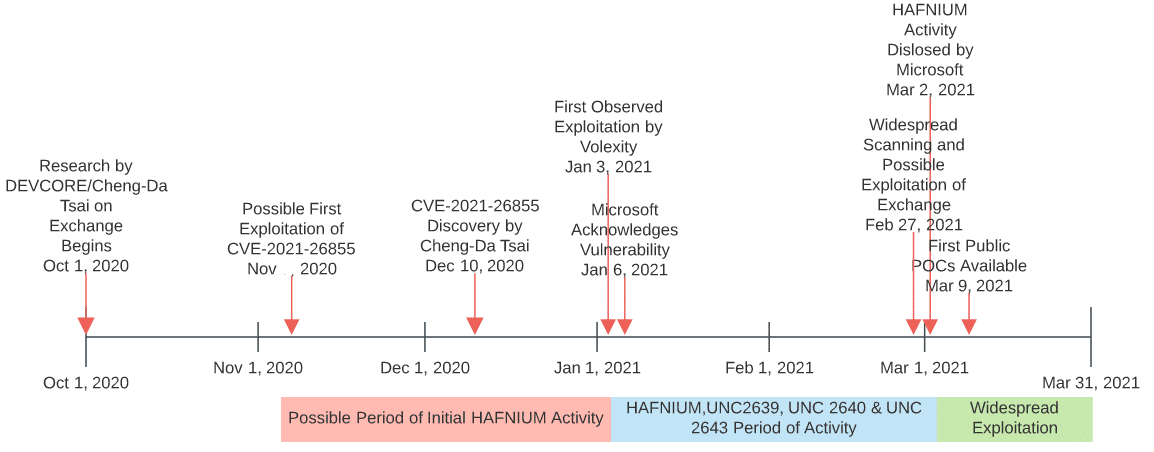
[UPDATE] March 8, 2021 – Since original publication of this blog, Volexity has now observed that cyber espionage operations using the SSRF vulnerability CVE-2021-26855 started occurring on January 3, 2021, three days earlier than initially posted. Volexity is seeing active in-the-wild exploitation of multiple Microsoft Exchange vulnerabilities used to steal e-mail and compromise networks. These attacks appear to have started as early as January 6, 2021. In January 2021, through its Network Security Monitoring service, Volexity detected anomalous activity from two of its customers' Microsoft Exchange servers. Volexity identified a large amount of data being sent to IP addresses it believed were not tied to legitimate users. A closer inspection of the IIS logs from the Exchange servers revealed rather alarming results. The logs showed inbound POST requests to valid files associated with images, JavaScript, cascading style sheets, and fonts used by Outlook Web Access (OWA). It was initially suspected the […]

Zero Day Vulnerabilities Discovered in all Versions of Microsoft Exchange Server
Examining Exchange Exploitation and its Lessons for Defenders - DomainTools

Customer Guidance for Reported Zero-day Vulnerabilities in Microsoft Exchange Server, MSRC Blog

Finding Proxylogon and Related Microsoft Exchange Vulnerabilities: How Tenable Can Help - Blog
Attackers Exploit New Zero-Day ProxyNotShell Vulnerabilities on Exchange Server

New Microsoft Exchange zero-days allow RCE, data theft attacks
Microsoft Exchange Server Zero-Day Vulnerabilities Exploited

Exploit Archives

Healthcare's Microsoft Exchange Critical Exposure - Meditology Services
MSFT Vulnerabilities (CVE-2022-41040 & 2022-41082)
Hunting down Microsoft Exchange 0-day
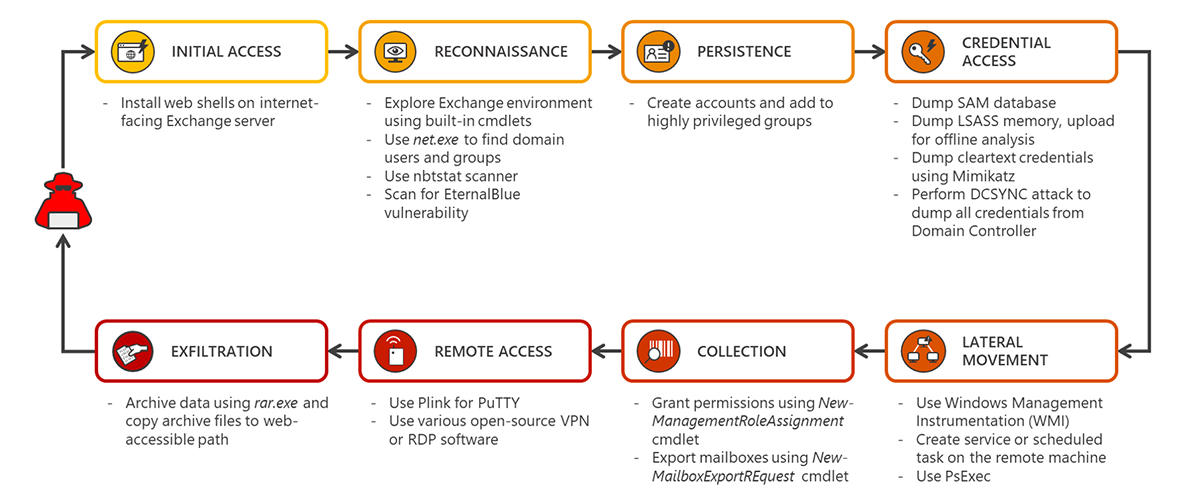
Tactics, Techniques, and Procedures (TTPs) Used by HAFNIUM to Target Microsoft Exchange Servers

Operation Exchange Marauder: Active Exploitation of Multiple Zero-Day Microsoft Exchange Vulnerabilities
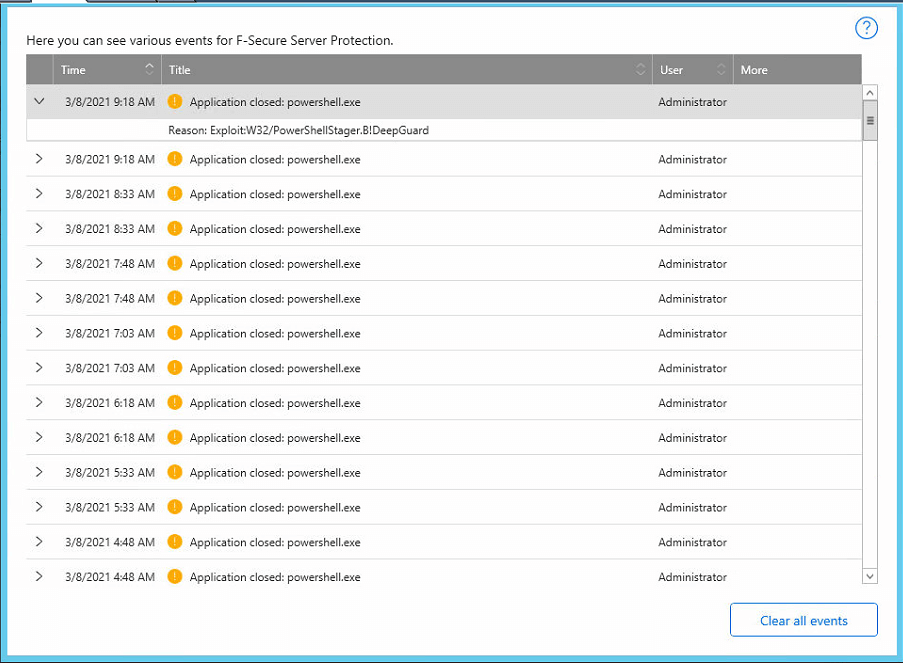
Defending Exchange servers under attack
Recomendado para você
-
 Counter-Strike Xbox Edition, Counter-Strike Wiki11 abril 2025
Counter-Strike Xbox Edition, Counter-Strike Wiki11 abril 2025 -
 Game Counter Strike Condition Zero 2.0 - Colaboratory11 abril 2025
Game Counter Strike Condition Zero 2.0 - Colaboratory11 abril 2025 -
 CSCZ server Host - CSCZ Server Mieten - VeryGames11 abril 2025
CSCZ server Host - CSCZ Server Mieten - VeryGames11 abril 2025 -
Guide – How To Start – Counter-Strike Condition Zero on Linux Stream 811 abril 2025
-
 Counter-Strike 1.6, frag, Counter-Strike: Source, game Server11 abril 2025
Counter-Strike 1.6, frag, Counter-Strike: Source, game Server11 abril 2025 -
 macos - Counter Strike Condition Zero Mac Dedicated Server with Steam - Arqade11 abril 2025
macos - Counter Strike Condition Zero Mac Dedicated Server with Steam - Arqade11 abril 2025 -
Steam Community :: Screenshot :: Counter-Strike: Condition Zero11 abril 2025
-
![Condition-Zero: Dark Winter (Mission [1] blockout teaser) video](https://media.moddb.com/cache/images/mods/1/60/59884/thumb_620x2000/deleted-scenes-dark-winter-mission-1-blockout-teaser.mp4.jpg) Condition-Zero: Dark Winter (Mission [1] blockout teaser) video11 abril 2025
Condition-Zero: Dark Winter (Mission [1] blockout teaser) video11 abril 2025 -
 Counter-Strike: Condition Zero - Deleted Scenes (GO) Ritual Missions #111 abril 2025
Counter-Strike: Condition Zero - Deleted Scenes (GO) Ritual Missions #111 abril 2025 -
 How to Play CounterStrike Condition Zero and 1.6 Multiplayer with Friends11 abril 2025
How to Play CounterStrike Condition Zero and 1.6 Multiplayer with Friends11 abril 2025
você pode gostar
-
 Attack with Caro-Kann Exchange Variation11 abril 2025
Attack with Caro-Kann Exchange Variation11 abril 2025 -
 Tekken 8 Guest Characters: Featuring Dante from the DMC Series11 abril 2025
Tekken 8 Guest Characters: Featuring Dante from the DMC Series11 abril 2025 -
 Kit 5 Livros, Ataque dos Titãs, Vol.1 ao Vol.511 abril 2025
Kit 5 Livros, Ataque dos Titãs, Vol.1 ao Vol.511 abril 2025 -
 Red Dead Redemption 2 - PS5 - Primária - Edição Padrão - GameShopp11 abril 2025
Red Dead Redemption 2 - PS5 - Primária - Edição Padrão - GameShopp11 abril 2025 -
 scarlet witch app icons|TikTok Search11 abril 2025
scarlet witch app icons|TikTok Search11 abril 2025 -
 Kylie Cammy cosplay11 abril 2025
Kylie Cammy cosplay11 abril 2025 -
 SPOILERS! - Ultra Sun & Ultra Moon New Pokemon/Moves Info11 abril 2025
SPOILERS! - Ultra Sun & Ultra Moon New Pokemon/Moves Info11 abril 2025 -
 A TERCEIRA TEMPORADA DA SÉRIE DE COMÉDIA MAX ORIGINAL, 'THE OTHER TWO', JÁ ESTÁ DISPONÍVEL NA HBO MAX em 202311 abril 2025
A TERCEIRA TEMPORADA DA SÉRIE DE COMÉDIA MAX ORIGINAL, 'THE OTHER TWO', JÁ ESTÁ DISPONÍVEL NA HBO MAX em 202311 abril 2025 -
 Carlsen-Anand 2014, 4: Not good enough11 abril 2025
Carlsen-Anand 2014, 4: Not good enough11 abril 2025 -
 nozorrra — yes-i-love-dreaming: Haru Nonaka / Yesterday wo11 abril 2025
nozorrra — yes-i-love-dreaming: Haru Nonaka / Yesterday wo11 abril 2025
